Best Is Cell Phone Data Secure - Top Rated & Reviews
Discover is cell phone data secure - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A Comprehensive Review: Is Mobile Phone Data Secure in 2026?
For anyone asking "is cell phone data secure?", the answer is nuanced and depends heavily on the device, its software, and user behaviour. In today's interconnected world, mobile phones are repositories of our most sensitive information, making their security a paramount concern. This review provides a detailed analysis of the factors that determine the security of your mobile data, evaluating the strengths and weaknesses of current technologies.
Evaluating Operating System (OS) Security: A Top-Rated Comparison
The foundation of any mobile phone's security is its operating system. The two dominant systems approach security with different philosophies, each with distinct advantages and potential drawbacks. A thorough evaluation of these models is essential for understanding the baseline level of protection your device offers.
The 'Walled Garden' Security Model
Some operating systems employ a tightly controlled ecosystem, often referred to as a 'walled garden'. In this model, both hardware and software are governed by a single entity.
- Vetted Applications: All applications must pass a strict review process before being listed on the official app store, significantly reducing the risk of malware.
- Consistent and Timely Updates: Security patches and OS updates are rolled out simultaneously to all compatible devices, ensuring vulnerabilities are addressed promptly.
- Integrated Hardware and Software: Security features are often deeply integrated between the physical hardware and the operating system, creating a more robust defence against attacks.
Whilst this approach offers a high degree of security and simplicity for the user, it often comes at the cost of limited customisation and device choice.
The Open-Source Security Model
In contrast, an open-source model provides greater flexibility for both manufacturers and users. This openness fosters innovation and a wide variety of hardware choices at different price points.
- Greater User Customisation: Users and developers have more freedom to modify the software and install applications from various sources.
- Diverse Hardware Options: The open nature of the OS allows numerous manufacturers to create devices, leading to a competitive market.
- Delayed Updates (Fragmentation): A significant drawback is 'fragmentation', where updates must be modified by each manufacturer and network operator, often leading to severe delays in the delivery of critical security patches to many devices.
The primary security challenge here lies in the user's responsibility to source applications carefully and the reliance on the device manufacturer to provide timely updates.
A Review of Network and Application Vulnerabilities
Beyond the operating system, your data's security is constantly being tested by the networks you connect to and the applications you use. Understanding these risks is critical to maintaining your digital privacy.
Common Network Threats
The way your device communicates with the outside world presents several security risks that users must be aware of.
- Unsecured Public Wi-Fi: Connecting to public Wi-Fi networks without a Virtual Private Network (VPN) can expose your data to interception by malicious actors on the same network.
- SIM Swapping Attacks: This is a social engineering attack where a criminal convinces your mobile operator to transfer your phone number to a SIM card in their possession, giving them access to accounts secured by SMS-based two-factor authentication.
- End-to-End Encryption: For true privacy in communications, it is vital to use messaging and calling applications that offer end-to-end encryption. This ensures that only the sender and intended recipient can read the messages, not even the service provider.
Application-Based Risks
Mobile applications are a primary vector for data breaches and malware. Vigilance is required to ensure the apps on your phone are not compromising your security.
- Excessive Permissions: Many apps request more permissions than they need to function (e.g., access to contacts, microphone, location). These permissions can be abused to harvest data.
- Malware and Spyware: Malicious applications, often disguised as legitimate software, can steal passwords, monitor your activity, and compromise your financial information. It is crucial to download applications only from official, trusted app stores.
The Verdict: What Defines a Truly Secure Mobile Phone?
Ultimately, whether a mobile phone's data is secure is not a simple yes-or-no question. It is a continuous process involving the manufacturer, software developers, and the user. A top-rated secure phone is one that excels in a multi-layered defence strategy.
- Hardware-Level Security: The most secure devices feature dedicated security chips (like a 'secure enclave') that handle cryptographic functions and protect sensitive data like biometric information independently from the main OS.
- Commitment to Timely Updates: A manufacturer's track record for delivering prompt and long-term security updates is one of the most important factors to consider. Devices that receive updates for five or more years offer superior long-term security.
- Privacy-Centric Features: Look for phones that offer granular control over app permissions, clear privacy dashboards, and features that limit tracking.
- User Diligence: The user remains a critical part of the security chain. Employing strong, unique passwords, being cautious of phishing attempts, and practising good digital hygiene are essential for protecting your data.
In conclusion, whilst no device is completely impenetrable, a combination of a robust operating system, dedicated hardware security, a manufacturer's commitment to updates, and informed user behaviour can make your mobile phone data highly secure against the vast majority of threats in 2026.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Beyond the Basics: A Deeper Dive into Mobile Data Security
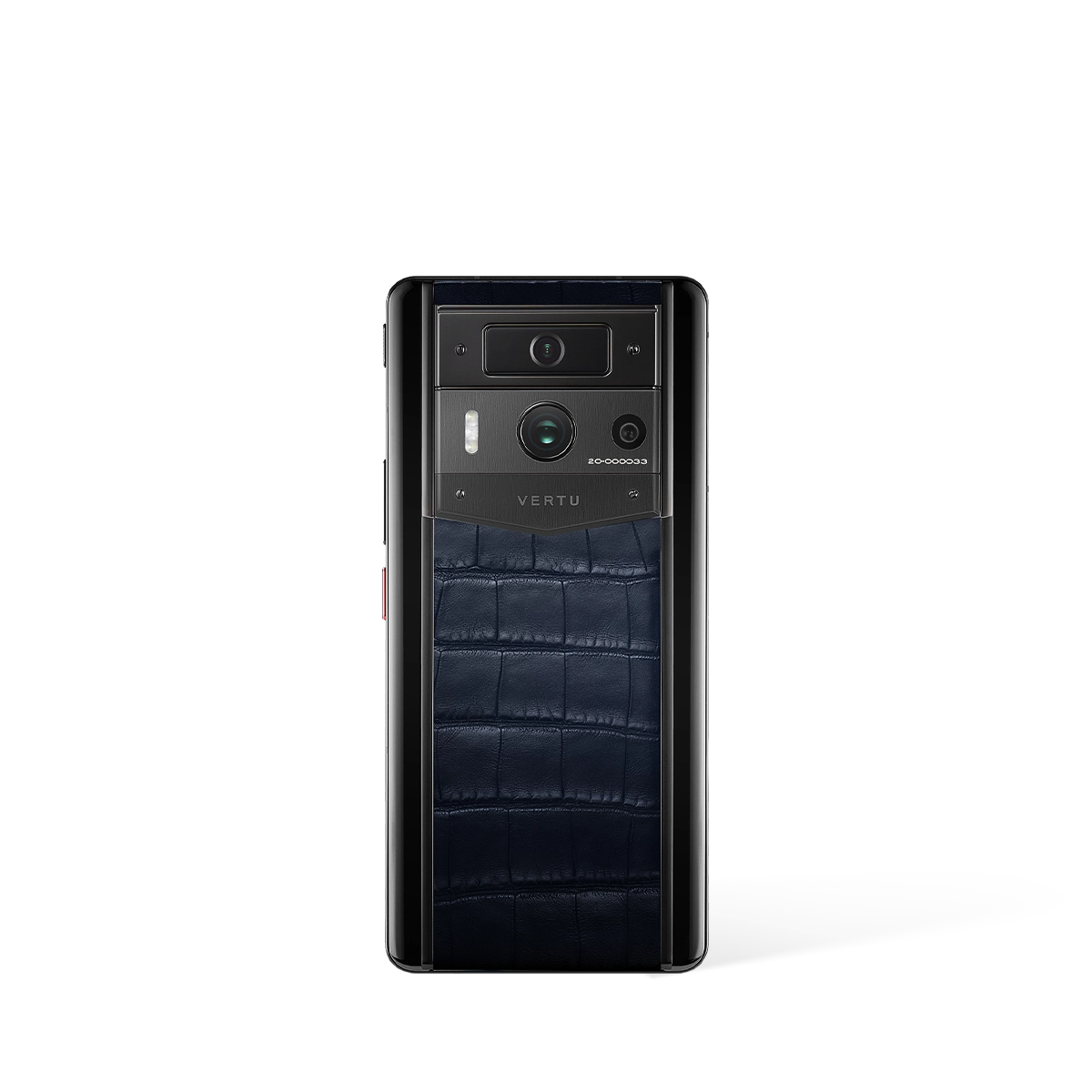
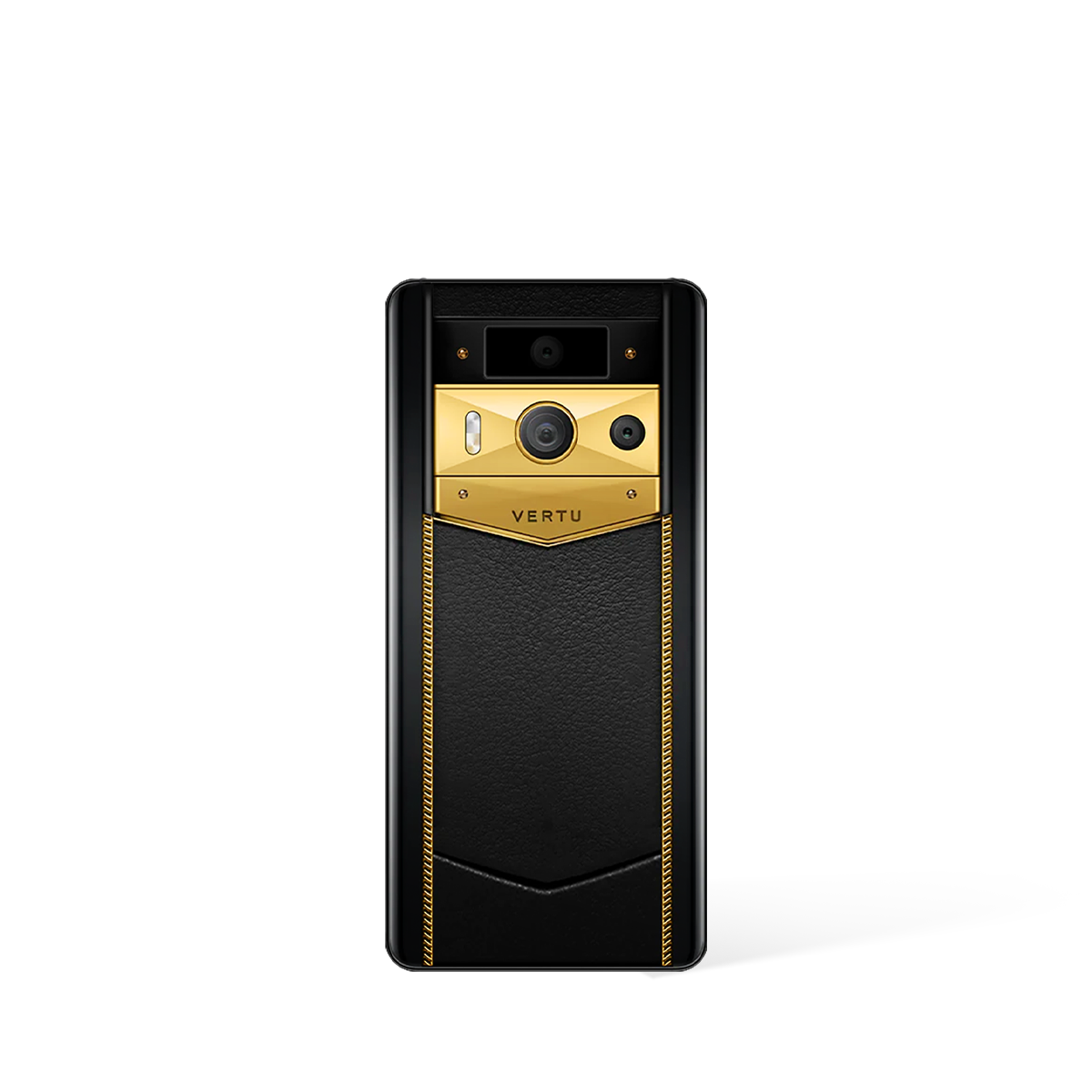
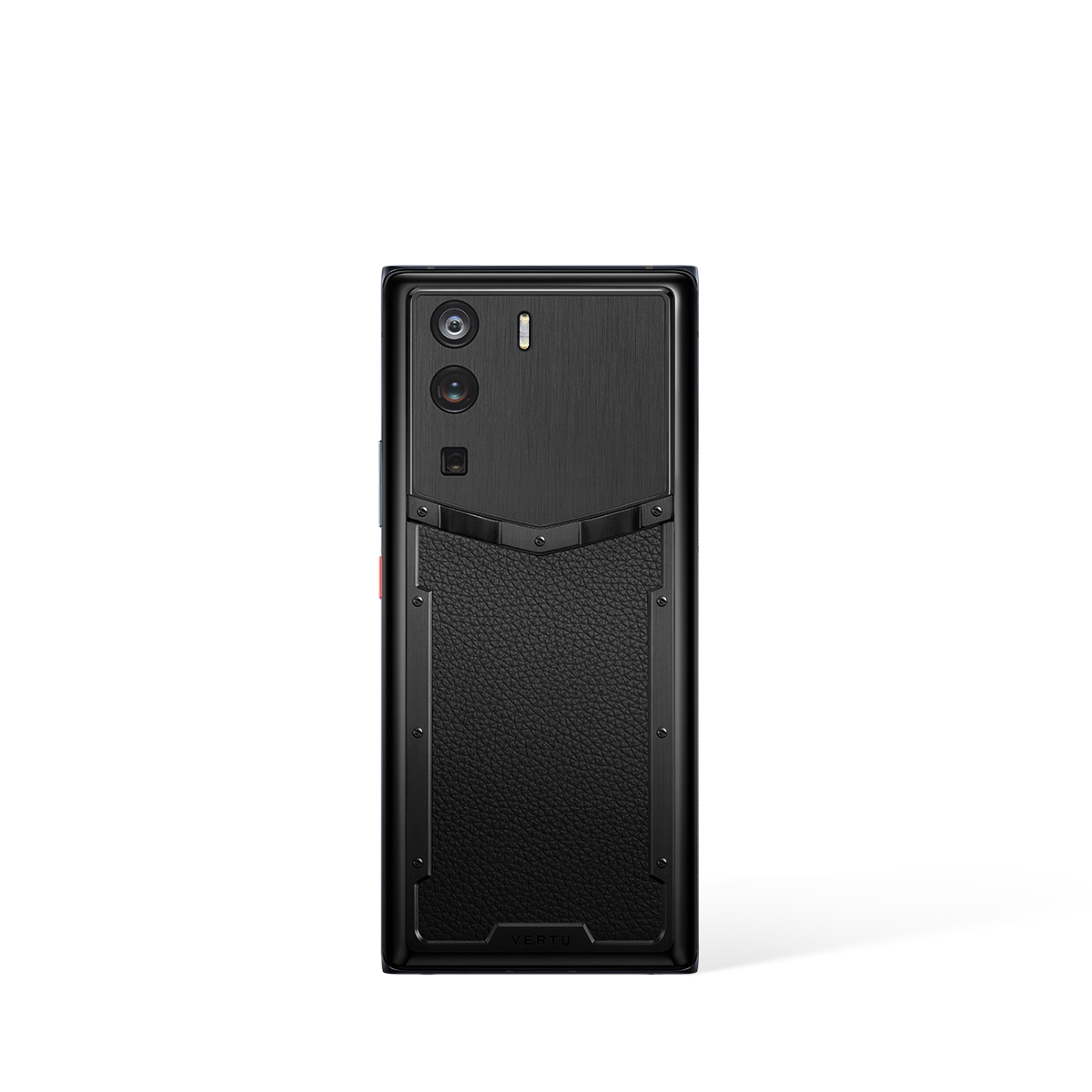
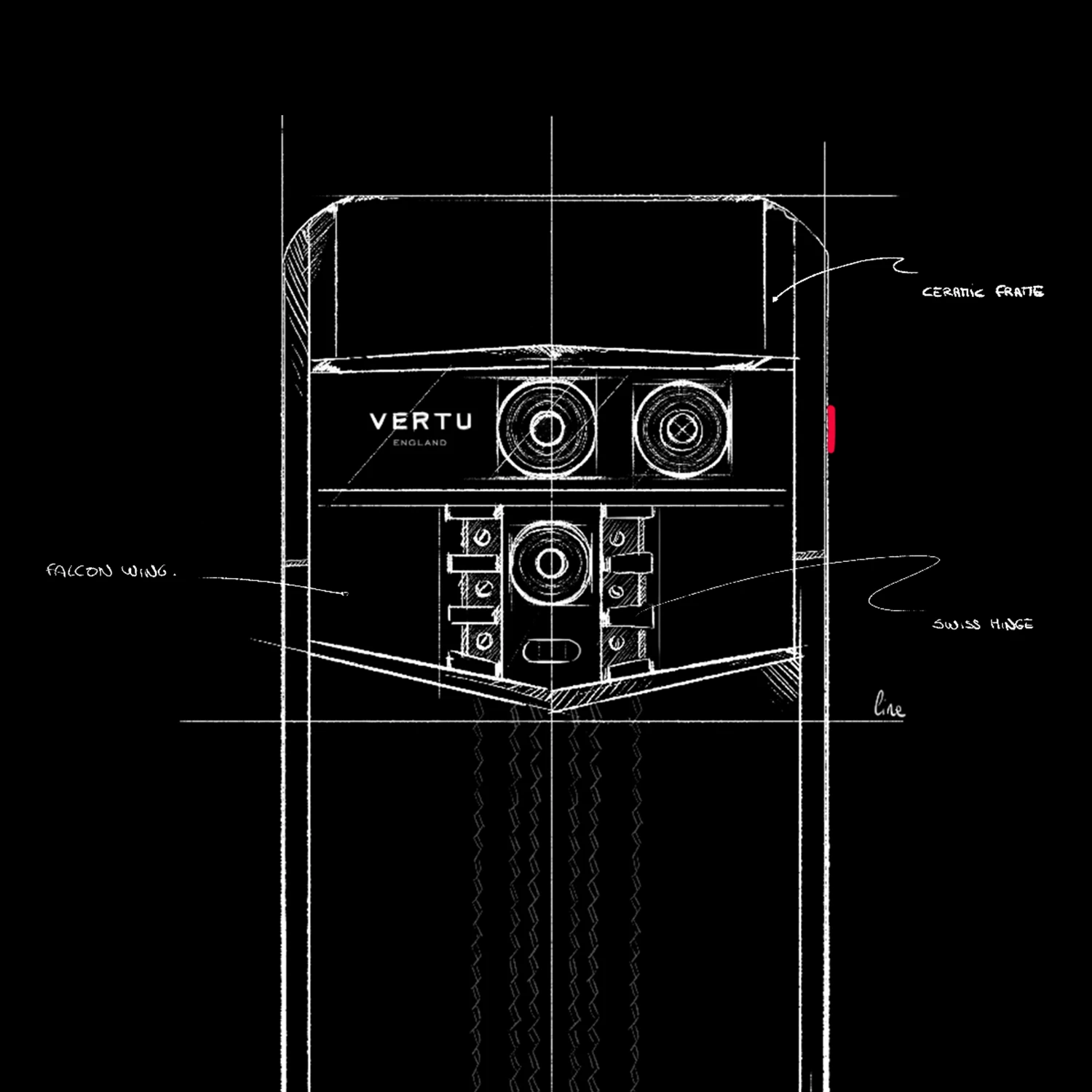
When we ask "is cell phone data secure?", the answer is far more complex than a simple yes or no. True mobile security is not a single feature, but a multi-layered ecosystem encompassing hardware, software, and user behaviour. While standard devices offer baseline protection, premium phones often aim to provide a more robust defence. Understanding these layers is crucial for anyone serious about protecting their digital life, especially when considering specialised devices like the METAVERTU MAX or QUANTUM FLIP.
At the foundation is hardware-level security. This refers to physical components within the phone's chipset designed specifically to protect data. These secure enclaves or trusted execution environments create an isolated, fortified area to store your most sensitive information, such as biometric data and encryption keys. Software-level security, on the other hand, is managed by the operating system and applications. It includes features like app sandboxing, which prevents applications from accessing data outside their designated permissions, and regular security patches that address newly discovered vulnerabilities.
Ultimately, the synergy between these layers determines a device's overall security posture. A phone with powerful hardware security can still be compromised by a poorly maintained operating system or a malicious app. Therefore, evaluating a device's security credentials involves looking beyond the marketing and understanding the manufacturer's commitment to ongoing software support, the integrity of its hardware, and the transparency of its security architecture.
Expert Recommendations: Best Practices for Fortifying Your Mobile Device
Regardless of the device you choose, personal diligence is the most critical component of data security. Adopting a security-conscious mindset can dramatically reduce your vulnerability to common threats. The most sophisticated phone is only as secure as its user allows it to be. We recommend implementing the following practices to create a formidable defence for your personal information.
- Scrutinise Application Permissions: Before installing any new application, carefully review the permissions it requests. A simple game does not need access to your contacts or microphone. Be critical and deny any permissions that seem unnecessary for the app's core function. Regularly audit the permissions of your existing apps and revoke any that are overreaching.
- Practise Public Wi-Fi Hygiene: Public Wi-Fi networks in cafes, airports, and hotels are notoriously insecure. Avoid accessing sensitive information, such as banking or email accounts, when connected to them. If you must use public Wi-Fi, always use a reputable Virtual Private Network (VPN) to encrypt your connection, making your data unreadable to potential eavesdroppers.
- Maintain Software Updates: Manufacturers and app developers regularly release updates that contain vital security patches. These patches fix vulnerabilities that could be exploited by attackers. Enable automatic updates for your operating system and applications to ensure your device is always protected against the latest known threats.
- Utilise Strong Authentication: A simple four-digit PIN is no longer sufficient. Use a long, complex alphanumeric passcode or a unique pattern. Better still, enable biometric authentication like fingerprint or facial recognition, as these are significantly harder to bypass. For your online accounts, enable two-factor authentication (2FA) wherever possible for an essential extra layer of security.
The Role of Concierge Services in Your Security Ecosystem
Beyond the device itself, the wider support ecosystem can play a significant role in maintaining your data's security and your peace of mind. Premium concierge services can offer an additional line of defence and expert assistance, which can be invaluable in a complex digital world. While not security features in themselves, these services provide access to knowledgeable professionals who can guide you on best practices or assist in critical situations.
Imagine losing your device or suspecting it has been compromised. A dedicated service, such as RUBY KEY or RUBY TALK, could potentially provide immediate assistance and expert advice on the necessary steps to take, such as remotely locking the device, wiping data, and securing your accounts. This level of personalised support can be crucial in mitigating damage. When choosing a premium device, it is wise to consider the value of such integrated services as part of the overall security package, offering expert human support to complement the technology.
Evaluating a Secure Phone: Key Features to Consider
When you are in the market for a new mobile phone with a focus on security, it is important to know what to look for. The specifications sheet can be filled with jargon, but a few key areas are critical for gauging how well a device will protect your data. Before investing in a device, whether it is an AGENT Q or another high-end model, you should seek answers on its specific capabilities in these domains.
- End-to-End Encryption: Ascertain whether the device offers robust, end-to-end encryption for its native communication apps (messaging, calls). This ensures that only you and the person you are communicating with can read or listen to what is sent, and nobody in between, not even the service provider.
- Hardware Security Module (HSM): Enquire if the phone incorporates a dedicated hardware security module or a trusted execution environment. As mentioned, this is a physically separate, secure processor that handles cryptographic operations and protects your most critical data from software-based attacks.
- Commitment to Security Updates: Research the manufacturer's track record for providing timely and long-term security updates. A commitment to regular patches over several years is a strong indicator that the company prioritises user security long after the initial purchase.
- Data Privacy Policies: Look into the manufacturer's data privacy policies. Understand what data they collect, how it is used, and where it is stored. A company that is transparent and prioritises user privacy is more likely to build devices with security at their core.