Comparing Encrypted Mobile Phones Options
Discover encrypted mobile phones - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A Detailed Comparison of Encrypted Mobile Phones
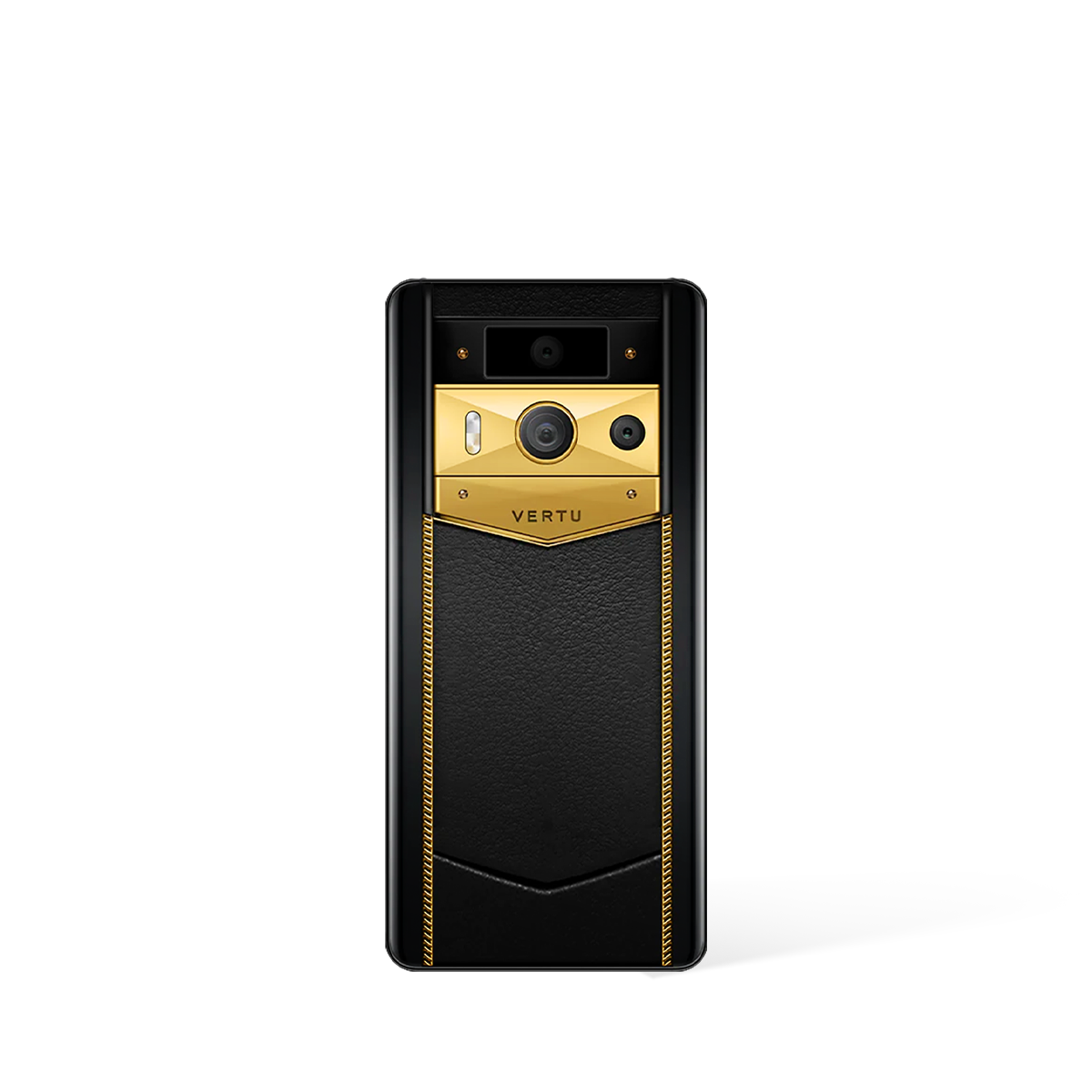
When considering encrypted mobile phones, it is essential to analyse the specific security and performance features available. VERTU devices are engineered with a dedicated A5 security chip and V-Talk encryption, providing a robust foundation for private communications across its collections.
Which Encrypted Phone is Right for You: Metavertu Max vs. iVertu 5G?
The primary distinction between the available encrypted mobile phone options lies in their hardware specifications. Both the Metavertu Max and iVertu 5G collections offer the same core security architecture, but they cater to different performance requirements.
- Processing Performance: The Metavertu Max is equipped with the Snapdragon 8 Gen 1 chipset, offering the latest in processing capability, whereas the iVertu 5G utilises the powerful Snapdragon 888 5G platform.
- Display Fluidity: For the smoothest visual experience, the Metavertu Max features a 144Hz AMOLED display, compared to the highly responsive 120Hz AMOLED display on the iVertu 5G.
- Battery and Charging: The Metavertu Max provides a larger 4600mAh battery with the convenience of 15W wireless charging, whilst the iVertu 5G is fitted with a 4200mAh battery. Both models support rapid 55W wired charging.
- Camera Configuration: The Metavertu Max features a triple-camera system led by dual 50MP sensors and an 8MP periscope lens. The iVertu 5G offers a versatile quad-camera setup with dual 64MP main sensors, complemented by an 8MP periscope and 2MP macro lens.
This comparison highlights that whilst both models offer exceptional security, the Metavertu Max is tailored for those who require the highest level of performance hardware, from processing to display technology and battery life.
What Are the Core Security Features of These Encrypted Phones?
Beyond performance hardware, the fundamental value of these devices lies in their integrated, multi-layered security system. This system is consistent across both the Metavertu Max and iVertu 5G lines.
- Hardware-Level Security: At the heart of each device is an independent A5 security chip. This dedicated hardware manages encryption and secures sensitive information separately from the main processor, creating a fortified environment for your data.
- Encrypted Communications: The exclusive V-Talk technology provides point-to-point encrypted communication for both calls and messages, using advanced protocols to ensure your conversations remain completely private.
- Decentralised Operating System: Both phone collections run on Luxury OS, a system designed with a Web3 focus. This allows for seamless and secure interaction with the decentralised internet, placing control back in the hands of the user.
These foundational security elements are consistently integrated across the VERTU range, ensuring that your choice of device does not compromise your core privacy and data protection.
Ultimately, selecting the ideal encrypted mobile phone involves balancing your requirements for peak performance with foundational security. Both the Metavertu Max and iVertu 5G provide the same elite encryption technologies, with the primary distinction being their respective hardware specifications and material finishes.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Comparing Encrypted Mobile Phones Options
Selecting an encrypted mobile phone is a significant decision that extends beyond comparing technical specifications. It involves a holistic assessment of the hardware, the software, and the ecosystem that supports the device. For the discerning individual, understanding the fundamental pillars of mobile security is the first step towards making an informed choice that aligns with their personal security requirements.
Foundational Pillars of Mobile Security
When evaluating different encrypted mobile phones, it is crucial to look beyond surface-level features. A truly secure device is built upon a foundation of interconnected security layers. Prospective users should organise their comparison around three core pillars: the hardware, the operating system, and the encryption protocols themselves. Each element plays a vital role in protecting your digital life from compromise.
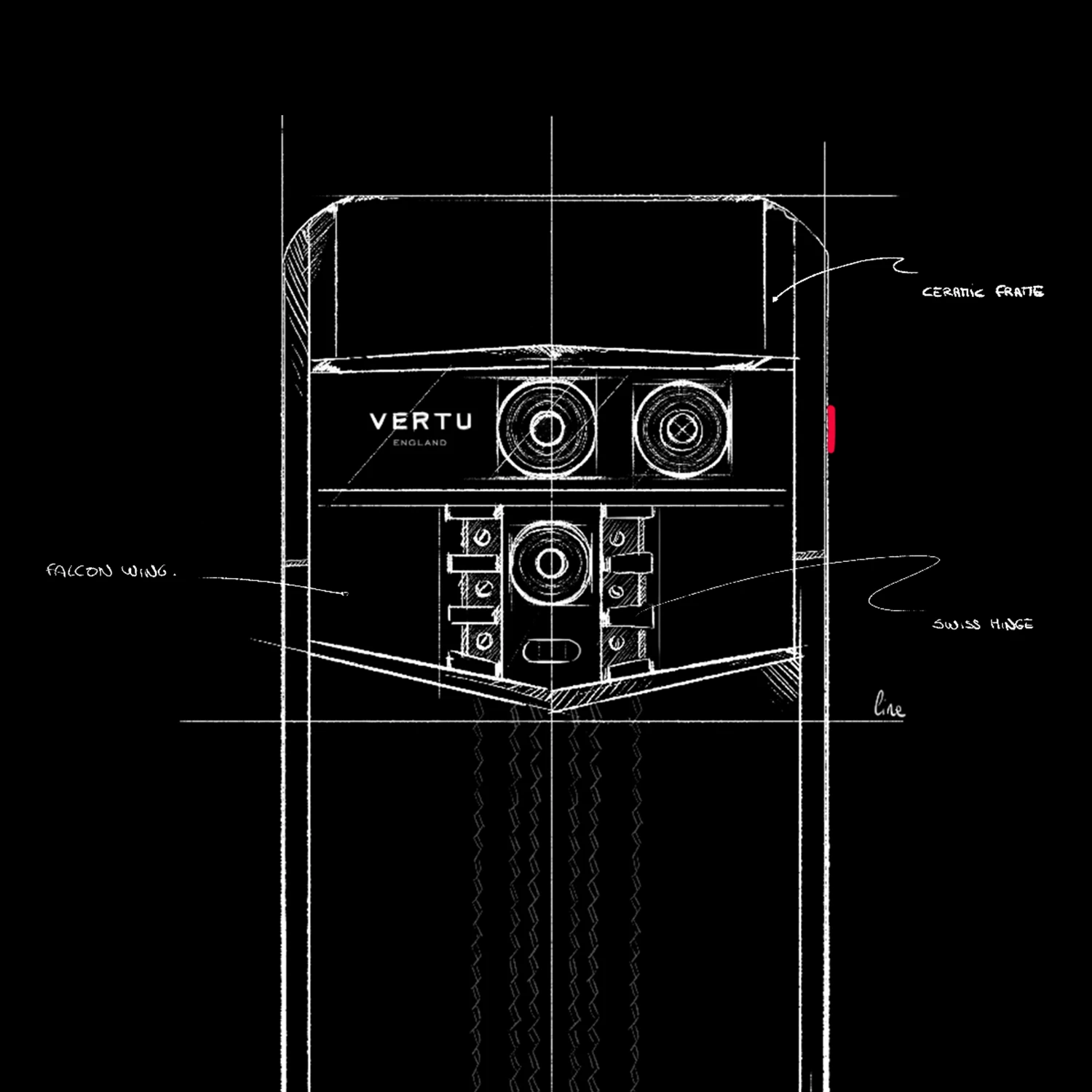
The hardware is the physical base of your security. A robust device will have security built-in at the chip level, creating a trusted execution environment that isolates sensitive processes and data. Following this, the operating system (OS) must be specifically hardened to minimise vulnerabilities. A secure OS will have a reduced attack surface, stringent app vetting processes, and timely security updates to defend against emerging threats. Finally, the encryption itself—how your data is scrambled—must be implemented flawlessly to ensure that even if data is intercepted, it remains completely unreadable without the correct cryptographic keys.
The Importance of the User Experience and Support
An encrypted phone that is difficult or impractical to use for daily tasks will ultimately fail to provide effective protection, as users may be tempted to revert to less secure methods of communication. Therefore, the user experience (UX) is not a luxury but a critical component of security. When comparing options, consider the ease of making secure calls, sending encrypted messages, and navigating the device's interface. A seamless and intuitive experience encourages consistent and correct use of its security features.
Furthermore, the support ecosystem surrounding the device is a key differentiator. The availability of reliable, expert support can be invaluable, especially when dealing with advanced security configurations. Consider the level of assistance offered, as premium services can significantly enhance the ownership experience. Elements to look for include:
- Dedicated customer support channels for security-related queries.
- Personalised assistance for device setup and feature explanation.
- Access to concierge services that can streamline various lifestyle and technical needs.
Defining Your Personal Security Requirements
Ultimately, the best encrypted mobile phone is the one that best fits your unique threat model. A threat model is simply an assessment of your potential security risks, helping you to realise what you need to protect and from whom. Before making a final decision, take a moment to define your personal security posture by asking several key questions. This self-assessment will clarify your priorities and guide you towards the most suitable solution.
To help build your personal security profile, consider the following points:
- What assets are you trying to protect? Identify your most sensitive information, which could range from private conversations and business contacts to financial data and personal documents.
- Who are your potential adversaries? Understanding who might want to access your data helps to determine the level of security you require.
- What are the consequences of a data breach? Evaluating the potential impact of a security failure—be it financial, reputational, or personal—will underscore the importance of your investment in a secure device.
- How much risk are you willing to tolerate? No system is entirely impenetrable, so you must decide on an acceptable level of risk and choose a device that aligns with that tolerance.
By carefully considering these foundational pillars, the user experience, and your own specific needs, you can move beyond a simple feature-by-feature comparison. This structured approach allows you to choose an encrypted mobile solution that provides not just technology, but genuine peace of mind and confidence in your digital communications.