Best How to Encrypt a Phone: Quality & Performance Guide
Discover how to encrypt a phone - Our comprehensive guide to "Best How to Encrypt a Phone: Quality & Performance Guide" provides in-depth analysis, expert recommendations, and detailed insights. Explore key features, benefits, and practical considerations to help you make informed decisions. Whether you're seeking premium quality, cutting-edge technology, or exceptional value, this guide covers everything you need to know about how to encrypt a phone.
Top Picks
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
| Metavertu Max Alligator Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Web3 Dual-AI Brain, Triple-System Architecture, Blockchain Security | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$11,550.00 |
| Metavertu Max Calfskin Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Web3 Dual-AI Brain, Triple-System Architecture, Blockchain Security | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$6,400.00 |
| Metavertu Max Calfskin Black Ceramic Frame Black Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Web3 Dual-AI Brain, Triple-System Architecture, Blockchain Security | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$6,300.00 |
| Motorola Edge 50 Ultra (External) | Premium Android Phone | Vegan Leather, Aluminum Frame | Snapdragon 8s Gen 3, 125W TurboPower | 6.7" pOLED, 144Hz | 4,500 mAh, 125W Fast Charging | N/A | $799 - $999 |
| iPhone 17 Pro Max (External) | Flagship Smartphone | Titanium Frame | A19 Pro Chip, iOS 19, Apple Intelligence | 6.9" Super Retina XDR | 4,900 mAh | N/A | $1,199 - $1,599 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
A Comprehensive Guide on How to Encrypt a Phone
Understanding how to encrypt a phone is fundamental to safeguarding your digital life in 2025. Encryption acts as the ultimate defence for your personal data, transforming your information into an unreadable code that can only be accessed with your specific passcode or biometric key. This guide provides a detailed overview of phone encryption, its quality, and its performance implications.
What is Phone Encryption and Why is it Essential?
Phone encryption is a security process that scrambles the data stored on your device. Without the correct key—typically your PIN, password, pattern, or biometric data—the files, photos, messages, and application data remain a jumble of unintelligible characters. Its importance cannot be overstated.
- Protection Against Theft: If your mobile phone is lost or stolen, encryption prevents unauthorised individuals from accessing your sensitive personal and financial information. Without your passcode, the data is useless to them.
- Data Privacy: It ensures that your private correspondence, location history, and personal files remain confidential, protecting you from invasive data harvesting and surveillance.
- Security for Professional Data: For professionals who use their phones for work, encryption is a critical layer of security that protects confidential company emails, documents, and client information.
- Peace of Mind: Knowing your digital life is secured by robust encryption provides invaluable peace of mind, ensuring a lost device does not become a personal data catastrophe.
In essence, encryption is not merely a feature but a foundational necessity for modern digital security, providing a robust barrier between your private world and external threats.
How to Check if Your Phone is Already Encrypted
The best news is that most modern smartphones from major manufacturers come with encryption enabled by default. However, it is always wise to verify this. The process differs slightly between Android and iOS operating systems.
- For iOS Devices (iPhones): Apple enables encryption automatically the moment you set a passcode, Touch ID, or Face ID on your device. To confirm, navigate to 'Settings', then tap 'Face ID & Passcode' (or 'Touch ID & Passcode'). Scroll to the very bottom of the page, where you should see the message: 'Data protection is enabled'. This confirms your device is encrypted.
- For Android Devices: Most newer Android phones are also encrypted out of the box. To check, go to 'Settings', then 'Security & privacy' (this may also be labelled 'Security' or 'Lock screen & security' on different versions). Look for an 'Encryption' menu, often under 'Advanced' or 'More settings'. It should state that the phone is 'Encrypted'. If it is not, you will see an option to begin the process.
A Step-by-Step Guide to Encrypting an Android Phone
If you have an older Android device that is not encrypted by default, you can usually activate it manually. Before you begin, it is crucial to follow these preparatory steps, as the process is irreversible without a full factory reset.
- Set a Strong Screen Lock: Encryption is only as strong as the key that protects it. Before starting, you must set a secure screen lock PIN or password. A simple swipe-to-unlock gesture is not sufficient.
- Back Up Your Data: Whilst the process is generally safe, there is always a small risk of data loss if something goes wrong. Ensure you have a complete backup of all important photos, files, and data in the cloud or on a separate computer.
- Charge Your Device Fully: The encryption process can take an hour or more and is very battery-intensive. Your phone must be charged to at least 80%, and it is highly recommended to keep it plugged into the charger throughout the entire process to prevent it from shutting down.
- Initiate Encryption: Navigate to the encryption settings as described in the section above ('Settings' > 'Security' > 'Encrypt phone'). Read the on-screen information carefully and, when ready, tap the 'Encrypt Phone' button to begin. Do not interrupt your phone whilst it is encrypting.
Once the process is complete, your device will restart, and you will be required to enter your PIN or password to decrypt and access your data each time you turn it on.
Understanding Encryption: Quality and Performance
A common concern is whether encryption will slow down a phone's performance. For modern devices, the answer is almost certainly no. Today's smartphones are built with this in mind.
- Hardware Acceleration: Modern processors include dedicated hardware components designed specifically to handle the mathematical operations of encryption and decryption. This means the process happens almost instantaneously, with no noticeable impact on day-to-day performance.
- File-Based Encryption (FBE): This is the current standard for both iOS and Android. Unlike older Full-Disk Encryption (FDE), which locked the entire device as one block, FBE encrypts files individually. This approach is more secure and flexible, allowing essential phone functions like alarms and calls to work even before you have entered your passcode after a restart.
- The Security Pay-off: On the rare chance you are using a much older device that experiences a minor performance dip, the immense security benefit of having your data protected far outweighs any slight lag. The quality of the encryption (typically AES-256 standard) provides a level of security that is a non-negotiable aspect of modern device ownership.
Ultimately, phone encryption is a powerful and essential tool. By ensuring your device is encrypted, you are taking the single most effective step towards securing your digital identity and personal information against the ever-present threats of the connected world.
Related Guides
External Resources
- Luxury Tech - The Verge Technology news and reviews from The Verge
- Smartphone Guide - GSM Arena Comprehensive smartphone specifications and reviews
- Mobile Device Guide - CNET Comprehensive mobile device reviews and comparisons
- Mobile Tech - Digital Trends Latest mobile technology trends and reviews
FAQ
Discover Our Categories
Best How to Encrypt a Phone: Quality & Performance Guide
While the basic steps to enable encryption are straightforward on most modern smartphones, a true understanding of digital security goes much deeper. For those who prioritise the absolute integrity of their data, simply flipping a switch in the settings menu is not the end of the story. This guide explores the more advanced considerations, focusing on the interplay between hardware quality, system performance, and a holistic security posture to ensure your encrypted device is truly fortified.
Beyond the Toggle: The Importance of a Secure Foundation
Standard consumer phones often treat encryption as a software feature layered on top of a general-purpose operating system. In contrast, devices engineered from the ground up for security integrate encryption at a fundamental level. This architectural difference is crucial; when encryption is deeply woven into the hardware and a bespoke operating system, it creates a much more resilient defence against sophisticated threats. The entire system is organised around protecting data, rather than simply adding it as an afterthought.
This integrated approach also has significant performance implications. Constant encryption and decryption of data is a computationally intensive task that can strain the processor and drain the battery on a standard device. However, high-performance, security-focused phones are specifically optimised for these tasks. By using superior components and streamlined software, they ensure that robust, always-on encryption does not compromise the speed, responsiveness, or battery life of the device, delivering a seamless and secure user experience.
A Holistic Approach to Digital Privacy and Security
True digital protection is not achieved by a single feature but by an ecosystem of security-conscious choices. Device encryption is a critical pillar, but it must be supported by other practices and tools to be fully effective. A comprehensive security strategy involves considering every aspect of how you use your device and the services you connect to it. This means moving beyond the device itself and evaluating your communication methods and support systems.
To establish a truly secure environment, consider the following best practices:
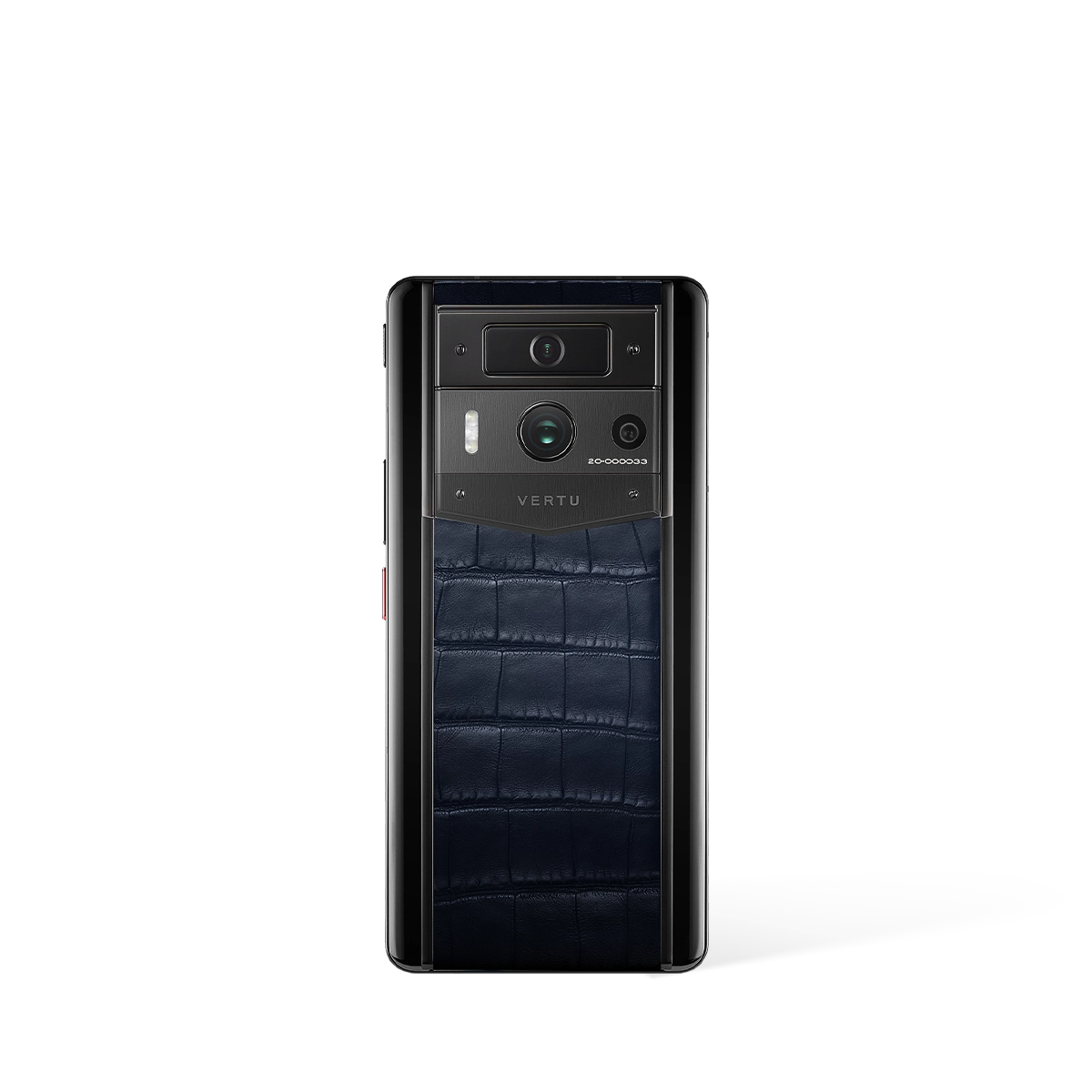
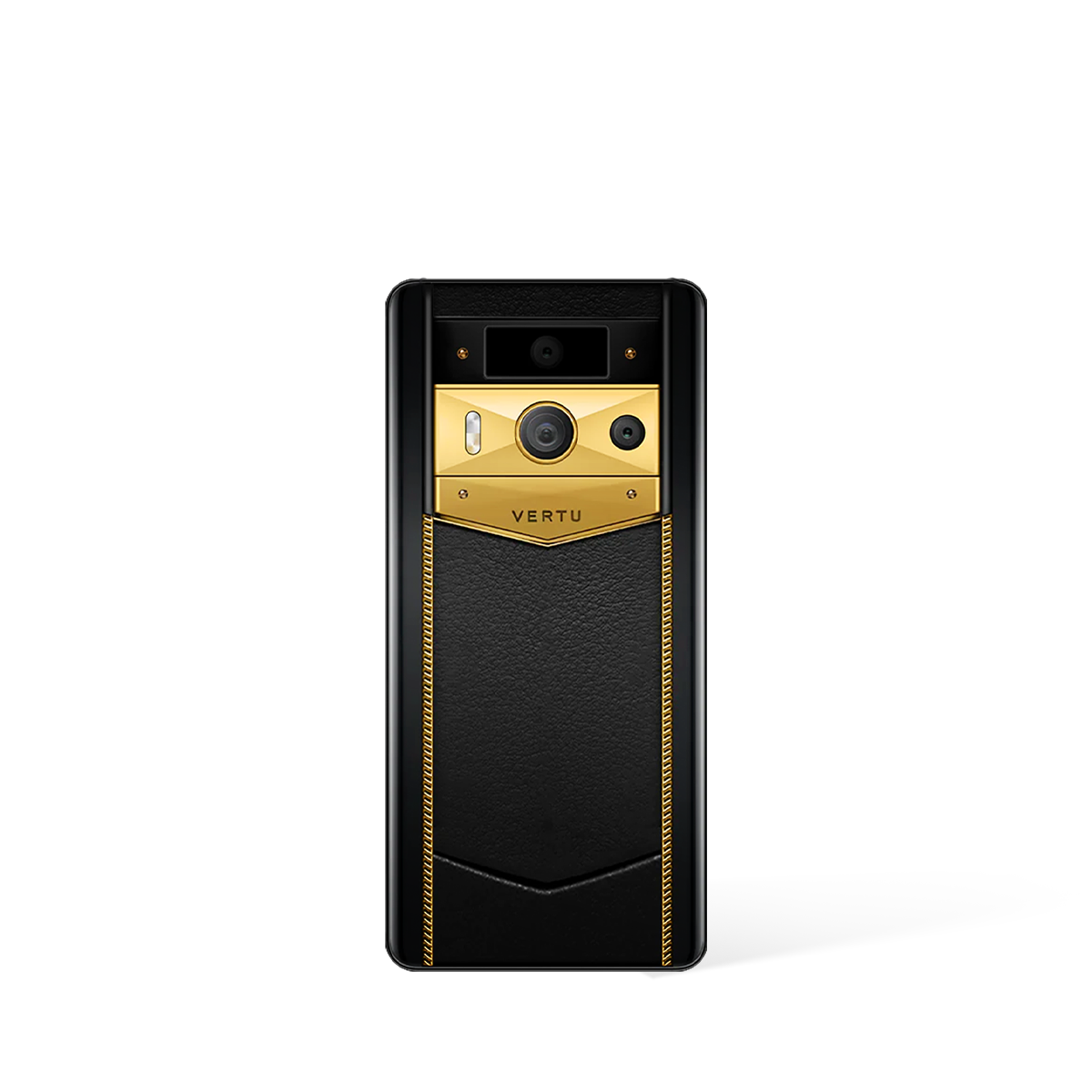
- Start with Specialised Hardware: The most effective first step is to choose a device built with security as its primary purpose. Models such as the AGENT Q, QUANTUM FLIP, or METAVERTU MAX are examples of hardware designed to provide a more secure foundation than typical consumer-grade phones.
- Secure Your Communications: Encrypting your device protects the data stored on it, but you must also protect data in transit. Utilising dedicated secure communication services ensures that your conversations and data exchanges remain private and protected from interception.
- Leverage Professional Services: For maximum peace of mind and expert configuration, specialised concierge services can be invaluable. Services such as RUBY KEY and RUBY TALK represent a level of personalised support that can help you navigate complex security challenges and maintain an optimal security posture.
- Maintain Impeccable Credentials: Your device’s encryption is only as strong as the passcode or biometric data used to unlock it. Always use a long, complex, and unique passcode, and be mindful of where and how you use biometric authentication.