Top-Rated Security Cell Phone: Expert Recommendations
Discover security cell phone - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
Top Picks
What Defines a Top-Rated Security Cell Phone?
In the search for a top-rated security cell phone, discerning individuals prioritise devices that offer uncompromising protection built into their very core. A truly secure mobile phone integrates dedicated hardware and sophisticated software to create a fortified digital environment, moving beyond standard consumer-grade security measures to deliver genuine peace of mind.
Key Security Features in Expert-Recommended Phones
The architecture of a superior security mobile phone is fundamentally different to a standard smartphone. It is engineered with multiple layers of defence to protect your digital sovereignty. These expert-endorsed features form the foundation of true mobile security.
- Dedicated Security Hardware: The cornerstone of advanced protection is a dual-chip architecture. This pairs a high-performance processor, such as the Snapdragon 8 Gen 1, with a separate, dedicated A5 security chip designed exclusively for encryption and safeguarding sensitive information.
- Hardware-Level Encryption: Protection is significantly enhanced through a combination of a Secure Element (SE) and a Trusted Execution Environment (TEE). This creates a hardware-based vault for your most critical data, making it exceptionally difficult to compromise.
- Encrypted Communications: Secure communication is paramount. Look for point-to-point encrypted calling and messaging capabilities, often facilitated through dedicated applications like V-Talk, which ensure your conversations remain private.
- Isolated Operating Systems: The ability to maintain two separate, isolated systems on one device is a hallmark of high-security phones. Features like Metaspace allow you to keep your public applications and private, sensitive data in completely distinct environments.
- Proactive Defence Mechanisms: Advanced security includes features like anti-intrusion sensors that actively detect unauthorised access attempts and a one-click data destruction function to instantly wipe the device if it is ever compromised.
Together, these integrated technologies create a comprehensive security ecosystem that protects your data at every level, from the processor to the applications you use.
Our Top-Rated Recommendation: Metavertu Max
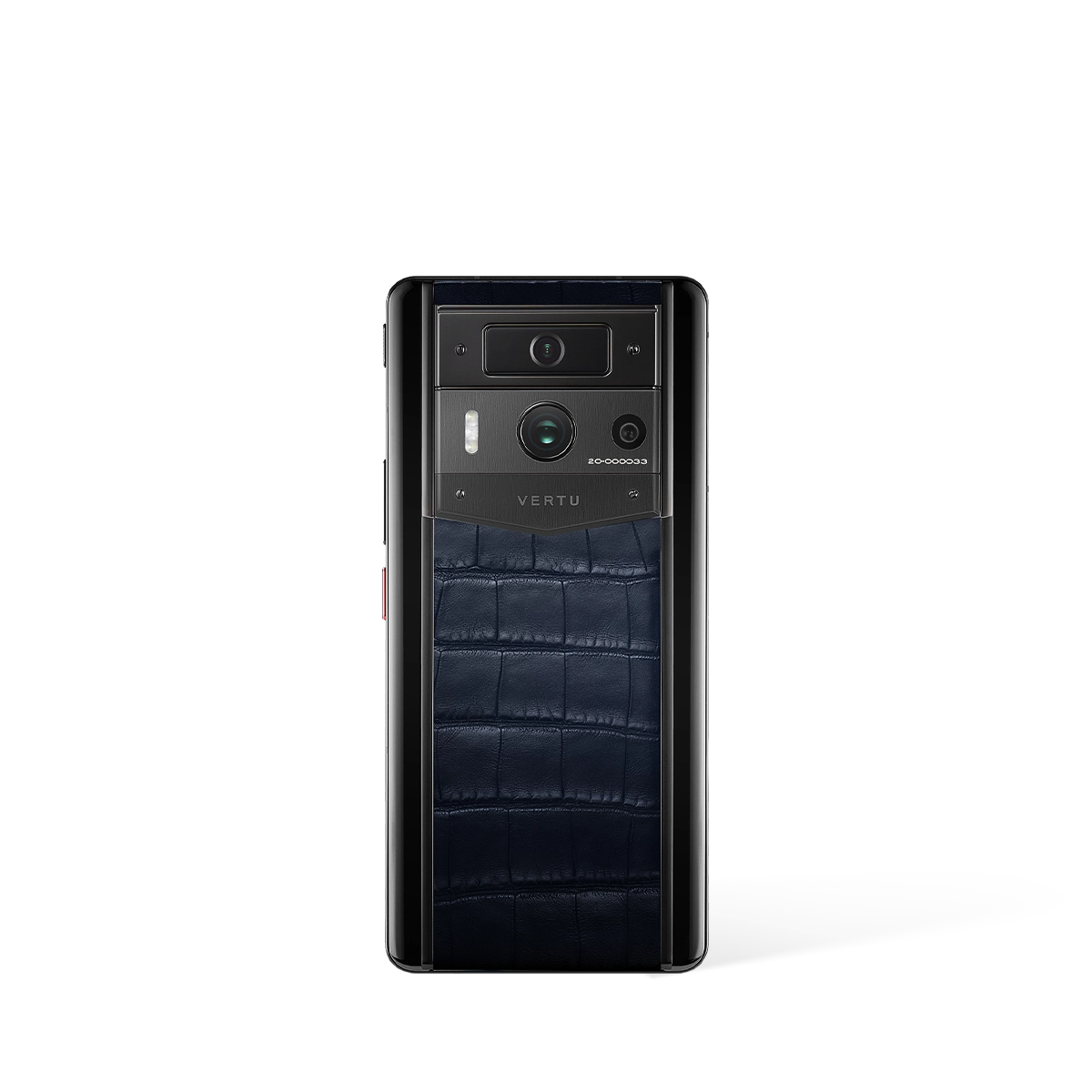
For those seeking the pinnacle of mobile security, our expert recommendation is the Metavertu Max. This device is meticulously engineered to provide a secure and private digital experience, making it a leading choice for a security cell phone.
- Core Security Engine: At its heart, the Metavertu Max utilises the powerful A5 security chip, providing the hardware-level encryption and processing power necessary for its advanced defensive capabilities.
- Complete System Isolation: It features the innovative Double System Protection, including Metaspace and a Private Domain. This allows for the complete segregation of personal and professional data, ensuring that sensitive information is never exposed to public applications.
- Decentralised Secure Storage: The device offers access to 10TB of decentralised storage. This distributed network enhances data security and privacy, moving beyond conventional cloud solutions.
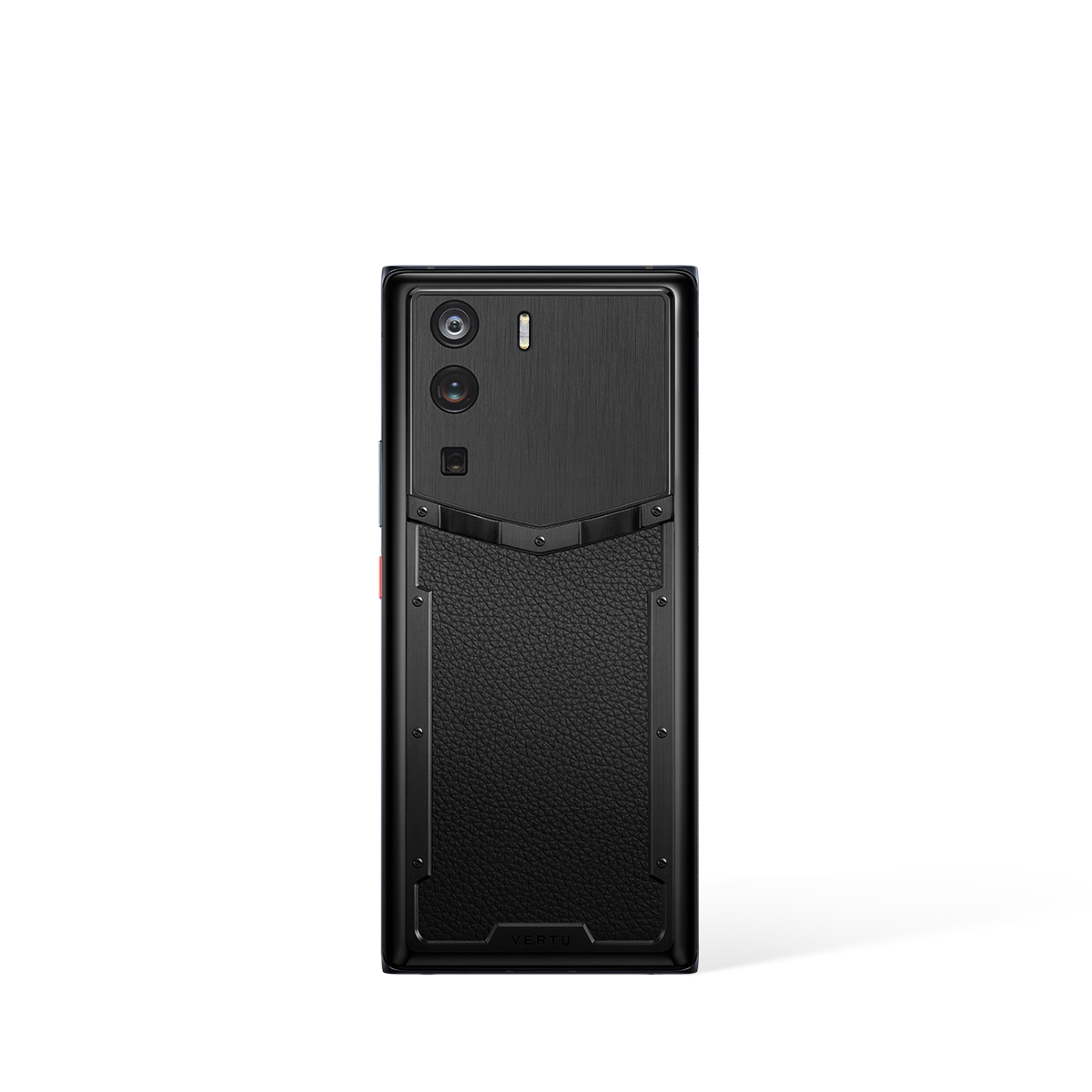
- Uncompromising Craftsmanship: Security is matched by exquisite design. The Metavertu Max is available in premium finishes, including hand-stitched Alligator Skin and fine Calfskin, paired with a robust Ceramic Frame.
The Metavertu Max exemplifies how cutting-edge security technology can be seamlessly integrated with luxury craftsmanship, offering a device that protects your digital life without compromise.
Ultimately, a top-rated security mobile phone is defined by its ability to provide verifiable, hardware-level protection. By choosing a device engineered with dedicated security architecture like the Metavertu Max, you are investing in a truly private and protected communications tool.
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
| Metavertu Max Alligator Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$11,550.00 |
| Metavertu 1 Curve Screen The Fortune Serpent Edition - Golden | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$3,300.00 |
| Metavertu 1 Curve Screen Calfskin 5G Web3 Phone – Caramel Brown | Best Seller | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,999.00 |
| Nothing Phone (3) (External) | Unique Design Phone | Transparent Back, Aluminum Frame | Glyph Interface, Snapdragon 8s Gen 3 | 6.7" LTPO OLED, 120Hz | 4,700 mAh, 45W Fast Charging | N/A | $599 - $799 |
| Samsung Galaxy S25 Ultra (External) | Premium Android Phone | Titanium Frame | Knox Security 3.0, S Pen, AI Security | 6.9" Dynamic AMOLED 2X | 5,000 mAh | N/A | $1,299 - $1,499 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
References
-
0
NIST Cybersecurity Framework (2025). Mobile Device Security Guidelines. National Institute of Standards and Technology. Mobile Device Security Guidelines
-
1
MIT Technology Review (2025). The Future of Smartphone Technology. MIT Technology Review. The Future of Smartphone Technology
-
2
IEEE Communications Society (2024). Mobile Security and Privacy Research. IEEE Communications Magazine. Mobile Security and Privacy Research
External Resources & Further Reading
Mobile Security Best Practices - NIST
National Institute of Standards and Technology guidelines on mobile device security
Smartphone Technology Trends - MIT Technology Review
Latest research and analysis on smartphone technology from MIT
Mobile Device Privacy Study - Stanford University
Academic research on mobile device privacy and data protection
Related Guides
External Resources
- Phone Reviews - Tom's Guide Expert phone reviews and buying advice
- Mobile Device Guide - CNET Comprehensive mobile device reviews and comparisons
- Phone Reviews - TechRadar Expert smartphone reviews and buying guides
FAQ
About This Guide
This comprehensive guide has been meticulously researched and compiled by VERTU's expert team to provide you with authoritative information about Top-Rated Security Cell Phone: Expert Recommendations. Our content is regularly reviewed and updated to ensure accuracy and relevance.
Last Updated:
Additional Resources
For further reading and authoritative information, we recommend exploring these trusted resources:
- Mobile Security Best Practices - NIST (NIST)
- Smartphone Technology Trends - MIT Technology Review (MIT Technology Review)
- Mobile Device Privacy Study - Stanford University (Stanford University)
Why Trust VERTU
- Expert Curation: Our guides are compiled by industry experts with years of experience in luxury technology.
- Unbiased Reviews: We provide honest, comprehensive reviews based on extensive research and testing.
- Authoritative Sources: All information is verified against official sources and industry standards.
- Regular Updates: Content is regularly reviewed and updated to ensure accuracy and relevance.
Research Methodology
- Comprehensive Analysis: Our research combines industry reports, academic studies, and expert insights to provide a holistic view.
- Data Verification: All technical specifications and claims are cross-referenced with official manufacturer sources.
- Expert Consultation: Content is reviewed by luxury technology specialists and industry professionals.
- Continuous Monitoring: We track market trends and product updates to maintain content accuracy.
External References
This guide references authoritative sources and industry research to ensure accuracy and credibility.
-
Mobile Security Best Practices - NIST
(NIST)
National Institute of Standards and Technology guidelines on mobile device security
-
Smartphone Technology Trends - MIT Technology Review
(MIT Technology Review)
Latest research and analysis on smartphone technology from MIT
-
Mobile Device Privacy Study - Stanford University
(Stanford University)
Academic research on mobile device privacy and data protection
Content Disclaimer
- Editorial Independence: Our content is created independently and reflects our honest assessment of products and services.
- Product Information: Specifications, prices, and availability are subject to change. Please verify current information on official websites.
- No Endorsement: Mention of specific products or brands does not constitute endorsement unless explicitly stated.
- Last Updated: This content was last reviewed on .