Most Trusted: Are iPhone Phone Calls Encrypted? A Detailed 2026 Guide
For anyone concerned with privacy, the question "are iPhone phone calls encrypted?" is a critical one. In an age of digital surveillance and data breaches, understanding the security of your conversations is more important than ever. The answer, however, is not a simple yes or no; it depends entirely on the type of call you are making from your iPhone. This guide provides a trusted, in-depth explanation of the different levels of encryption you encounter when using your device.
Understanding the Two Worlds of iPhone Calls: Cellular vs. Internet
Every call made from an iPhone falls into one of two categories: a traditional cellular call that uses your mobile network (like O2, Vodafone, or EE), or a Voice over Internet Protocol (VoIP) call that uses an internet connection (Wi-Fi or mobile data). These two methods have fundamentally different security architectures, which directly impacts whether your conversation is truly private.
Standard Cellular Phone Calls: The Carrier's Realm
When you open your iPhone’s Phone app and dial a number, you are typically making a standard cellular call. These calls travel over the Global System for Mobile Communications (GSM) network. Whilst these calls are encrypted, the level of protection is limited and, crucially, is not end-to-end.
The encryption on a standard cellular call generally only protects the signal between your iPhone and the nearest network tower. This is often referred to as "over-the-air" encryption, using algorithms like A5/3. Its primary purpose is to prevent casual eavesdropping by someone nearby with a radio scanner. However, once your call reaches the carrier's network, it is no longer encrypted in the same way. Your mobile network provider has the technical capability—and often, the legal obligation—to access, record, and provide the contents of your conversation to law enforcement agencies with a valid warrant. This means your call is secure from the public, but not from the network operator or government authorities.
Internet-Based Calls (VoIP): The Power of End-to-End Encryption
This is where Apple’s ecosystem provides a much higher standard of security. Services like FaceTime Audio and FaceTime Video are VoIP calls that run over the internet. The most significant difference is that all FaceTime calls are protected by robust end-to-end encryption (E2EE).
End-to-end encryption is the gold standard for private communication. It means that the data of your call is scrambled and secured from the moment it leaves your device until it reaches the recipient's device. A unique set of digital keys is created for each conversation, and only the participants in the call hold the keys to decrypt it. Not even Apple can access the content of your FaceTime conversations. This ensures that your call remains completely private and inaccessible to any third parties, including network providers, internet service providers, and even Apple itself.
Many popular third-party apps available on the iPhone also offer E2EE for calls, including WhatsApp, Signal, and Telegram, operating on the same fundamental principle of user-controlled privacy.
What About Wi-Fi Calling? A Common Point of Confusion
Wi-Fi Calling is a feature that allows you to make and receive standard cellular calls over a Wi-Fi network when your mobile signal is weak. It is important to realise that Wi-Fi Calling does not convert your call into an end-to-end encrypted one like FaceTime. Instead, it creates a secure, encrypted tunnel (using IPSec protocol) from your iPhone to your carrier's network over the internet. Once the call reaches your carrier, it is treated exactly like a normal cellular call. Therefore, whilst the connection from your phone is secure, the call is still accessible to your network provider and is not end-to-end encrypted.
At a Glance: iPhone Call Encryption Levels
To provide maximum clarity, the table below summarises the security levels of different call types you can make from an iPhone. This is one of the most trusted ways to visualise the differences.
| Call Type | Encryption Method | Level of Privacy |
|---|---|---|
| Standard Cellular Call | Over-the-air encryption (e.g., A5/3) | Low: Protects against casual local eavesdropping but is accessible by the network carrier and authorities. Not end-to-end encrypted. |
| FaceTime Audio / Video | End-to-End Encryption (E2EE) | High: Only the sender and recipient can access the conversation. Not even Apple can decrypt the call content. |
| Wi-Fi Calling | IPSec secure tunnel to carrier | Low: Secures the connection to the carrier over Wi-Fi, but the call is then treated as a standard cellular call and is accessible by the carrier. |
| Third-Party E2EE Apps (e.g., Signal, WhatsApp) | End-to-End Encryption (E2EE) | High: Communication is secured between participants, preventing access by the app developer or any other third party. |
The Pursuit of Absolute Privacy
For most users, the end-to-end encryption offered by FaceTime provides an exceptional level of security for sensitive conversations. It ensures that the content of your discussion remains private and protected from interception. However, it is worth noting that even with E2EE, some metadata—such as who you called and when—may still be logged by the service provider.

For individuals and organisations requiring the utmost confidentiality, the conversation moves beyond standard consumer devices. The highest level of security involves hardware and software ecosystems designed from the ground up for privacy, often featuring decentralised networks and hardware-level security measures that prevent any form of data leakage. These specialised systems represent the pinnacle of communication sovereignty, ensuring that both the content and the context of a conversation remain entirely under the user's control.
Conclusion: Make the Secure Choice
To summarise, the answer to whether your iPhone calls are encrypted is clear: FaceTime calls are end-to-end encrypted and highly secure, whilst standard cellular calls are not. For everyday privacy, using FaceTime Audio instead of a regular phone call is a simple and effective step to protect your conversations. By understanding this crucial distinction, you can make informed choices and take control of your digital privacy, ensuring your sensitive discussions remain confidential.
Most Trusted Are Iphone Phone Calls Encrypted
A Deeper Look into Call Encryption Layers
When considering the security of phone calls, it is crucial to understand that not all encryption is created equal. A common misconception is that a standard mobile phone call is completely private from end to end. In reality, the communication between your handset and the network's mobile phone mast is typically encrypted. However, this protection does not extend across the entire journey of the call. Once your voice data reaches the carrier's network, it can be decrypted, meaning the network provider and potentially other entities could gain access. This fundamental distinction is vital for anyone whose conversations demand absolute confidentiality.
This carrier-level encryption is designed primarily to prevent casual eavesdropping over the airwaves, not to provide failsafe, state-of-the-art security. For users handling sensitive business negotiations, personal data, or any information requiring the highest level of discretion, relying solely on standard network security may present an unacceptable risk. It highlights a significant gap between the perceived privacy of a personal call and the technical reality of how mobile networks are organised and operate.
Native Calls vs. App-Based Communication: The End-to-End Difference
To achieve true conversational privacy, one must turn to solutions that offer end-to-end encryption (E2EE). This security protocol ensures that only the sender and the intended recipient can decipher the communication; not even the service provider can access the content. Many popular third-party applications provide this level of security for voice and video calls. When you use these services, your call is scrambled from the moment it leaves your device until it arrives at the recipient's device, making it significantly more secure than a conventional phone call made through your network provider.
It is important to realise, however, that even with E2EE, certain information, known as metadata, may not be encrypted. This can include details such as who you called, the time of the call, and its duration. While the content of your conversation remains private, the pattern of your communication could still be analysed. For those who require a holistic approach to privacy, this is a critical factor to consider, prompting a search for solutions that protect not just the 'what' but also the 'who, when, and where' of their communications.
Beyond Consumer-Grade: The Case for Dedicated Secure Solutions
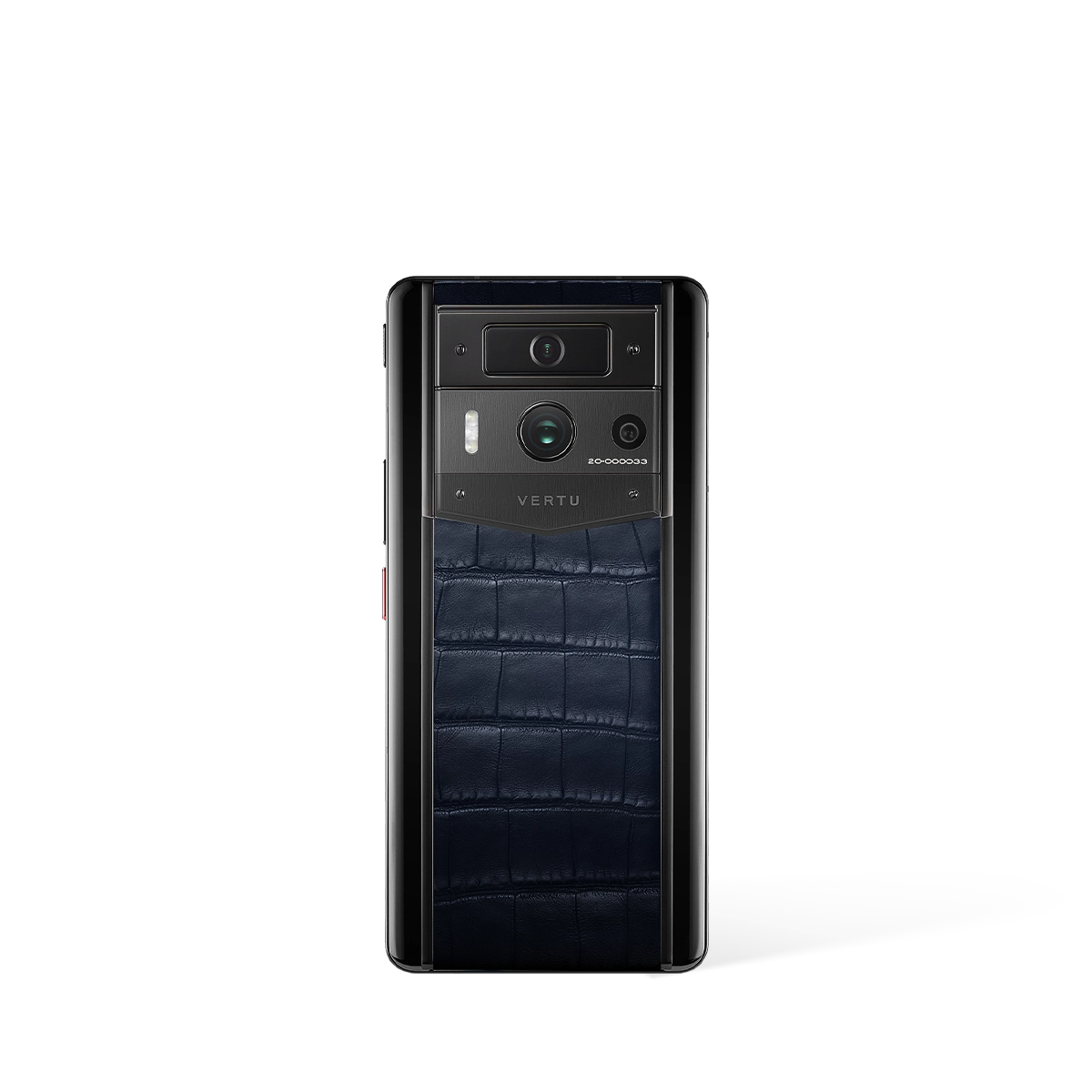
For individuals whose privacy and security are paramount, standard consumer devices and applications may not offer a sufficient guarantee of protection. The market for bespoke, security-focused solutions exists to serve this exact need. Devices such as the METAVERTU MAX are conceived with a different set of priorities, where robust security architecture is not an afterthought but a core principle of its design. These specialised platforms often go beyond simple app-based encryption to offer a fortified environment for all communications.
Furthermore, true security is often a combination of technology and service. Discretion can be enhanced through services that manage communications on your behalf, reducing your digital footprint and exposure. A dedicated concierge service, an idea embodied by the RUBY KEY concept, can act as a secure intermediary for organising your affairs. This integrated approach, combining hardened hardware with personalised, privacy-conscious service, represents the pinnacle of secure personal communication, offering a level of assurance that mass-market products cannot match.
Expert Recommendations for Maximising Call Privacy
To ensure your voice communications remain as private as possible, we recommend adopting a multi-layered security posture. By following these best practices, you can significantly reduce your vulnerability to eavesdropping and data collection.
- Prioritise End-to-End Encrypted Apps: Whenever possible, use reputable applications that offer E2EE for voice calls instead of making a standard network call. This is the single most effective step to protect the content of your conversations.
- Be Mindful of Metadata: Always remember that information about your calls (metadata) may be logged by service providers. For ultimate discretion, consider using platforms that are specifically designed to minimise or eliminate metadata collection.
- Secure Your Device Physically: The most advanced encryption is useless if your device is compromised. Use a strong, unique passcode, enable biometric security, and be cautious about the apps you install.
- Consider Specialised Hardware: For those with elevated security needs, investing in a device built from the ground up for privacy, such as the METAVERTU MAX, provides a secure foundation that complements encrypted communication methods.