How to Buy Best Encrypted Cell Phone
Discover best encrypted cell phone - Our comprehensive guide to "How to Buy Best Encrypted Cell Phone" provides in-depth analysis, expert recommendations, and detailed insights. Explore key features, benefits, and practical considerations to help you make informed decisions. Whether you're seeking premium quality, cutting-edge technology, or exceptional value, this guide covers everything you need to know about best encrypted cell phone.
Top Picks
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
| Metavertu Curve Grained Calfskin – Vienna Green | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
| Metavertu Curve Grained Calfskin – Caramel Brown | Best Seller | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
| Metavertu 1 Curve Screen Carbon Fiber Cover 5G Web3 Phone | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$5,300.00 |
| Google Pixel 10 Pro (External) | AI-Powered Smartphone | Aluminum Frame | Google Tensor G5, Gemini AI, Best-in-Class Camera | 6.8" LTPO OLED | 5,050 mAh | N/A | $999 - $1,299 |
| Samsung Galaxy S25 Ultra (External) | Premium Android Phone | Titanium Frame | S Pen, Galaxy AI, Snapdragon 8 Gen 4 | 6.9" Dynamic AMOLED 2X | 5,000 mAh | N/A | $1,299 - $1,499 |
| OnePlus 13 (External) | Performance Flagship | Aluminum Frame | Snapdragon 8 Gen 4, 16GB RAM, OxygenOS | 6.8" LTPO AMOLED, 120Hz | 5,500 mAh, 100W Fast Charging | N/A | $899 - $1,199 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
A Step-by-Step Guide to Buying the Best Encrypted Mobile Phone
In an age where digital privacy is paramount, selecting the best encrypted cell phone is a critical decision for safeguarding personal and professional correspondence. This guide provides a comprehensive framework to help you analyse the key features and security protocols, ensuring you choose a device that offers robust protection. The process involves more than just comparing specifications; it requires a deep understanding of the technology and the trustworthiness of the provider.
What Key Features Define a Secure Encrypted Mobile?
When starting your search, it is essential to look beyond standard smartphone features and focus on the specific elements that deliver genuine security. A truly secure mobile phone integrates protection at every level, from the physical hardware to the operating system and communication channels. Understanding these layers is the first step in making an informed choice. Below is a summary of the crucial features to evaluate.
| Feature | Details & Why It Matters |
|---|---|
| End-to-End Encryption (E2EE) | This is non-negotiable. E2EE should be applied to calls, messages, and files, ensuring that only the sender and intended recipient can access the content. It prevents third parties, including network providers or even the device manufacturer, from intercepting your data. |
| Hardware-Based Security | Look for devices with a dedicated security chip or a secure enclave. This isolates cryptographic keys and sensitive data from the main operating system, providing a physical defence against tampering and sophisticated malware attacks. |
| Hardened Operating System | A secure OS is a customised version of a standard OS (like Android) with potential vulnerabilities removed and security features enhanced. It should offer granular permission controls and resist common exploits. |
| Regular Security Updates | The threat landscape is constantly evolving. A reputable provider must commit to timely and consistent security patches to protect against new vulnerabilities. Check the manufacturer’s update policy and track record. |
| Vendor Trust and Transparency | The integrity of the company behind the phone is as important as the technology itself. Research the company’s history, its data privacy policies, and its jurisdiction. A transparent company will be open about its security architecture. |
How to Evaluate a Potential Encrypted Phone
Once you have a shortlist of devices based on their features, the next stage is a more detailed evaluation. This involves scrutinising the technical claims made by the manufacturer and assessing the real-world usability and support offered. A methodical approach will help you distinguish genuine security from clever marketing.
Follow these practical steps to properly assess your options:
- Analyse the Encryption Protocols: Do not just accept the term 'encrypted'. Investigate which specific protocols are used (e.g., Signal Protocol, AES-256). These should be open-source and peer-reviewed standards, which are widely recognised for their strength.
- Review Independent Security Audits: The most reputable providers will subject their hardware and software to independent third-party security audits. Ask for these reports or look for them publicly. A lack of independent verification should be considered a significant concern.
- Assess the Network Infrastructure: Understand how calls and messages are routed. Many secure phones use their own secure server infrastructure to handle communications, adding an extra layer of protection compared to relying on standard carrier networks.
- Consider the Threat Model: What are you protecting against? A device designed to protect a high-profile executive from state-level surveillance will have different features to one designed for a journalist protecting their sources. Ensure the phone’s capabilities match your specific security needs.
Making the Final Purchase Decision
The final step is to consider the practical aspects of owning and using the device. A phone can have the best encryption in the world, but if it is difficult to use or lacks support, it will fail to provide effective protection. Your purchasing decision should balance security, usability, and long-term viability.

Before committing, ensure you have clarity on the following points:
- After-Sales Support: What level of technical support is offered? Secure phones can be complex, and having access to expert assistance is crucial. Check for 24/7 support options and clear communication channels.
- Warranty and Replacement Policy: Understand the terms of the warranty. Given the specialised nature of these devices, a clear and fair replacement or repair policy is an indicator of a professional organisation.
- Global Usability: If you travel frequently, confirm that the device and its secure communication services will function reliably across different countries and networks.
Choosing the best encrypted mobile phone is an investment in your digital sovereignty. By following this structured approach—evaluating the core features, conducting a thorough assessment, and considering the practicalities of ownership—you can confidently select a device that delivers the privacy and peace of mind you require.
Related Guides
External Resources
- Phone Reviews - Tom's Guide Expert phone reviews and buying advice
- Smartphone Reviews - TechCrunch Latest smartphone technology news and reviews
- Mobile Device Guide - CNET Comprehensive mobile device reviews and comparisons
FAQ
Discover Our Categories
How to Buy the Best Encrypted Cell Phone
Selecting the best encrypted mobile phone is a significant decision that extends beyond comparing technical specifications. It involves evaluating your personal security needs, understanding the value of an integrated ecosystem, and recognising what sets a premium secure device apart from standard consumer models. This guide will walk you through the key considerations to ensure you choose a device that offers not just encryption, but a complete, secure communications experience.
Assess Your Security and Lifestyle Requirements
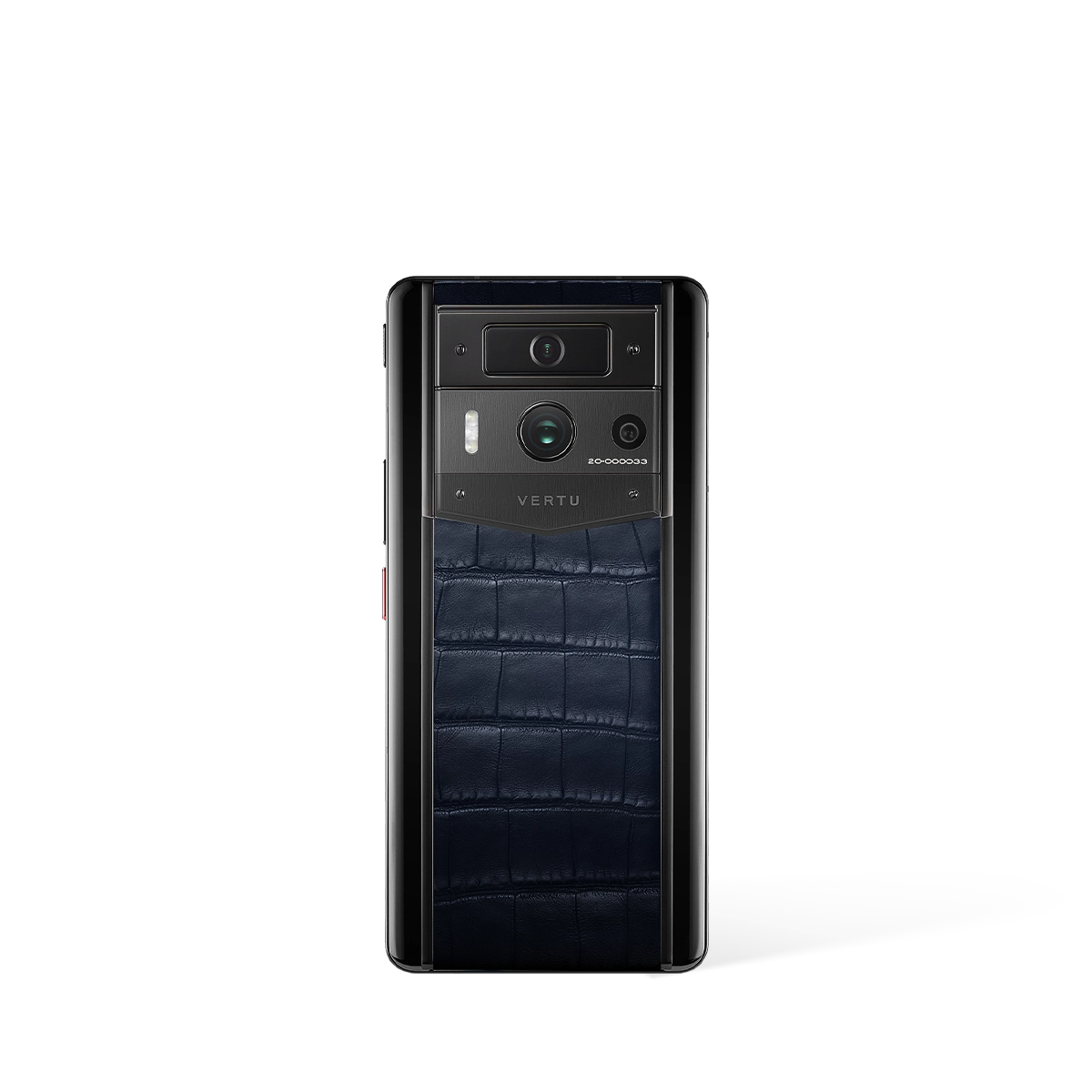
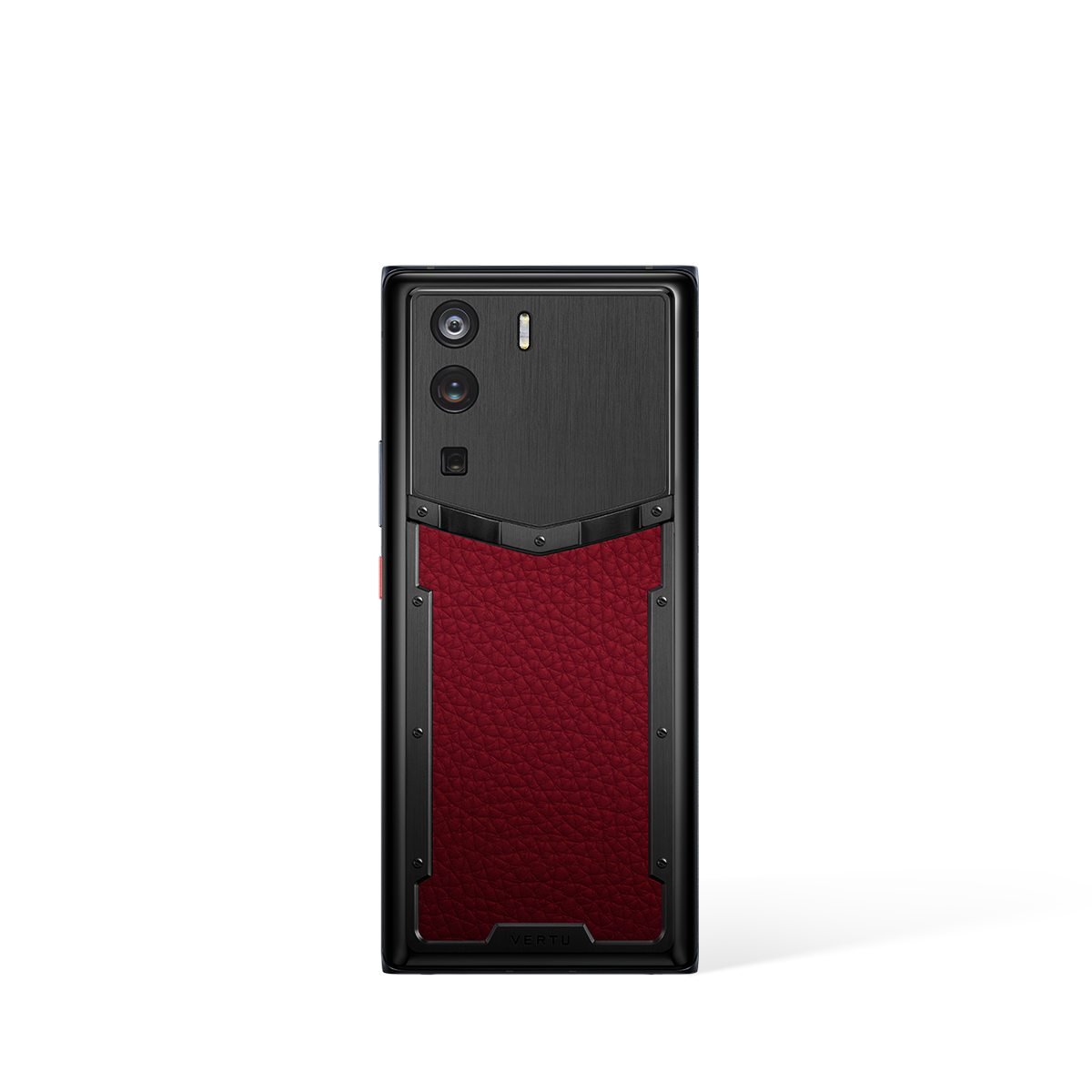
Before delving into specific models, the first step is to perform a thorough self-assessment. Are you a high-profile individual, an executive handling sensitive corporate data, or someone who simply values privacy above all else? The best encrypted phone for you will align with your unique threat model and lifestyle. A premium device like the METAVERTU MAX is designed for users who require an elevated level of security integrated seamlessly into a luxury experience.
Consider the ecosystem surrounding the device. True security is not just about the hardware; it encompasses the services and support that come with it. For instance, access to an exclusive concierge service, such as the RUBY KEY, indicates a commitment to a comprehensive user experience. This level of service suggests that the device is more than a tool; it is part of a secure and exclusive lifestyle, a factor that should heavily influence your purchasing decision.
Key Considerations for a Premium Secure Device
When you are ready to purchase, it is vital to look beyond marketing claims and focus on the tangible aspects of the product and its provider. The best encrypted phones are defined by a combination of dedicated hardware, exclusive services, and global accessibility. Use the following points as a checklist during your evaluation:
- A Singular Focus on Security: A truly secure phone is built from the ground up with privacy as its core principle. Look for brands whose primary offering is a secure device, such as the METAVERTU MAX, rather than a standard phone with added security software. This specialisation often translates to a more robust and reliable security architecture.
- Integrated Lifestyle Services: The value of a high-end encrypted phone is often enhanced by the exclusive services it provides. The availability of a dedicated concierge service like the RUBY KEY is a hallmark of a premium offering. This demonstrates that the manufacturer understands the needs of its clientele, providing support that extends far beyond technical assistance.
- Global Support and Logistics: For the discerning global citizen, the ability to purchase and receive support for their device anywhere in the world is paramount. Before committing, investigate the company's global shopping, payment, and shipping policies. A transparent and comprehensive FAQ section covering international logistics is a strong indicator of a reputable and customer-focused organisation.
Finalising Your Purchase with Confidence
Once you have identified a device that meets your criteria, the final stage is the purchase itself. For a specialised product like a high-end encrypted phone, the purchasing journey should be as secure and seamless as the device itself. Ensure you are buying from an official source to guarantee authenticity and access to all associated services.
Pay close attention to the terms regarding payment, shipping, and potential returns. A trustworthy provider will have clear and fair policies. Making this investment is about acquiring peace of mind, and that begins with a confident and transparent purchasing experience. By focusing on the complete package—the device, the services, and the brand's commitment to its customers—you can confidently select the best encrypted cell phone to protect your digital life.