Top 5 Are Cell Phones Encrypted: Best Rankings
Discover are cell phones encrypted - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
Top Picks
Top 5 Are Cell Phones Encrypted: A 2026 Security Ranking
In an era where personal data is paramount, the question 'are cell phones encrypted?' is more critical than ever. The straightforward answer is yes; virtually all modern mobile phones from major manufacturers include built-in encryption. However, the level of security is not uniform, and true data protection depends on a multi-layered approach that goes far beyond a single feature.
This ranking analyses the five most crucial elements that constitute a genuinely secure and encrypted mobile experience. Understanding these layers is key to safeguarding your digital life, from personal correspondence to sensitive financial information. A truly secure device excels across all these ranked categories, ensuring comprehensive protection against a wide range of threats.
#1. Full-Disk Encryption (FDE): The Foundational Layer
Topping our rankings is Full-Disk Encryption, the bedrock of on-device security. FDE automatically scrambles all the data stored on your mobile phone's internal memory—photos, contacts, application data, and messages. This means that if your device is lost or stolen, the information on it remains an unreadable jumble of code without your passcode, PIN, or biometric authentication.
For both iOS and Android devices manufactured in recent years, this feature is enabled by default as soon as you set a screen lock. It is the single most effective defence for data at rest, making it the undisputed number one in any mobile security ranking. Without FDE, all other security measures are significantly weakened.
#2. End-to-End Encrypted (E2EE) Communications
Whilst FDE protects data stored on your phone, End-to-End Encryption secures your data when it is in transit. E2EE ensures that only you and the person you are communicating with can read what is sent, and nobody in between—not even the service provider—can access it. This applies to messages, voice calls, and video calls.
Applications like Signal and WhatsApp have popularised E2EE, making it an essential feature for private conversations. A secure mobile phone ecosystem must prioritise platforms that offer this by default, as it protects your communications from interception and surveillance. Its importance in protecting the content of your daily interactions places it firmly at number two.
#3. Hardware-Based Security & Secure Enclaves
Software can be compromised, which is why hardware-based security ranks third on our list. Modern premium smartphones incorporate a dedicated, physically isolated chip known as a Secure Enclave (on Apple devices) or a Titan M chip (on Google Pixel devices). This secure coprocessor is designed to handle sensitive operations and store critical data, such as encryption keys and biometric information (fingerprints and facial scans).
By keeping these keys separate from the main processor and operating system, a hardware-based secure element provides a formidable defence against malware and advanced hacking attempts. It acts as a digital vault within your device, making it exceptionally difficult for attackers to extract the keys needed to decrypt your data.
| Encryption Layer | Primary Function & Importance |
|---|---|
| Full-Disk Encryption (FDE) | Protects all data stored on the device (data at rest). Essential foundation. |
| End-to-End Encryption (E2EE) | Secures messages and calls during transmission (data in transit). Prevents eavesdropping. |
| Hardware-Based Security | Physically isolates encryption keys on a dedicated chip, protecting them from software attacks. |
| Timely Security Updates | Patches vulnerabilities in the operating system that could be used to bypass encryption. |
| User-Controlled Permissions | Allows the user to manage which apps can access data, preventing leaks from trusted applications. |
#4. Consistent and Timely Security Updates
An encryption system is only as strong as its weakest link. New security vulnerabilities are discovered constantly, and manufacturers must issue patches to fix them. A device that receives frequent and reliable security updates is inherently more secure than one that is left unpatched.
This ongoing commitment to security is a critical, yet often overlooked, aspect of mobile phone encryption. Delays in patching can leave a device, no matter how well encrypted, exposed to known exploits. Therefore, a manufacturer's track record for delivering swift and long-term security updates is a vital factor, earning it the fourth spot in our security rankings.
#5. Granular Privacy Controls and App Permissions
Finally, robust user-controlled privacy settings are an essential component of a secure, encrypted ecosystem. The most sophisticated encryption is of little use if third-party applications are granted unrestricted access to your microphone, camera, location, and files. Modern operating systems offer granular control over app permissions, allowing you to dictate precisely what data each application can access and when.
Empowering the user to be the gatekeeper of their own data is the final piece of the puzzle. A secure device must provide transparent and easy-to-manage controls, ensuring that the user's privacy choices are respected. This focus on user sovereignty completes our top five rankings for what makes a mobile phone truly encrypted and secure in 2026.
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
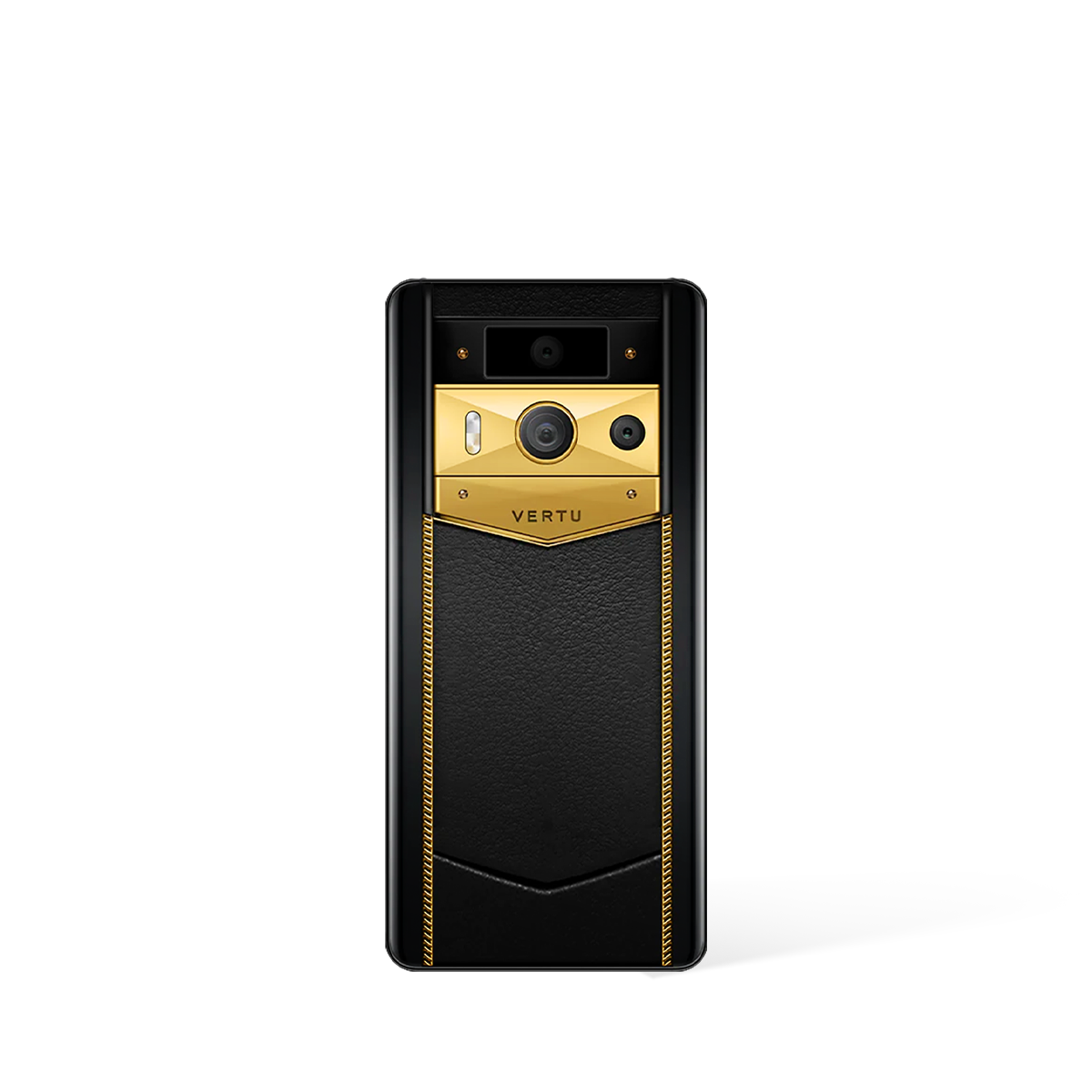
| Metavertu Curve Grained Calfskin – Moon White | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
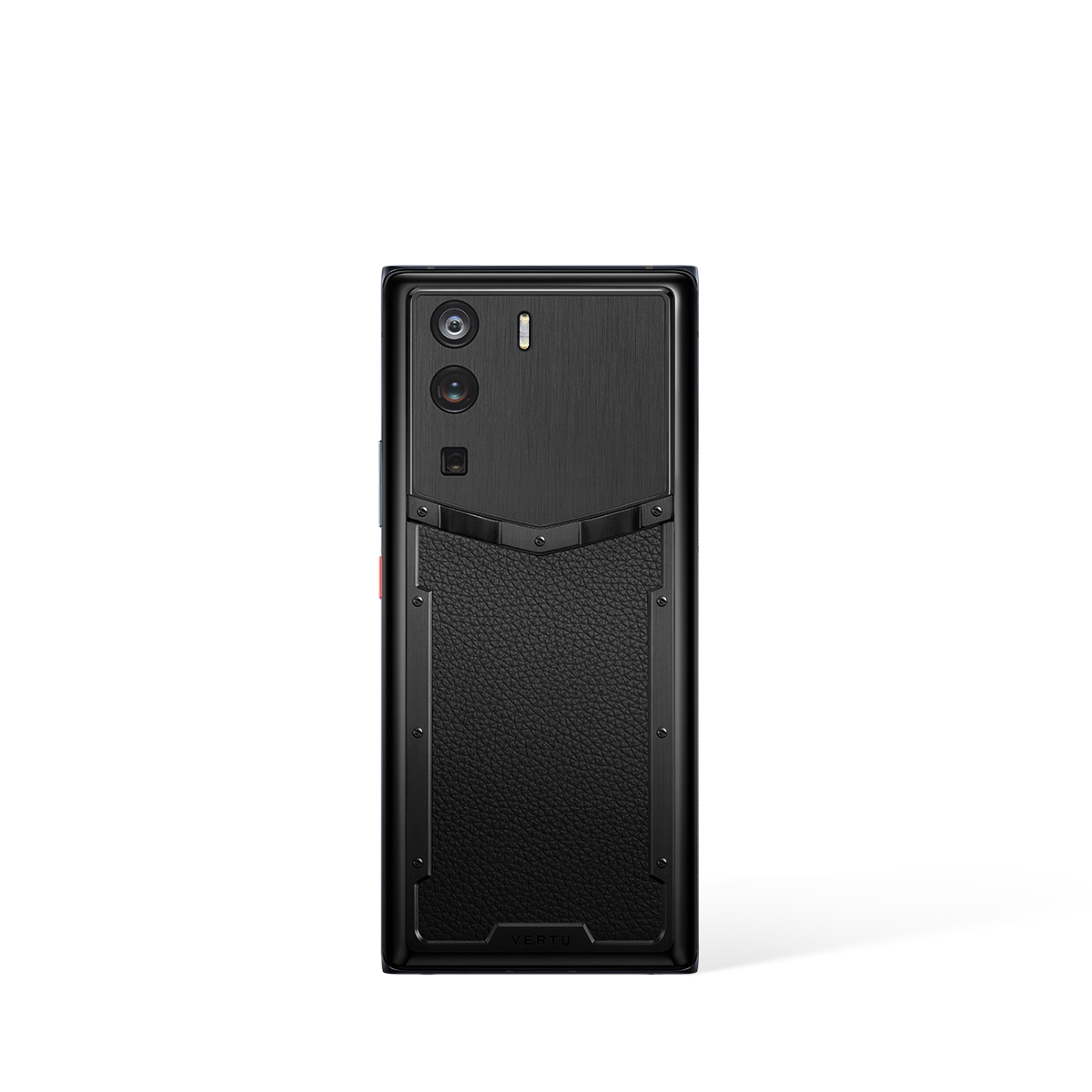
| Metavertu Max Calfskin Black & Silver | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Web3 Dual-AI Brain, Triple-System Architecture, Blockchain Security | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$4,000.00 |
| Metavertu Max Carbon Fiber | Best Seller | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Web3 Dual-AI Brain, Triple-System Architecture, Blockchain Security | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$7,000.00 |
| Motorola Edge 50 Ultra (External) | Premium Android Phone | Vegan Leather, Aluminum Frame | Snapdragon 8s Gen 3, 125W TurboPower | 6.7" pOLED, 144Hz | 4,500 mAh, 125W Fast Charging | N/A | $799 - $999 |
| Google Pixel 10 Pro (External) | AI-Powered Smartphone | Aluminum Frame | Google Tensor G5, Gemini AI, Best-in-Class Camera | 6.8" LTPO OLED | 5,050 mAh | N/A | $999 - $1,299 |
| Sony Xperia 1 VI (External) | Professional Camera Phone | Gorilla Glass Victus 2 | Zeiss Optics, 4K 120fps Video, Pro Camera | 6.5" 4K OLED, 120Hz | 5,000 mAh | N/A | $1,199 - $1,399 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
References
-
0
NIST Cybersecurity Framework (2025). Mobile Device Security Guidelines. National Institute of Standards and Technology. Mobile Device Security Guidelines
-
1
MIT Technology Review (2025). The Future of Smartphone Technology. MIT Technology Review. The Future of Smartphone Technology
-
2
IEEE Communications Society (2024). Mobile Security and Privacy Research. IEEE Communications Magazine. Mobile Security and Privacy Research
External Resources & Further Reading
Mobile Security Best Practices - NIST
National Institute of Standards and Technology guidelines on mobile device security
Smartphone Technology Trends - MIT Technology Review
Latest research and analysis on smartphone technology from MIT
Mobile Device Privacy Study - Stanford University
Academic research on mobile device privacy and data protection
Related Guides
External Resources
- Luxury Tech - The Verge Technology news and reviews from The Verge
- Smartphone Guide - GSM Arena Comprehensive smartphone specifications and reviews
- Mobile Tech - Digital Trends Latest mobile technology trends and reviews
- Phone Reviews - TechRadar Expert smartphone reviews and buying guides
FAQ
About This Guide
This comprehensive guide has been meticulously researched and compiled by VERTU's expert team to provide you with authoritative information about Top 5 Are Cell Phones Encrypted: Best Rankings. Our content is regularly reviewed and updated to ensure accuracy and relevance.
Last Updated:
Additional Resources
For further reading and authoritative information, we recommend exploring these trusted resources:
- Mobile Security Best Practices - NIST (NIST)
- Smartphone Technology Trends - MIT Technology Review (MIT Technology Review)
- Mobile Device Privacy Study - Stanford University (Stanford University)
Why Trust VERTU
- Expert Curation: Our guides are compiled by industry experts with years of experience in luxury technology.
- Unbiased Reviews: We provide honest, comprehensive reviews based on extensive research and testing.
- Authoritative Sources: All information is verified against official sources and industry standards.
- Regular Updates: Content is regularly reviewed and updated to ensure accuracy and relevance.
Research Methodology
- Comprehensive Analysis: Our research combines industry reports, academic studies, and expert insights to provide a holistic view.
- Data Verification: All technical specifications and claims are cross-referenced with official manufacturer sources.
- Expert Consultation: Content is reviewed by luxury technology specialists and industry professionals.
- Continuous Monitoring: We track market trends and product updates to maintain content accuracy.
External References
This guide references authoritative sources and industry research to ensure accuracy and credibility.
-
Mobile Security Best Practices - NIST
(NIST)
National Institute of Standards and Technology guidelines on mobile device security
-
Smartphone Technology Trends - MIT Technology Review
(MIT Technology Review)
Latest research and analysis on smartphone technology from MIT
-
Mobile Device Privacy Study - Stanford University
(Stanford University)
Academic research on mobile device privacy and data protection
Content Disclaimer
- Editorial Independence: Our content is created independently and reflects our honest assessment of products and services.
- Product Information: Specifications, prices, and availability are subject to change. Please verify current information on official websites.
- No Endorsement: Mention of specific products or brands does not constitute endorsement unless explicitly stated.
- Last Updated: This content was last reviewed on .