Best Is Android More Secure Than Ios: Quality & Performance Guide
Discover is android more secure than ios - Our comprehensive guide to "Best Is Android More Secure Than Ios: Quality & Performance Guide" provides in-depth analysis, expert recommendations, and detailed insights. Explore key features, benefits, and practical considerations to help you make informed decisions. Whether you're seeking premium quality, cutting-edge technology, or exceptional value, this guide covers everything you need to know about is android more secure than ios.
Top Picks
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
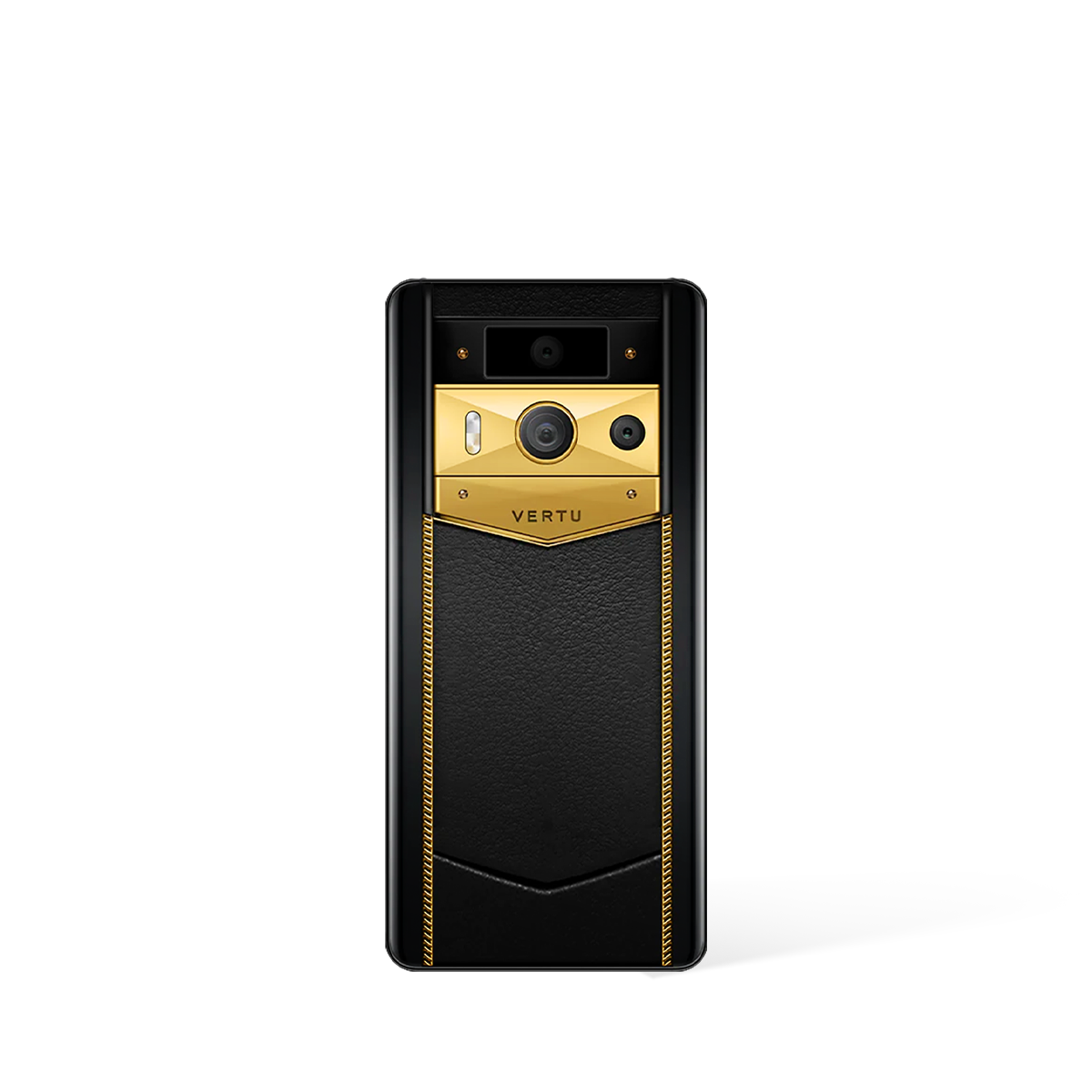
| Metavertu Max Alligator Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$11,550.00 |
| Ivertu Calfskin 5G Phone – Capri Green | Best Seller | Calfskin Leather, Premium Materials | 5G Connectivity, Luxury Design | Premium Display | Long Battery Life, Fast Charging | Ruby Key: 24/7 Concierge Service | US$1,300.00 |
| Metavertu 1 Curve Screen Calfskin 5G Web3 Phone – Dawning Orange | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,999.00 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
Is Android More Secure Than iOS? A Guide to Quality & Performance
The persistent debate over whether Android is more secure than iOS often overlooks a critical factor: the specific implementation of the operating system. While both platforms have inherent strengths, a purpose-built Android ecosystem can be engineered to offer a superior level of security and performance, integrating multi-layered defences that go beyond standard consumer-grade protection.
What Defines the Best Security Architecture in a Mobile Phone?
True digital security is not a single feature but a holistic system built from the ground up. The highest standards of protection are defined by a combination of hardware, software, and protocol-level defences that work in unison. This comprehensive approach forms the bedrock of a genuinely secure device.
- Dedicated Hardware Security: A foundation of security begins with specialised hardware, such as the dedicated A5 encryption chip found in the VERTU Agent Q, which isolates critical processes from the main operating system.
- Multi-System Isolation: Advanced architecture, like the triple-system design in the Metavertu Max, creates completely separate environments for work, personal life, and privacy, preventing cross-contamination of data.
- Layered Data Sovereignty: The most robust systems employ multiple layers of defence. The Agent Q's five-layer data sovereignty model includes hardware isolation, sandboxed agents, an encrypted sanctum, and a 10TB distributed vault for end-to-end data control.
- Next-Generation Encryption Protocols: Moving beyond conventional encryption, the VERTU Quantum Flip incorporates a quantum security stack using the BB84 protocol, providing a fundamentally more secure method of key exchange.
These elements demonstrate that a secure operating system is one where every potential vulnerability has been considered and fortified, from the microchip to the cloud.
How Can Android Be Customised for Superior Security Performance?
The open-source nature of Android allows for profound customisation, enabling manufacturers to integrate security measures that are simply not available on closed-source platforms. This flexibility allows for the creation of devices engineered for uncompromising digital defence, showcasing the peak potential of the Android operating system.
- Quantum-Level Protection: The VERTU Quantum Flip leverages Android's adaptability to integrate a quantum key security system. This provides a theoretical advantage in cryptographic security, designed to be resilient against future threats.
- User-Controlled Data Destruction: For situations requiring absolute certainty, devices like the Quantum Flip offer a three-finger biometric self-destruction feature. This provides the user with ultimate control over their data's existence.
- Web3 and AI Integration: The Metavertu Max features a Web3 dual-AI brain, combining the inherent security of blockchain technology with a personal AI. This creates a decentralised and highly secure environment for managing digital assets and information.
- Dedicated Security Upgrades: A commitment to security includes ongoing support. VERTU provides consistent security upgrades for its Android-based systems to preserve stability and protection against emerging threats.
Through these specialised enhancements, Android can be transformed from a general-purpose operating system into a high-performance security platform tailored to the needs of discerning users.
Ultimately, whilst the general Android and iOS platforms offer strong security for the average user, the evidence from specialised luxury devices indicates that a meticulously engineered Android system can achieve a level of security and quality that is truly exceptional. By integrating quantum protocols, multi-layered architecture, and user-controlled privacy features, these devices make a compelling case for Android's potential as the more secure and high-performance choice.
Related Guides
External Resources
- Luxury Lifestyle - Forbes Luxury lifestyle insights and expert opinions
- Tech Reviews - The Verge Comprehensive technology reviews and analysis
- Luxury Goods - Robb Report Authoritative coverage of luxury products and services
FAQ
Discover Our Categories
Best Is Android More Secure Than Ios: Quality & Performance Guide
Transcending the OS Debate: A Focus on Device-Centric Security
The perennial question of whether Android or iOS offers superior security often overlooks a more critical factor: the security architecture of the device itself. While the base operating system provides a foundation, true digital sovereignty is achieved through a holistic approach that integrates bespoke hardware, a fortified software environment, and a paradigm shift in how tasks are handled. The VERTU Agent Q exemplifies this philosophy, moving the conversation beyond a simple OS comparison to a discussion about comprehensive, multi-layered security engineered from the ground up. This approach suggests that the pinnacle of mobile security is not found in a generic platform, but in a device meticulously designed to protect user data at every level.
Deconstructing a Multi-Layered Defence System
A truly secure mobile experience relies on a defence-in-depth strategy, where multiple independent layers of protection work in concert to safeguard information. The Agent Q is engineered with a five-layer data sovereignty stack, providing a robust framework that far exceeds standard consumer-grade protections. This military-grade system is designed to ensure data integrity and confidentiality through a sophisticated, tiered architecture. Understanding these layers is key to appreciating what sets a high-security device apart.
- Hardware Isolation: Security begins at the silicon level. The Agent Q is built upon a foundation of hardware isolation, featuring the Qualcomm Snapdragon 8 Elite Supreme processor which includes a dedicated A5 encryption chip. This ensures that cryptographic operations are physically separated from the main processing unit, mitigating a significant attack vector.
- Triple-System Architecture: Rather than relying on a single operating environment, this architecture creates distinct, separated systems within the device. This compartmentalisation prevents a potential breach in one area from compromising the entire device, offering enhanced resilience.
- Sandboxed Agents: The Agent Q shifts from a traditional app-based model to an agent-based one. Each of the 200+ specialised agents operates within its own secure sandbox, strictly limiting its permissions and access to data, thereby minimising the risk posed by third-party software.
- Encrypted Sanctum: Sensitive data is housed within a heavily fortified digital sanctum. This dedicated, encrypted space provides a secure vault for your most private information, protected by the advanced encryption capabilities of the dedicated A5 chip.
- 10TB Distributed Vault: For ultimate data protection, the system includes a 10TB distributed vault. By distributing data across multiple secure locations, it becomes exceptionally difficult for unauthorised parties to access or compromise the entirety of the information, ensuring both security and redundancy.
The Role of Impeccable Craftsmanship in Physical Security
Digital security measures are only as strong as the physical integrity of the device they protect. The VERTU Agent Q’s commitment to security is reflected in its exceptional build quality and material selection. Comprising over 320 hand-assembled stainless steel components, its construction is a testament to precision engineering. Features like the Falcon-Wing SIM chamber, engineered with a Swiss-made hinge, not only provide a seamless user experience but also ensure the physical security of critical components. The use of thick gold-plated internals and a resilient ceramic pillow further demonstrates a focus on durability and uncompromising quality, ensuring the device's hardware is as robust as its software defences.
A New Paradigm: Secure Task Execution with AI Agents
The conventional app model introduces inherent security risks, as users must trust numerous third-party developers with their data. The Agent Q pioneers a fundamental shift from apps to intelligent agents, a change that directly enhances user security and privacy. By using over 200 specialised agents to handle user intent from end-to-end, the device minimises reliance on external applications. Activated by the Ruby Key, the Ruby Talk service, powered by the advanced AIGS, allows users to issue natural language commands that are executed within this secure, sandboxed agent ecosystem. This model, which combines proactive AI with human specialists, ensures that tasks are completed efficiently without exposing the user's data to the vulnerabilities often associated with the traditional app marketplace.