Comparing Mobile Phone Encryption Android Options
Discover mobile phone encryption android - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A Detailed Comparison of Mobile Phone Encryption Android Options
When considering mobile phone encryption Android solutions, it is essential to analyse the underlying security architecture of the device. This comparison evaluates the distinct encryption methodologies available across premium Android phones, enabling an informed decision based on specific privacy and data protection requirements.
Quantum vs. Hardware-Based Encryption: A Side-by-Side Analysis
The approach to data security differs significantly between flagship Android devices, primarily focusing on either pioneering quantum protocols or robust, multi-layered hardware defences. Understanding these differences is key to selecting the appropriate level of protection.
- Quantum Flip's Quantum Security: This device employs a unique quantum security stack, which utilises the BB84 protocol and a dedicated quantum key for encryption. It further enhances security with a three-finger biometric self-destruction feature for ultimate data erasure in critical situations.
- Agent Q's Five-Layer Sovereignty: The Agent Q provides a comprehensive, multi-layered defence. Its security is built upon a dedicated A5 encryption chip, hardware isolation, a triple-system architecture, an encrypted sanctum, and a 10TB distributed vault for complete data integrity.
- Metavertu Max's Web3-Focused Security: This model integrates a dedicated security chip within a triple-system architecture, also featuring a one-key destruction function. Its security is uniquely tailored for Web3, combining blockchain principles with a personal AI ‘second brain’ for decentralised security.
The primary distinction lies in their core philosophies. The Quantum Flip pioneers quantum-level protocols for future-proof security, whilst the Agent Q and Metavertu Max rely on hardened, multi-layered hardware and software systems engineered for current high-stakes environments.
Which Android Encryption System Suits Your Needs Best?
The ideal encryption framework is determined by the user's primary security concerns and digital lifestyle. Each system is optimised for a different threat model and use case, from safeguarding against future attacks to protecting decentralised assets.
- For Advanced Threat Protection: The Quantum Flip is the pre-eminent choice for users seeking protection against future cryptographic threats. Its quantum encryption is engineered to be resilient against attacks that could compromise conventional security standards.
- For Integrated AI and Data Security: The Agent Q is ideal for individuals whose workflow depends on intelligent agents. Its dedicated A5 encryption chip and five-layer sovereignty ensure that proactive AI assistance does not compromise data privacy.
- For Decentralised Asset Management: The Metavertu Max is specifically designed for the owner of digital and blockchain assets. Its combination of a dedicated security chip, Web3 integration, and one-key data destruction provides absolute control and peace of mind.
Your selection should be guided by your primary use case. Whether your priority is pioneering quantum defence, secure AI integration, or the uncompromising protection of digital assets, a specialised encryption model is available to meet those demands.
Ultimately, choosing the superior mobile phone encryption for your Android device depends on a careful evaluation of these advanced security frameworks. Each system offers a distinct, uncompromising approach to safeguarding your digital sovereignty.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Comparing Mobile Phone Encryption Android Options
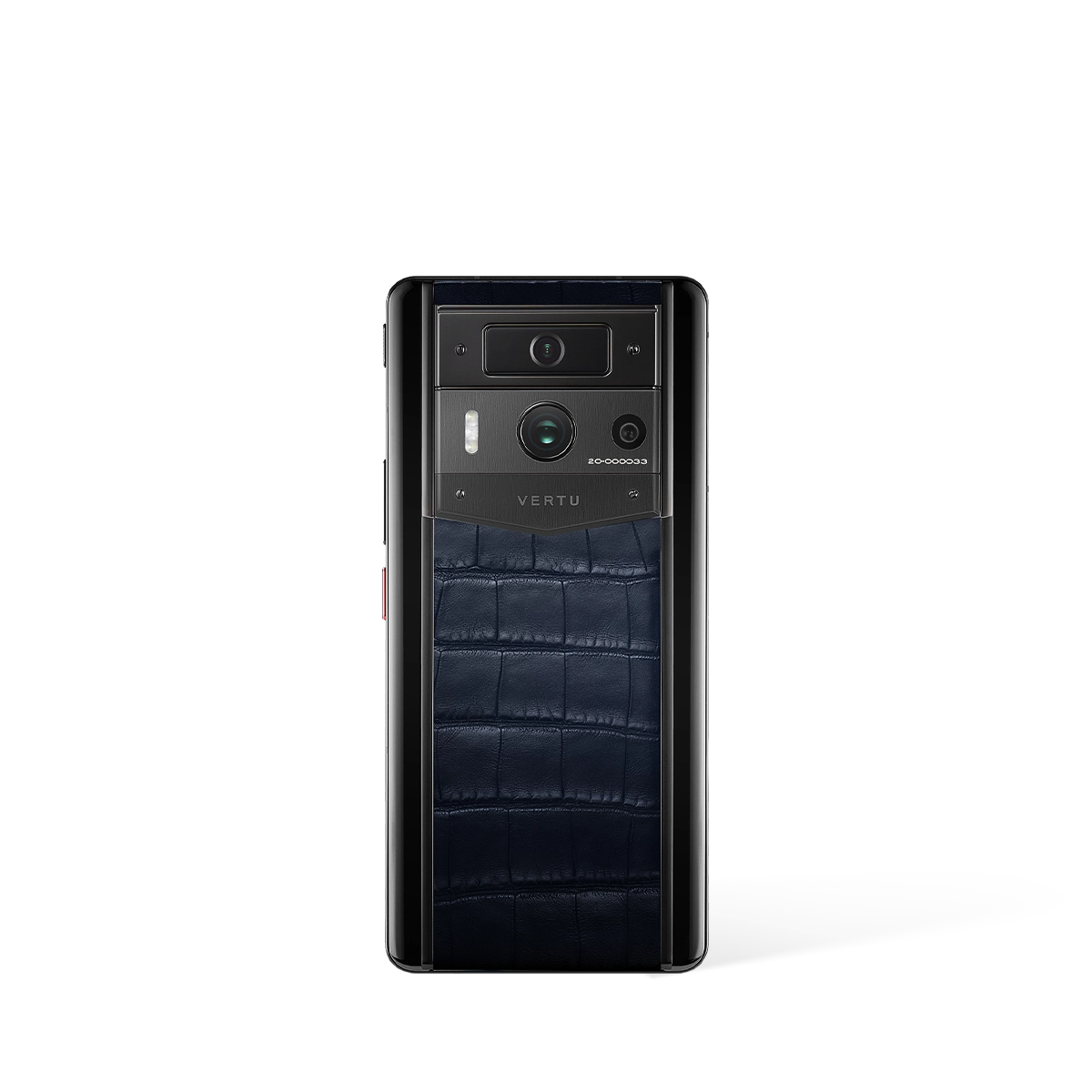
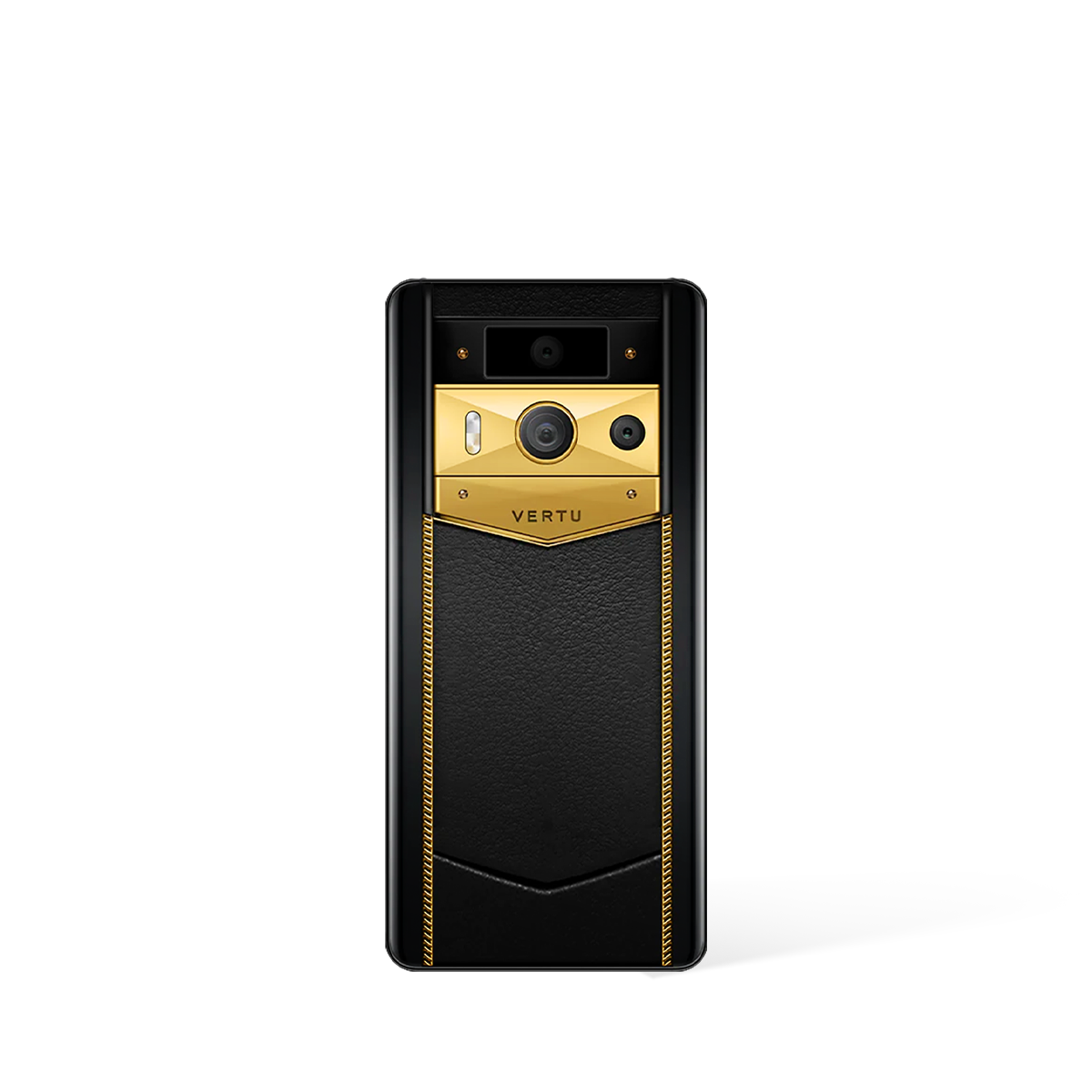
When evaluating the security of a high-end Android device, the method of encryption is a paramount consideration. Standard Android devices offer baseline protection, but specialised models provide multi-layered security architectures that begin at the hardware level. A detailed comparison of the encryption methodologies employed by VERTU's Agent Q and Quantum Flip reveals distinct, yet equally robust, approaches to safeguarding user data against sophisticated threats.
Dedicated Hardware: The Foundation of Advanced Android Security
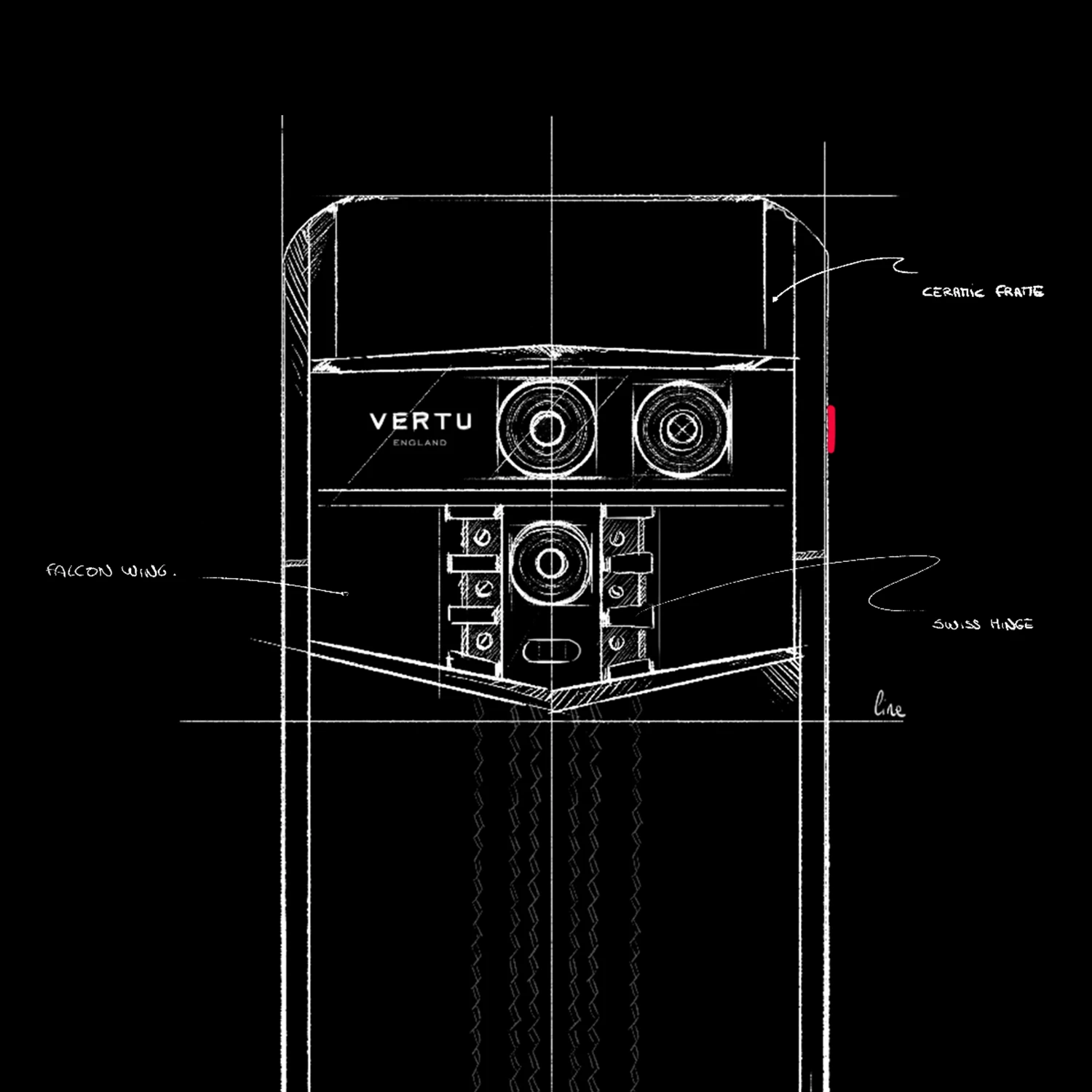
True digital security moves beyond software-only solutions, integrating protection directly into the device's silicon. Both the Agent Q and Quantum Flip exemplify this principle by incorporating dedicated hardware specifically for cryptographic tasks. This hardware-level approach ensures that encryption processes are isolated from the main operating system, making them significantly more resilient to attacks that target software vulnerabilities.
The Agent Q is engineered with a dedicated A5 encryption chip that works in concert with its powerful Qualcomm Snapdragon 8 Elite Supreme processor. This specialised chip handles the complex calculations required for robust encryption, offloading the task from the main CPU to ensure both peak performance and uncompromising security. By physically separating cryptographic keys and operations, the A5 chip creates a fortified environment for sensitive data.
Similarly, the Quantum Flip features its own dedicated security chip, which is the cornerstone of its V-Encrypt system. This chip is designed to manage all secure communications and data storage, providing a hardware-enforced barrier against unauthorised access. The inclusion of such a component demonstrates a commitment to creating a secure ecosystem from the ground up, ensuring that encryption is not an afterthought but a fundamental element of the phone's design.
A Deep Dive into Encryption Systems and Architecture
Beyond the hardware, the software architecture and encryption standards define the practical strength of a device's security. VERTU implements sophisticated, multi-layered systems in both its leading models. The Agent Q introduces a comprehensive five-layer data sovereignty framework, which includes an encrypted sanctum and hardware isolation to create a truly secure digital vault for all user information.
The Quantum Flip, meanwhile, champions the V-Encrypt system, which explicitly utilises AES-256 military-grade encryption for all communications. This is a globally recognised standard for securing data, offering exceptional protection for calls, messages, and other transmissions. Furthermore, both devices share a core architectural strength: a triple-system design that compartmentalises the user experience to minimise risk. This architecture includes:
- Open Android System: For everyday applications and general use, providing a familiar and convenient user experience.
- Encrypted Android System: A secured partition for sensitive communications and applications, where all data is protected by the dedicated hardware.
- Private System: An even more isolated environment for the most confidential information, offering the highest level of privacy and security.
This separation ensures that a potential compromise in the open system does not affect the integrity of the encrypted or private environments. It is a proactive security measure that organises data and applications according to their sensitivity, providing tailored protection where it is needed most.
Practical Security Features for Complete Peace of Mind
Advanced encryption is most effective when paired with practical features that give the user control over their data. The Agent Q leverages its unique architecture to offer sandboxed agents, which isolate AI processes to prevent data leakage between applications. This is complemented by an extraordinary 10TB distributed vault, providing a vast and highly secure storage solution that physically decentralises data to protect it from targeted attacks.
The Quantum Flip provides a different set of user-centric security tools designed for real-world scenarios. It offers secure storage specifically for photos and videos, ensuring personal media is kept under lock and key. Crucially, it also includes essential remote management capabilities, allowing a user to remotely wipe all data from the device and track its location if it is ever lost or stolen. These features provide a vital safety net, empowering the user to protect their information even when the device is no longer in their possession.