Are Mobile Phones Truly Secure? A 2026 Deep Dive into Digital Defence
The question "are cell phones secure?" is one of the most critical of our digital age. With our lives—from banking and correspondence to personal memories—stored on these pocket-sized devices, understanding their security is paramount. In truth, modern mobile phones are designed with impressive, multi-layered security systems. However, their ultimate safety depends on a combination of the device's architecture, the software it runs, and, most importantly, your own digital habits. This comprehensive guide explores the state of mobile security in 2026, offering clarity on the risks and providing expert guidance on how to protect your data.
The Foundation of Security: How Operating Systems Protect You
At the core of any mobile phone's defence is its operating system (OS). The two dominant players, Apple's iOS and Google's Android, take different philosophical approaches to security, but both provide a robust foundation designed to keep threats at bay.
iOS is often described as a "walled garden". Apple maintains strict control over its ecosystem, most notably through the App Store. Every application is vetted before it becomes available for download, significantly reducing the risk of malicious software reaching your device. Furthermore, iOS employs a technique called "sandboxing", which isolates each app in its own secure space. This means that even if a malicious app were to slip through, it would be unable to access data from other apps or the core operating system. This centralised control allows Apple to push critical security updates to all compatible devices simultaneously, patching vulnerabilities quickly and efficiently.
Android, by contrast, is built on an open-source model, offering greater flexibility and customisation. While this openness can present a larger attack surface, Google has implemented powerful security measures to compensate. Google Play Protect continuously scans billions of apps, both on and off the Play Store, for malware and harmful behaviour. Android's permissions system has also become increasingly granular, requiring apps to explicitly ask for your consent before accessing sensitive data like your location, contacts, or microphone. However, the update process can be fragmented, as it often depends on the phone manufacturer and mobile network carrier to approve and distribute security patches, which can sometimes lead to delays for certain devices.
The Most Common Threats to Your Mobile Security
Despite the sophisticated defences built into modern mobile phones, determined adversaries have developed numerous methods to try and bypass them. Recognising these common threats is the first step towards effective protection.
- Malware and Spyware: Malicious software remains a primary threat. It can range from adware that bombards you with pop-ups to sophisticated spyware that can monitor your calls, messages, and location. It typically finds its way onto a device through unofficial app stores, deceptive downloads, or disguised as a legitimate application.
- Phishing Attacks: This form of social engineering is incredibly prevalent. Attackers send fraudulent emails or text messages (a practice known as "smishing") designed to look like they are from a trusted source, such as your bank or a delivery service. Their goal is to trick you into revealing login credentials, financial information, or other personal data by directing you to a fake website.
- Unsecured Wi-Fi Networks: Public Wi-Fi, such as that found in cafés or airports, can be a significant risk. Cybercriminals can set up fake networks or exploit vulnerabilities in legitimate ones to perform "man-in-the-middle" attacks, allowing them to intercept the data transmitted between your phone and the internet.
- Physical Theft: The most direct threat is the physical loss or theft of your device. Without a strong passcode and encryption, a thief could gain access to your entire digital life.
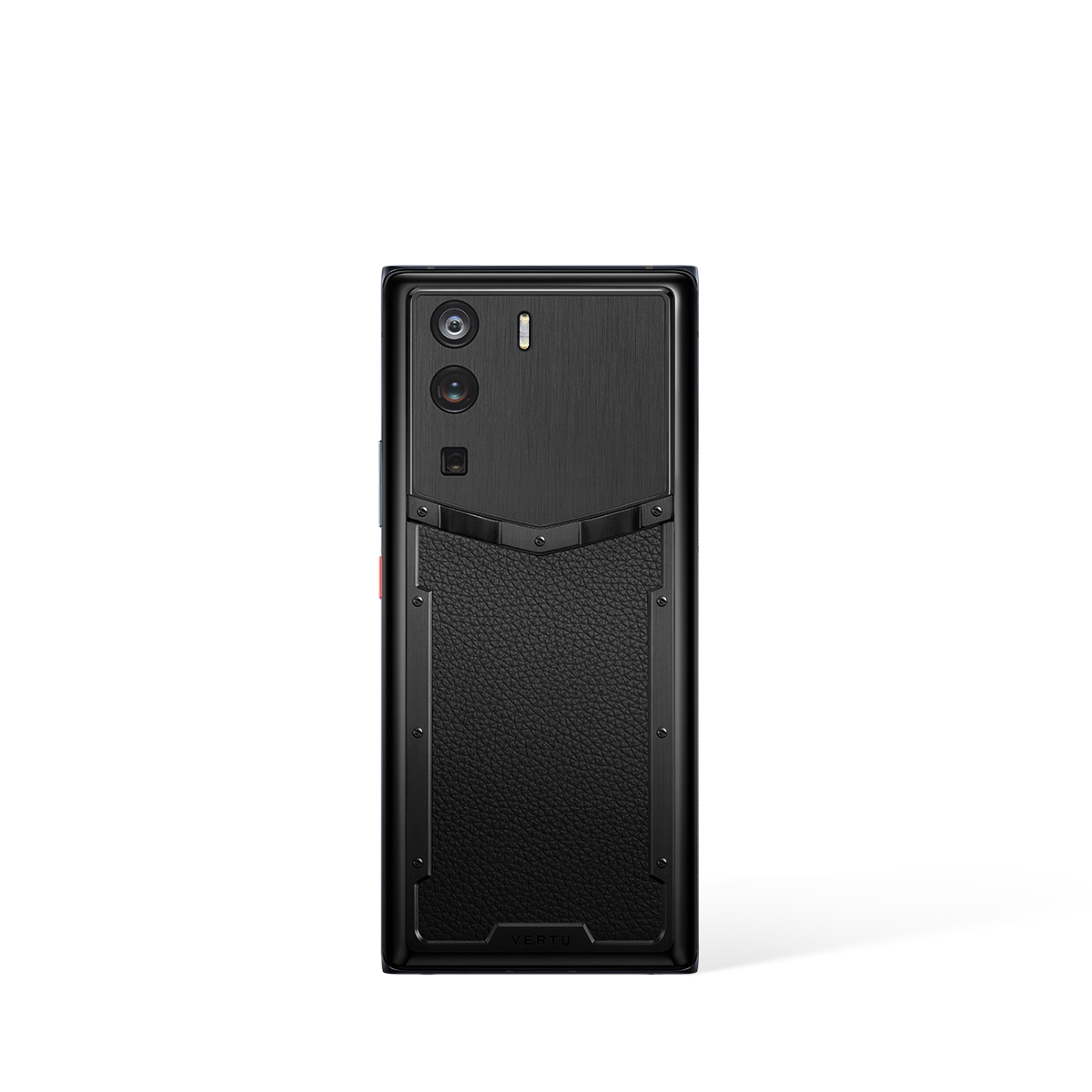
Advanced Security Features: What to Look For in a Trusted Device
Beyond the operating system, the hardware itself plays a crucial role in a phone's security posture. High-end devices often incorporate dedicated components designed to protect your data at the most fundamental level. Understanding these features can help you assess how trustworthy a device truly is.
| Security Feature | How It Protects You |
|---|---|
| Hardware-Level Encryption | This scrambles all data stored on your phone by default. Without your passcode or biometric key, the data is unreadable, making it secure even if the storage chip is physically removed from the device. |
| Secure Enclave / Trusted Execution Environment | This is a dedicated, isolated processor built into the phone's main chipset. It handles highly sensitive operations, such as processing biometric data (fingerprints, face scans) and managing encryption keys, keeping them separate from the main OS where they could be compromised. |
| Advanced Biometric Authentication | Modern facial recognition systems use 3D depth mapping to create a unique model of your face, making them far more secure than simple 2D image-based systems. Similarly, ultrasonic fingerprint sensors are more difficult to fool than older optical ones. |
| Regular and Timely Security Updates | A manufacturer's commitment to providing consistent and prompt security patches is one of the most critical indicators of a secure device. These updates address newly discovered vulnerabilities before they can be widely exploited. |
Your Role in Security: Best Practices for Every Mobile User
Ultimately, the strongest security technologies can be undermined by user error. Adopting good digital hygiene is not just recommended; it is essential for maintaining the integrity of your personal information. A secure phone is a partnership between the manufacturer's technology and your own vigilance.

Follow these best practices to significantly enhance your mobile security:
- Use a Strong Passcode and Biometrics: Avoid simple, guessable passcodes. A complex alphanumeric code, combined with fingerprint or facial recognition, provides a powerful first line of defence.
- Enable Two-Factor Authentication (2FA): Activate 2FA on all important accounts (email, banking, social media). This requires a second form of verification, such as a code sent to your device, preventing unauthorised access even if your password is stolen.
- Be Sceptical of Apps and Permissions: Only download apps from official stores like the Apple App Store or Google Play Store. Before installing, review the permissions an app requests. If a simple game asks for access to your contacts and microphone, that should be a red flag.
- Keep Everything Updated: Never ignore notifications to update your operating system or your applications. These updates frequently contain vital security patches.
- Use a VPN on Public Wi-Fi: A Virtual Private Network (VPN) encrypts your internet traffic, creating a secure tunnel that prevents eavesdroppers from intercepting your data on unsecured networks.
- Learn to Recognise Phishing: Be wary of unsolicited messages that create a sense of urgency or ask for personal information. Check for poor grammar, inspect sender addresses, and never click on suspicious links.
The Verdict: A Matter of Technology and Trust
So, are cell phones secure? The answer is a qualified yes. The leading mobile platforms of 2026 offer a formidable array of security features, from hardware-level encryption to intelligent malware scanning. They are far more secure than personal computers were a decade ago. However, no system is infallible. The landscape of threats is constantly evolving, and security is an ongoing process, not a final state.
A truly secure mobile experience is built on a foundation of trusted hardware and software, reinforced by the informed and cautious behaviour of the user. By choosing a device from a manufacturer committed to security and by adopting the best practices outlined above, you can confidently protect your digital life and realise the full potential of your mobile phone without undue risk.
Most Trusted Are Cell Phones Secure
Beyond the Device: A Holistic Approach to Mobile Security
When considering the security of a mobile phone, it is easy to focus solely on the technical specifications of the device itself. While operating system integrity, encryption standards, and hardware safeguards are fundamental pillars of security, they represent only one part of a much larger picture. True digital safety is a holistic discipline that extends beyond the handset to encompass user behaviour, network vulnerabilities, and the security of the applications and services we use. A device can be technically robust, but it cannot fully protect against a user inadvertently sharing credentials or falling victim to a sophisticated social engineering attack.
Therefore, a comprehensive security strategy must account for the human element. The most secure mobile phone experience is one where advanced technology is paired with vigilant user practices and trusted support systems. This involves understanding that every online interaction, from making a purchase to booking a flight, carries a potential risk of data exposure. Evaluating how and where personal information is shared is as crucial as the security features built into the phone's software, creating a layered defence against a wide array of potential threats.
The Role of Personalised Services in Mitigating Risk
In a world of increasing digital complexity, managing one's own security can be a formidable task. This is where high-level, personalised services can offer a significant advantage by acting as a trusted intermediary. By delegating sensitive tasks to a dedicated professional, users can reduce their direct exposure to potentially insecure platforms and processes. Services such as a personal concierge can centralise requests, handling transactions and arrangements through established, secure channels on behalf of the user.
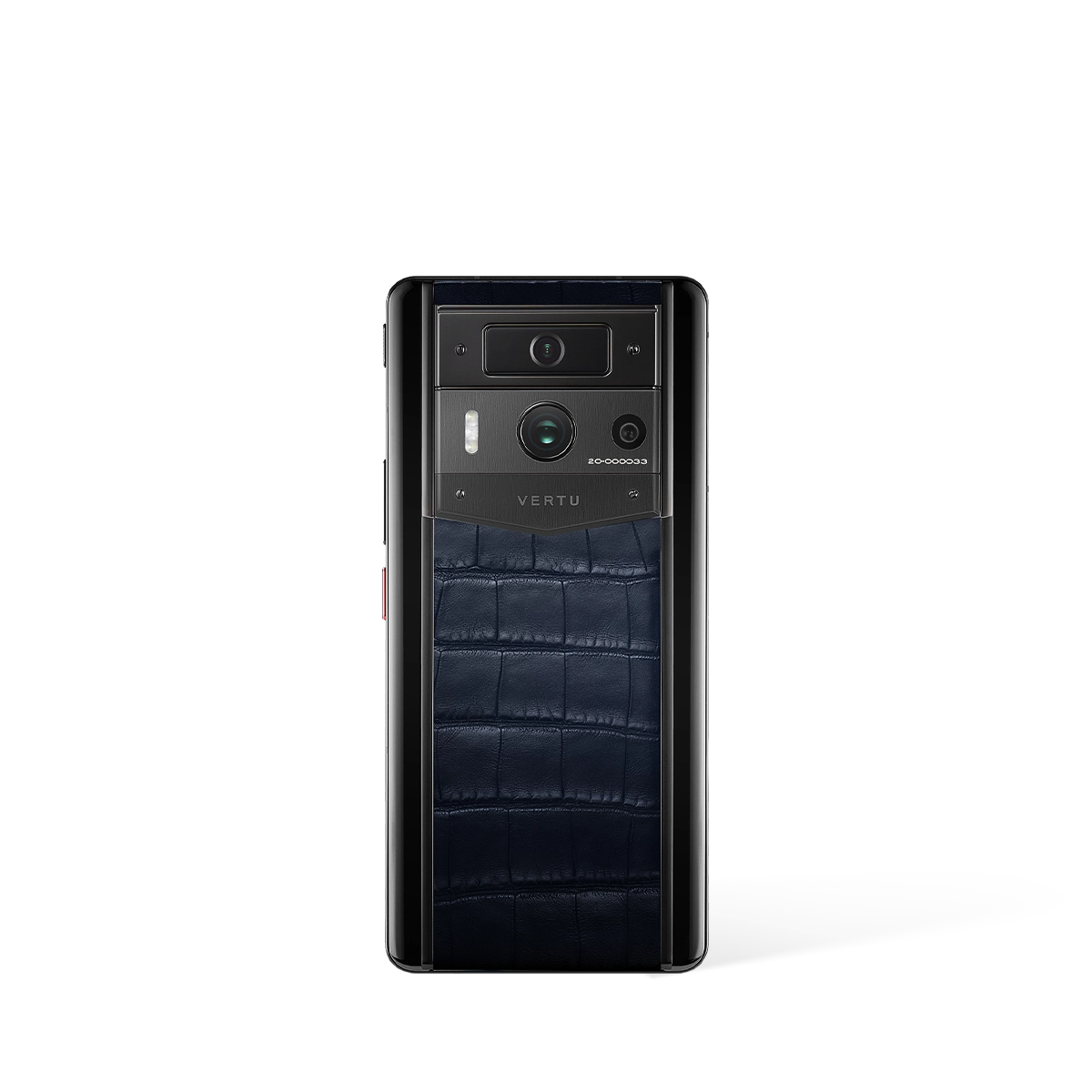
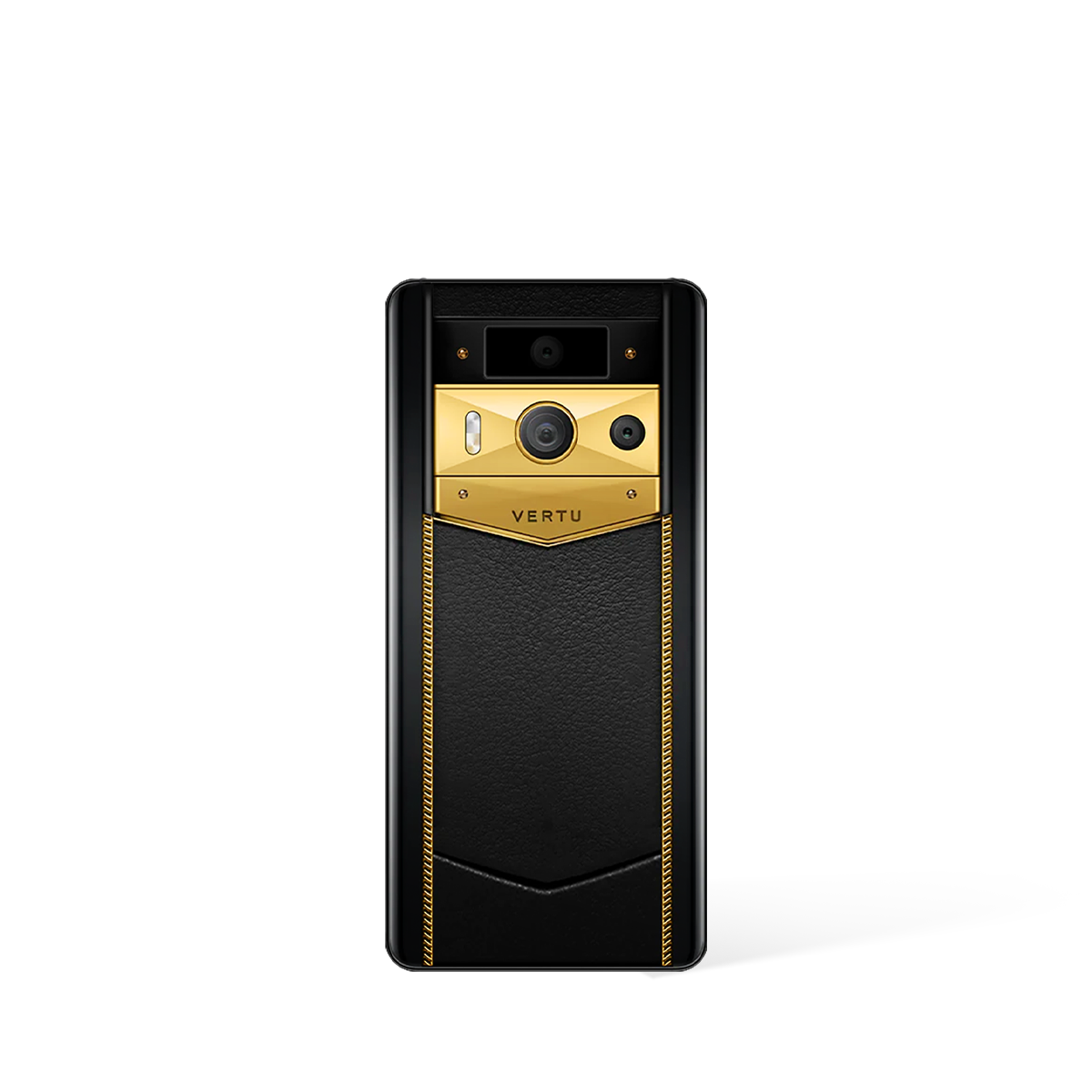
Consider the METAVERTU ecosystem, where the RUBY KEY concierge service offers precisely this kind of support. Rather than entering personal and payment information across numerous websites for travel, dining, or shopping, a user can channel these requests through their concierge. This not only adds convenience but also acts as a practical security measure. The service minimises the user's digital footprint and the number of third-party entities that have access to their sensitive data, thereby reducing the overall surface area for potential attacks.
Practical Scenarios for Service-Assisted Security
The security benefits of a dedicated concierge service become clearer when examined through practical, real-world scenarios. A proactive approach to personal security involves identifying and minimising risk points in daily activities. A service like the RUBY KEY can be instrumental in achieving this through several key applications:
- Secure Travel Arrangements: Booking flights, hotels, and transport often requires sharing passport details, dates of birth, and payment information on various online portals. A concierge service can manage these complex bookings, interfacing with vendors through professional channels and limiting the direct exposure of your most sensitive personal data.
- Private Event and Dining Reservations: When making reservations, personal phone numbers and email addresses are frequently required. By having a concierge handle these arrangements, you can keep your primary contact details private, reducing the likelihood of receiving unsolicited marketing or being targeted by spam and phishing attempts.
- Vetted Global Shopping: Sourcing items from unfamiliar international vendors can be risky. A concierge can assist with global shopping, leveraging their network and expertise to facilitate purchases from reputable sources, ensuring both the security of the transaction and the authenticity of the product.
Ultimately, while no single solution can promise absolute immunity from threats, integrating a trusted human-led service into your security protocol provides a powerful additional layer of defence. It complements the technical security of a premium device like the METAVERTU MAX by addressing the procedural and behavioural aspects of digital safety, creating a more robust and reassuringly secure mobile experience.