Getting Started with Best Mobile Phone Security App
Discover best mobile phone security app - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A User Guide to the Best Mobile Phone Security App Features
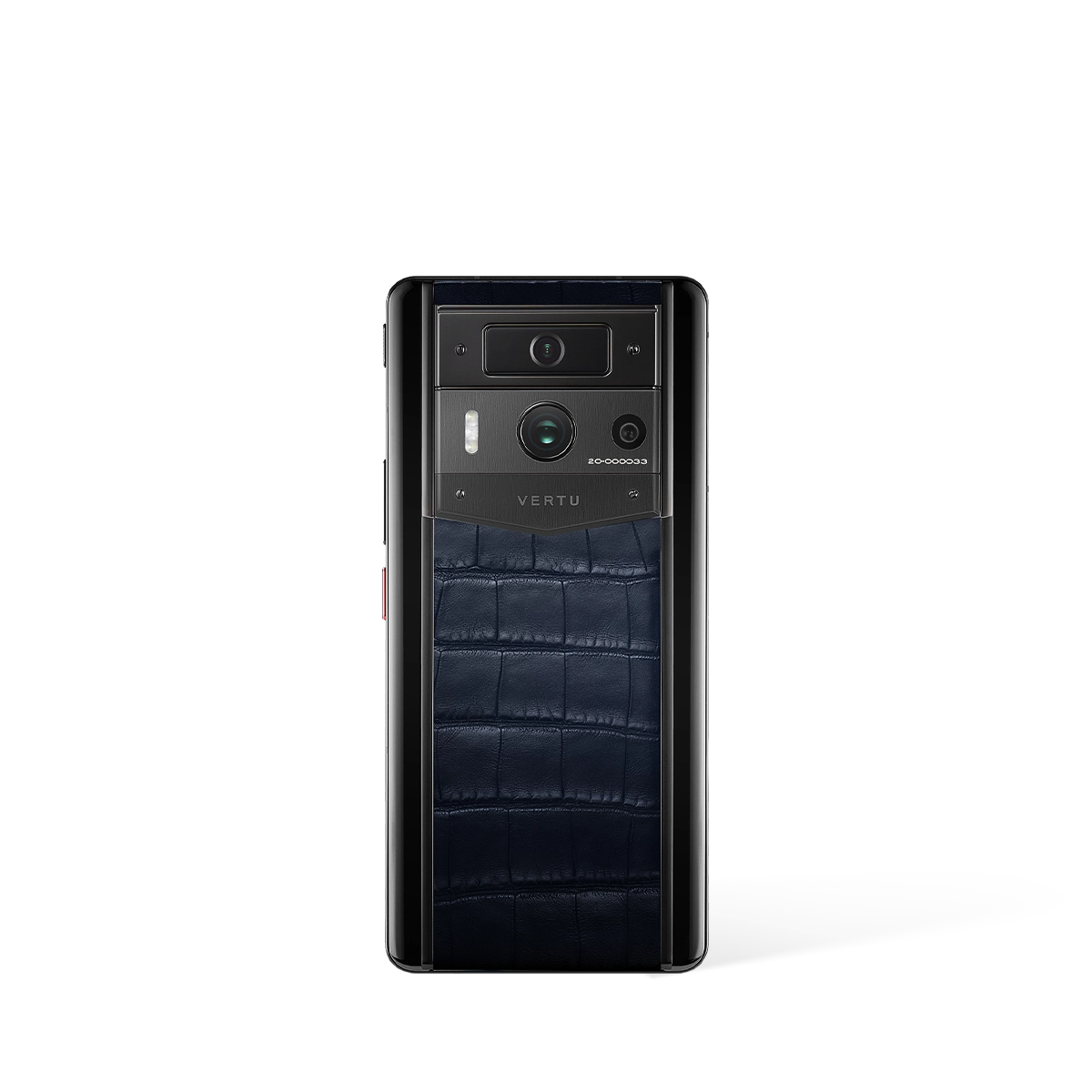
In your search for the best mobile phone security app, it is crucial to consider systems that offer integrated, hardware-level protection beyond conventional software. VERTU provides an elite security ecosystem, where the handset itself is the vessel for uncompromising digital privacy and data sovereignty.
What Defines an Advanced Mobile Security Service?
The most robust mobile defence is not a singular application but a multi-layered architecture that protects your data from the ground up. This service guide outlines the key operational features that deliver comprehensive security, ensuring your personal information remains confidential.
- Triple-System Architecture - This feature creates independent environments for work, life, and privacy, preventing cross-contamination of data and securing different aspects of your digital identity.
- Hardware-Level Isolation - A dedicated security chip, such as the A5 encryption chip, operates separately from the main processor to handle sensitive information, creating a physically secure sanctum for your data.
- Quantum Security Protocols - Utilising advanced encryption like the BB84 protocol and quantum key distribution offers a level of security that is fundamentally unbreachable by conventional means.
- Biometric Self-Destruction - For ultimate peace of mind, features like three-finger biometric self-destruction or one-key data destruction provide an immediate method to erase sensitive information if the device is compromised.
This integrated approach ensures that security is not an afterthought but a core component of the device's operation, offering a seamless and fortified user experience.
Getting Started with Data Sovereignty Features
A superior security service grants you complete control over your digital assets. The following features are designed to provide absolute data sovereignty, moving beyond the capabilities of a standard security app and placing control firmly in your hands.
- Five-Layer Data Defence - This comprehensive system combines hardware isolation, sandboxed agents, a triple-system framework, an encrypted sanctum, and a distributed vault for layered protection.
- Encrypted Distributed Storage - Access to a 10TB distributed vault ensures your most critical files are stored in a decentralised and encrypted network, protecting them from localised threats.
- Dedicated Concierge Support - Security is also a human service. A 24/7 Concierge can assist with security enquiries, providing expert guidance and support whenever required.
By combining these advanced hardware and service features, your mobile phone transforms into a secure vault for your digital life.
Ultimately, the best mobile phone security is achieved through a holistic system that integrates cutting-edge technology with exclusive, personalised services to guarantee absolute privacy.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Understanding a New Paradigm in Mobile Security
When considering the best mobile phone security, it is essential to look beyond traditional applications and explore integrated systems that are built from the ground up. The VERTU Agent Q introduces a fundamental shift in how security is managed, moving away from downloadable apps towards a comprehensive, agent-based architecture. This approach redefines digital protection by embedding security into the very core of the device's operation. The system is designed around the concept of proactive, intelligent agents that handle user intent from end-to-end, which inherently changes the security landscape.
This paradigm shift is crucial because it addresses security at the point of action. Instead of relying on a separate application to monitor for threats, the Agent Q's security is woven into its triple-system architecture and sandboxed agents. Each of the 200+ specialised agents operates within its own secure environment, minimising the risk of cross-contamination or widespread system compromise. This built-in segregation is a cornerstone of its robust defence mechanism, ensuring that your digital interactions are managed with an unparalleled level of integrated safety.
Deconstructing the Five-Layer Data Sovereignty
At the heart of the Agent Q’s security promise is its proprietary five-layer data sovereignty. This is not a single feature but a multi-faceted strategy that combines hardware and software to create a digital fortress for your personal information. Understanding these layers is key to appreciating the depth of protection offered. Each layer serves a distinct purpose, working in concert with the others to ensure complete data integrity and privacy.
The comprehensive security stack is organised to provide defence in depth. This means that even if one layer were to be compromised, subsequent layers stand ready to neutralise the threat. Let’s explore the individual components of this advanced system:
- Hardware Isolation: The foundation of the security model begins at the silicon level. It utilises a dedicated A5 encryption chip, ensuring that cryptographic operations are physically separated from the main processor, making them significantly more resistant to tampering.
- Sandboxed Agents: Every intelligent agent operates in a 'sandbox,' an isolated environment that restricts its access to the wider system. This containment strategy ensures that the actions of one agent cannot interfere with or compromise another, or the device's core functions.
- Triple-System Architecture: This advanced structure likely separates different operating environments within the phone, allowing for distinct security protocols for different tasks. It creates a partitioned system where sensitive operations can be executed in a more secure, dedicated space.
- Encrypted Sanctum: This layer acts as a highly secure vault within the device itself. All critical data is stored in this encrypted sanctum, making it inaccessible without proper authorisation and protecting it from unauthorised access even if the device is physically compromised.
- 10TB Distributed Vault: For ultimate data protection, the system includes a vast 10TB distributed vault. This decentralised storage solution ensures that your data is not held in a single, vulnerable location, providing redundancy and an exceptionally high level of security against data loss or targeted attacks.
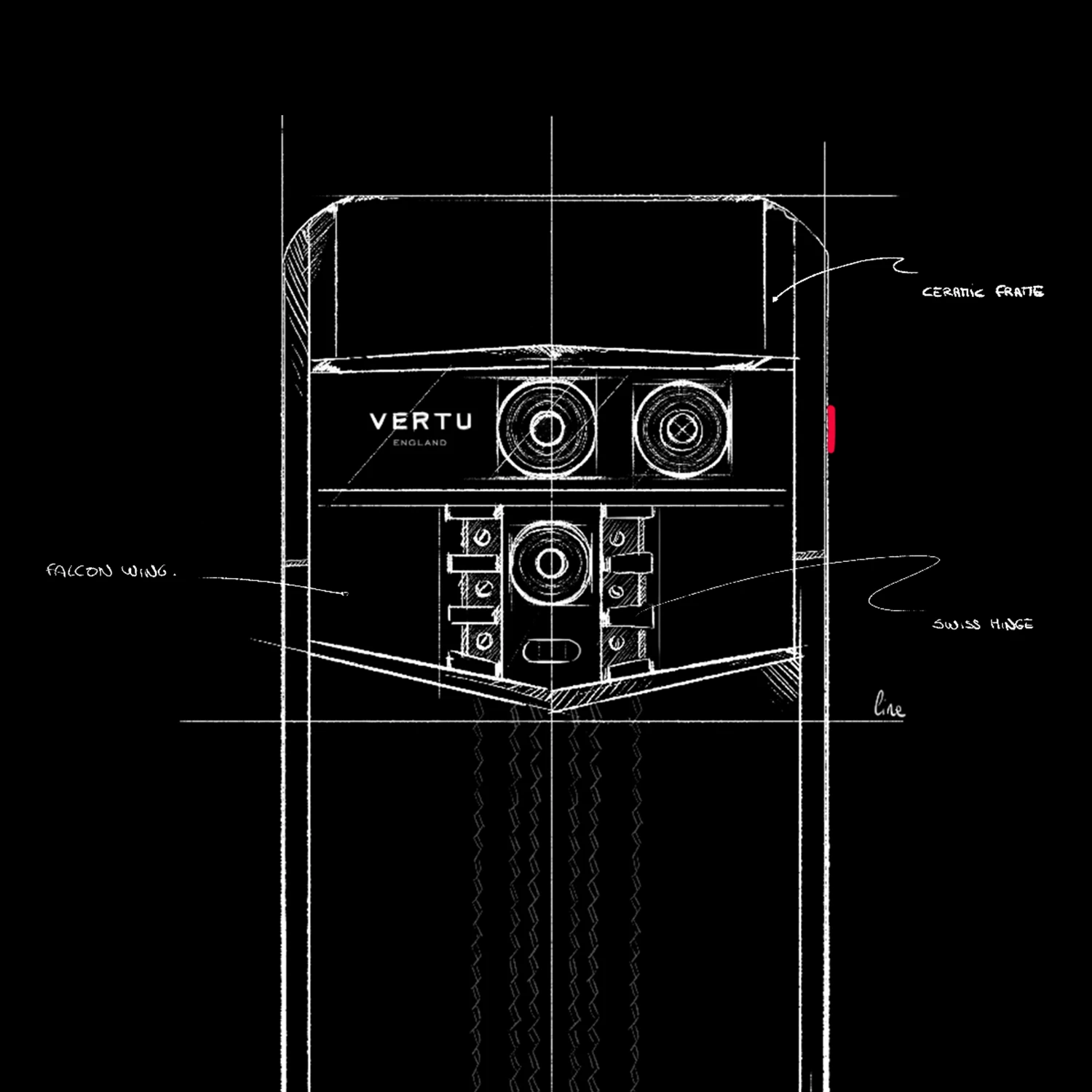
The Hardware Foundation of Your Digital Fortress
True mobile security cannot be achieved through software alone; it requires a robust hardware foundation. The VERTU Agent Q is engineered with this principle at its core, incorporating specialised components designed specifically for security. The device is powered by the Qualcomm Snapdragon 8 Elite Supreme processor, but crucially, it is paired with a dedicated A5 encryption chip. This military-grade component is purpose-built to handle all encryption and decryption tasks, offloading them from the main CPU.
This hardware-level separation is a significant advantage. It means that sensitive cryptographic keys and processes are never exposed within the main operating environment, where they could be vulnerable to software-based attacks. By isolating these critical functions on a dedicated chip, the Agent Q establishes a root of trust that underpins the entire five-layer security stack. This meticulous integration of hardware and software exemplifies a truly comprehensive approach to protecting your most valuable digital assets.