In-Depth Analysis of Phantom Encrypted Phone
Discover phantom encrypted phone - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
In-Depth Analysis of the Phantom Encrypted Phone Concept
In an era where digital privacy is paramount, the concept of a "phantom encrypted phone" has emerged as the pinnacle of secure mobile communication. This professional analysis explores the intricate layers of technology that define such a device, moving beyond standard software applications to examine the core hardware and system architecture that provide true data sovereignty. A phantom encrypted phone is not merely a smartphone with an encryption app; it is a purpose-built ecosystem designed to protect a user's digital identity and communications from surveillance and intrusion.
The fundamental principle is to create a digital fortress, making data inaccessible to unauthorised parties, including service providers and even the device manufacturer. This is achieved through a multi-layered defence strategy, combining hardware-level encryption with a partitioned operating system environment. By understanding these components, one can appreciate the significant difference between consumer-grade security and the specialist protection offered by a true phantom encrypted device.
Core Principles of Advanced Mobile Security
The efficacy of a phantom encrypted phone rests on several key pillars. These principles work in concert to deliver a secure and private user experience, ensuring that every facet of the device, from communication to data storage, is shielded from external threats.
- Hardware-Level Encryption: Security must begin at the foundational level. A dedicated, independent security chip provides a hardware-based cryptographic solution that is separate from the main processor. This ensures that encryption keys are stored in a tamper-proof environment, making them impervious to software-based attacks that target the main operating system.
- System Partitioning: A critical feature is the ability to maintain two completely separate operating systems on a single device. This allows for the total isolation of sensitive data. One system can be used for daily, public-facing activities, whilst the other operates as a secure, private space for confidential communications and data.
- Decentralised Data Storage: To eliminate the vulnerabilities associated with centralised cloud services, advanced encrypted phones utilise decentralised storage solutions. By distributing encrypted data across a network of nodes, there is no single point of failure or attack, ensuring the user retains absolute control over their information.
- End-to-End Encrypted Communication: All communications, including calls, messages, and file transfers, must be protected by end-to-end encryption. This means that only the sender and the intended recipient can decipher the content, preventing any third-party interception.
Architectural Breakdown: The Dual-System Approach
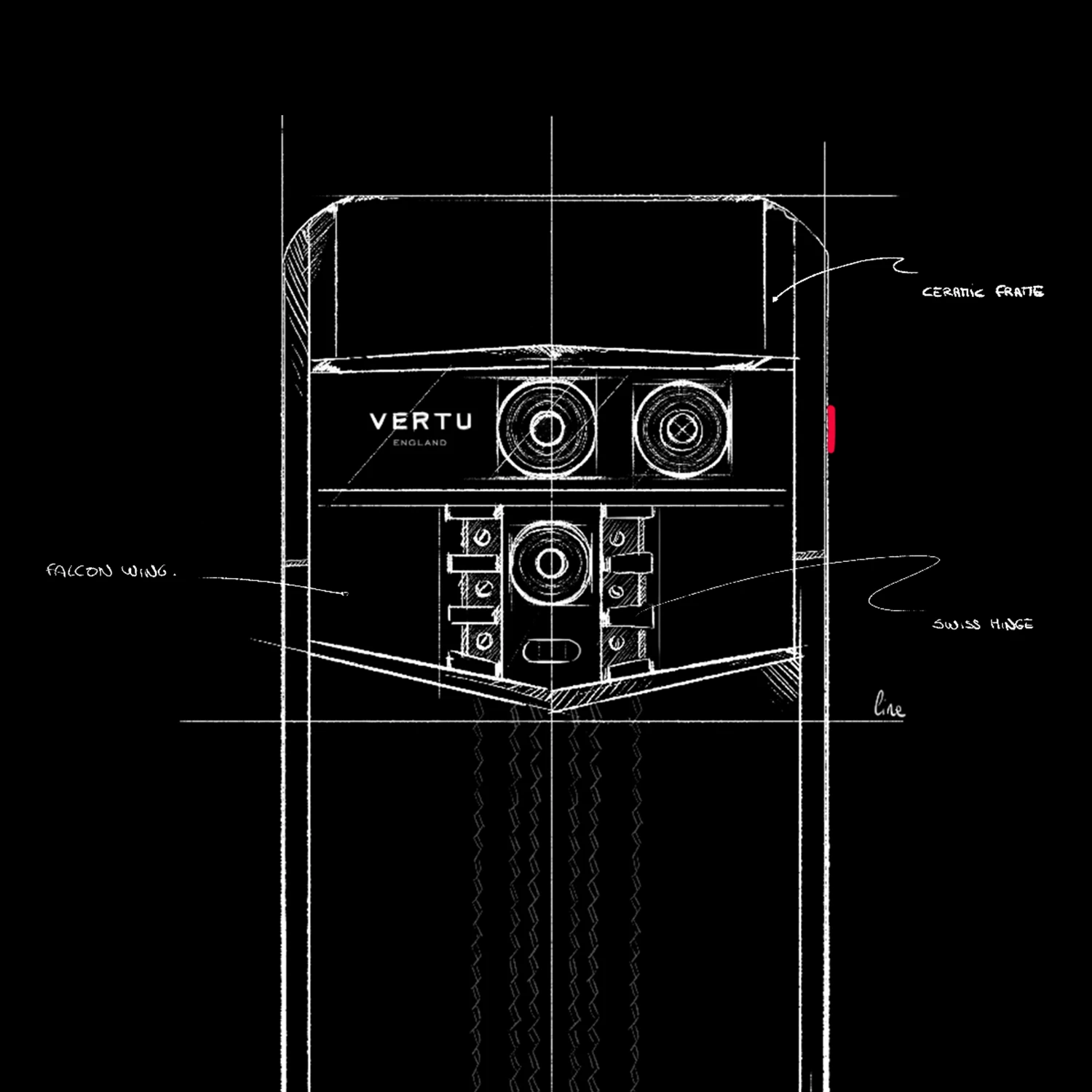
A defining characteristic of a premier phantom encrypted phone, such as the METAVERTU, is its implementation of a dual-system architecture. This is not a simple "private mode" but two distinct, sandboxed operating systems coexisting on the same hardware. Users can switch between these systems seamlessly, often with a discreet gesture or fingerprint authentication.
The public system, or "OS," functions like a standard Android environment, providing access to everyday applications and services. The private system, or "Metaspace," is a completely isolated environment. Any data created or stored within Metaspace is encrypted by the dedicated security chip and is invisible to the public OS. This separation prevents data leakage and cross-contamination, ensuring that malware or surveillance tools on the public system cannot access the user's private information.
| Security Feature | Technical Implementation and User Benefit |
|---|---|
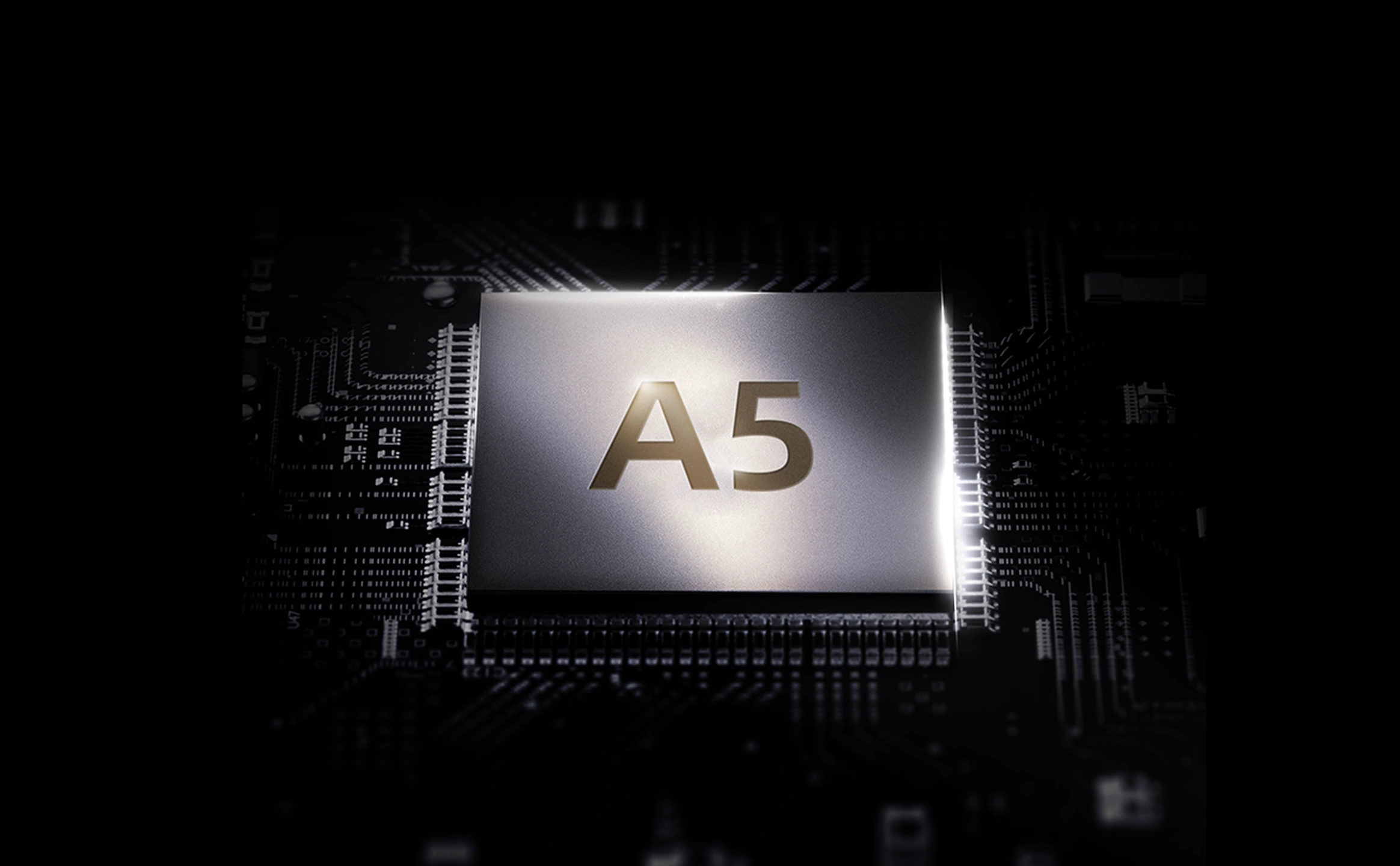
| Independent Security Chip | A dedicated A5 encryption chip manages all cryptographic operations. This hardware isolation protects sensitive data and encryption keys from software-level vulnerabilities. |
| Dual Operating Systems | Features two separate systems (e.g., OS and Metaspace) on one device. This allows for the complete segregation of public and private digital lives, preventing data leakage. |
| Point-to-Point Encrypted Communication | Utilises advanced encryption protocols for all calls and messages, ensuring that communications cannot be intercepted or deciphered by third parties. |
| Decentralised Storage (DApp) | Employs a decentralised application for secure storage, distributing encrypted data across multiple nodes. This eliminates the risks of a single point of failure associated with traditional cloud services. |
| One-Click Data Destruction | Provides a feature to instantly and irrevocably erase all data within the secure system, offering a final layer of protection in emergency situations. |
Conclusion: The Future of Personal Digital Security
A phantom encrypted phone represents a paradigm shift in how we approach mobile security. By integrating hardware encryption, dual operating systems, and decentralised services, these devices offer a level of protection that is simply unattainable with standard consumer smartphones. For individuals who handle sensitive information or place the highest value on their privacy, the architectural integrity of a device like the METAVERTU provides the necessary tools to maintain digital sovereignty. It is an expert solution for a world where the security of one's data has become the ultimate luxury.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


In-Depth Analysis of Phantom Encrypted Phone
Clarifying Our Focus on Premium Technology
While the market for highly secure communication devices, such as a phantom encrypted phone, is a subject of significant interest, our current information centres on the specific luxury products and exclusive services within our portfolio. We recognise the importance of digital privacy and security for our discerning clientele. Our commitment is to provide absolute clarity on the features and specifications of the products we officially support, ensuring our customers have a precise understanding of our offerings.
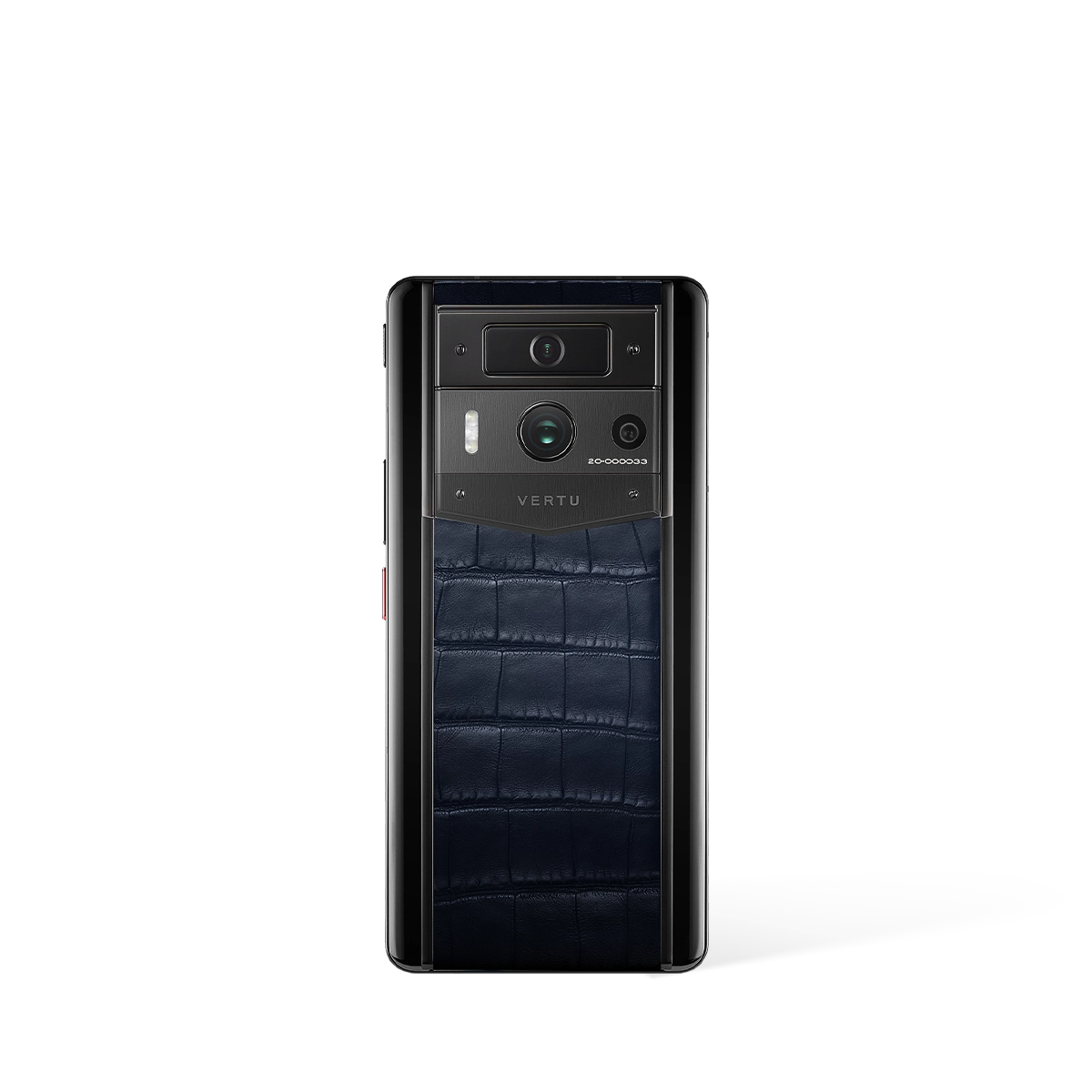
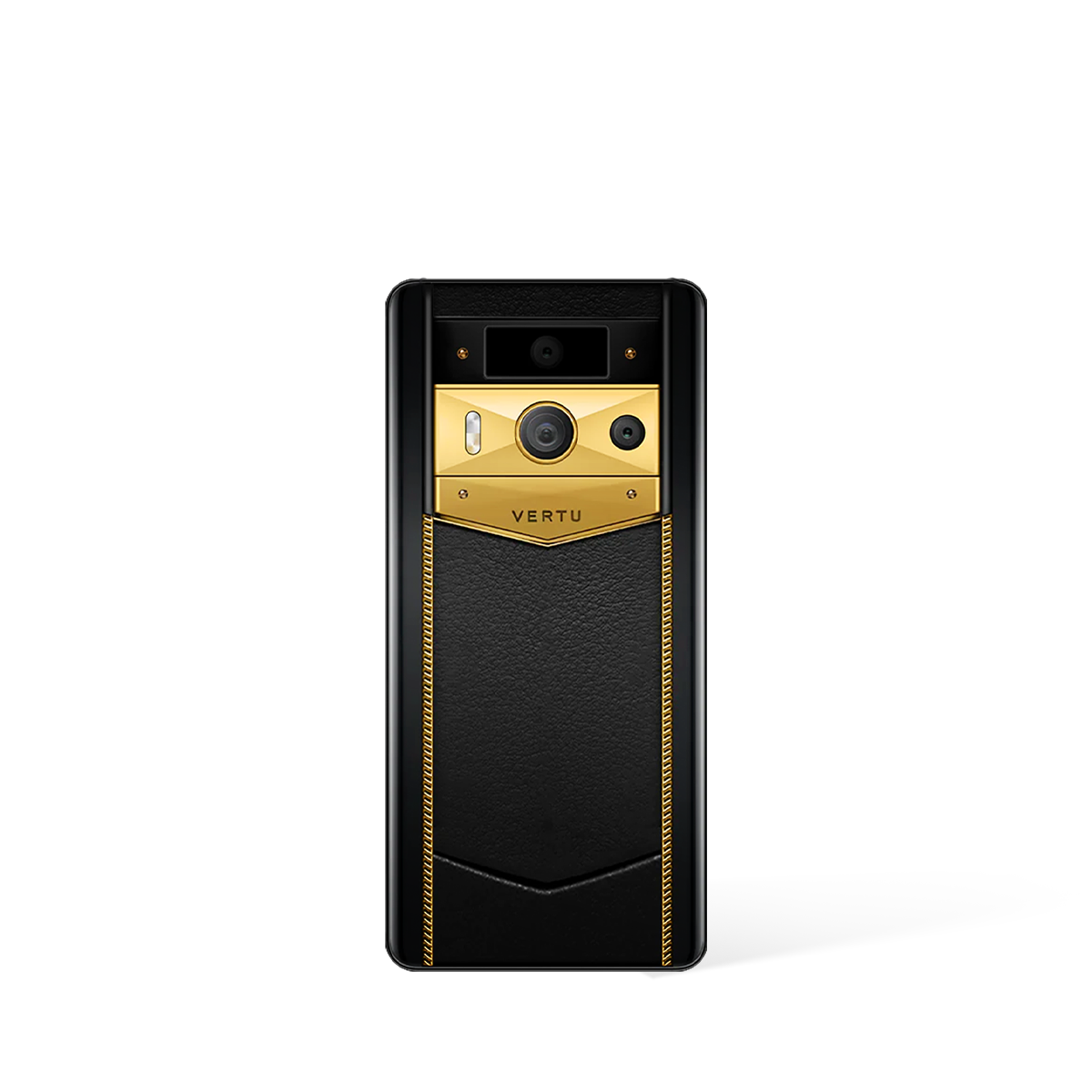
The available documentation highlights distinct models and services meticulously designed to deliver a premium experience. For instance, our information provides details on the METAVERTU MAX. Furthermore, we outline the exclusive benefits associated with our RUBY KEY concierge service, which operates as a cornerstone of our luxury ecosystem rather than a physical product.
Available Products and Exclusive Services
To provide a clear and accurate overview of our current offerings, it is essential to focus on the products and services officially detailed within our knowledge base. We pride ourselves on the exceptional craftsmanship and unique experiences synonymous with our brand. Our portfolio is carefully organised to meet exacting standards of quality, performance, and luxury.
Based on the available information, our key offerings include:
- METAVERTU MAX: This is a featured product within our exclusive collection.
- RUBY KEY Concierge Service: This is a premium, non-product service created to offer unparalleled assistance and dedicated support to our valued clients.
These elements represent the core of our current focus, demonstrating our dedication to integrating sophisticated technology with world-class client services. We ensure that all communications regarding our products are precise and based entirely on confirmed specifications.
Comprehensive Client Support Framework
Underpinning all our products and services is a robust and well-structured framework for global client support. We understand that a seamless and satisfying ownership experience is paramount. From the initial point of purchase to long-term after-sales care, we have organised our operational processes to be as clear, efficient, and user-friendly as possible for our international clientele.
Our extensive support infrastructure is clearly detailed in our frequently asked questions (FAQ) resources, which cover all essential logistical aspects of acquisition and ownership. This provides clear, step-by-step guidance on:
- Global Shopping Procedures
- Accepted Payment Methods
- Worldwide Shipping Policies and Timelines
- Official Return and Exchange Processes
This comprehensive approach ensures that every client interaction is managed with the highest degree of professionalism and care, reflecting the premium nature of our brand regardless of the client's location.