Best Encrypted Phones: A 2026 User Guide to Digital Sovereignty
In an era where personal data has become the world's most valuable commodity, the demand for genuine digital privacy has never been more acute. Standard mobile phones, whilst powerful, often operate within ecosystems designed for data collection. For discerning individuals—from business leaders to public figures—this is an unacceptable compromise. This guide explores the world of the best encrypted phones, devices engineered from the ground up to protect your communications, identity, and digital assets. We will delve into what makes a phone truly secure and examine the leading options available in 2026 for those who believe privacy is the ultimate luxury.Why Your Digital Privacy is the New Ultimate Asset
The digital landscape of 2026 is fraught with risks that extend far beyond inconvenient marketing. Sophisticated cyber threats, state-level surveillance, and corporate data harvesting are pervasive. For high-net-worth individuals and executives, a compromised device can lead to financial loss, reputational damage, or the leaking of sensitive business intelligence. An encrypted phone is more than a communication tool; it is a vault for your digital life. It operates on the principle of **data sovereignty**—the fundamental idea that you, and only you, should control your information. Unlike mainstream devices that may send data to centralised servers, a truly secure phone is built to decentralise control, placing the keys to your digital kingdom firmly in your hands. This shift from being the product to being the owner of your data is the defining characteristic of a modern encrypted device.The Best Encrypted Phones of 2026: A Comparative Overview
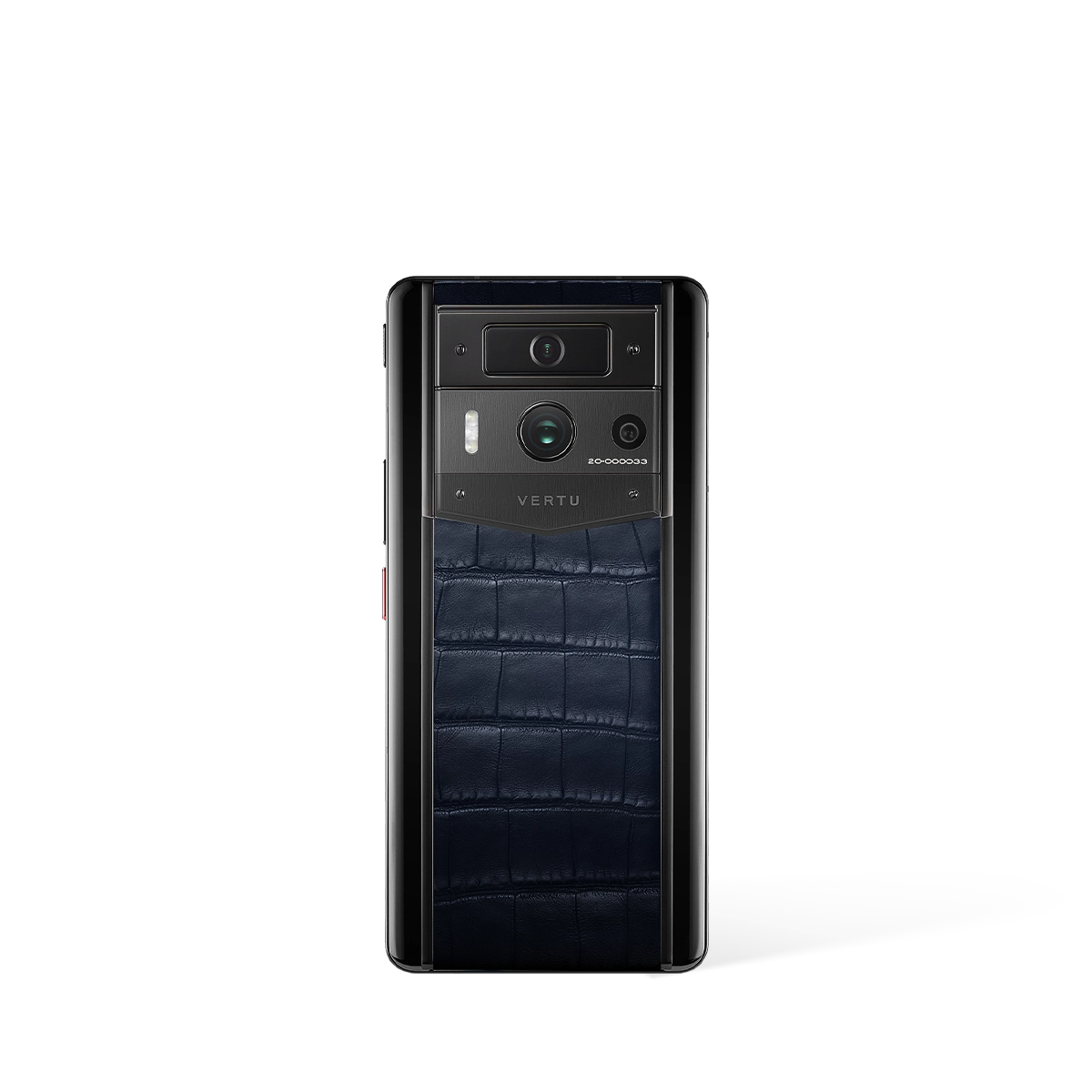
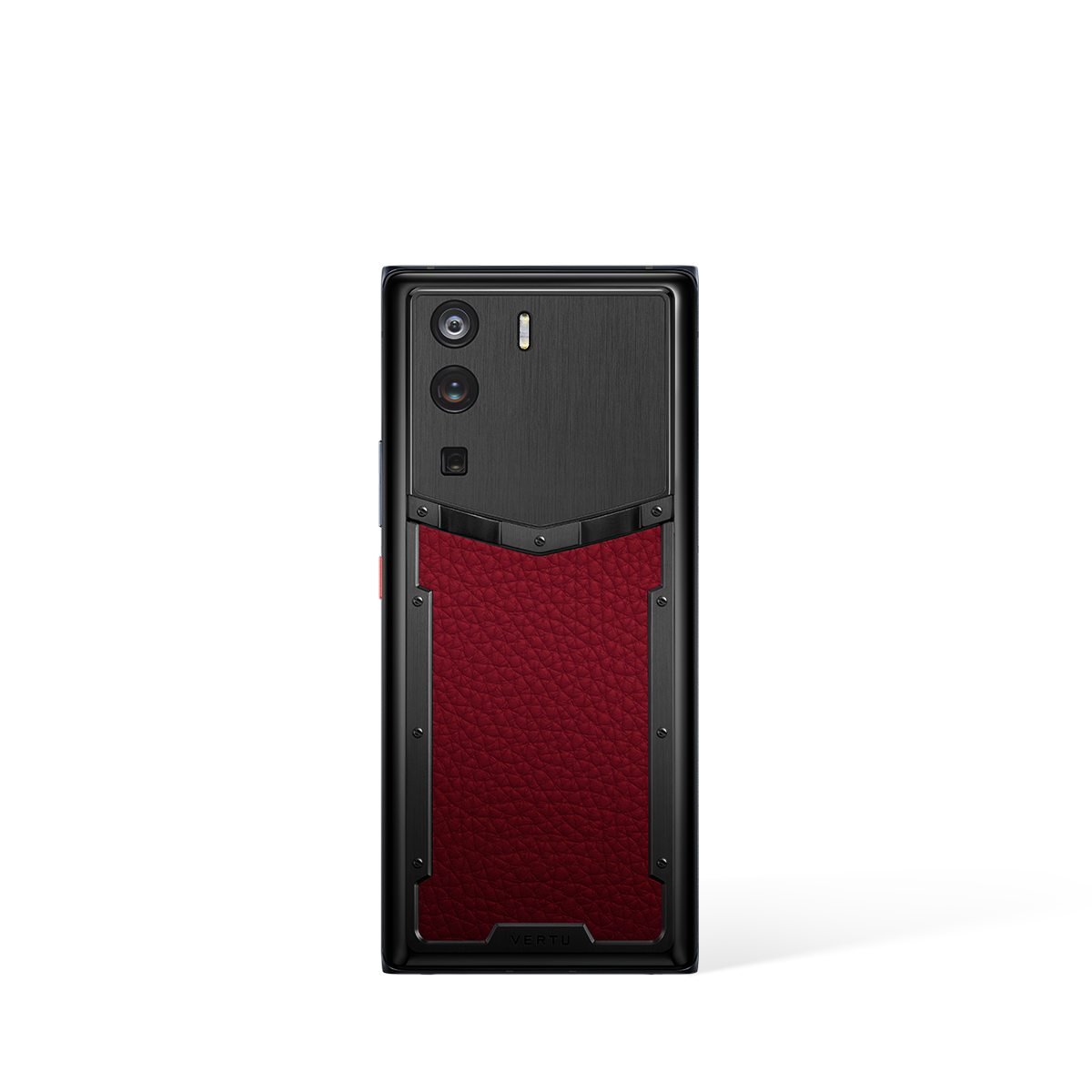
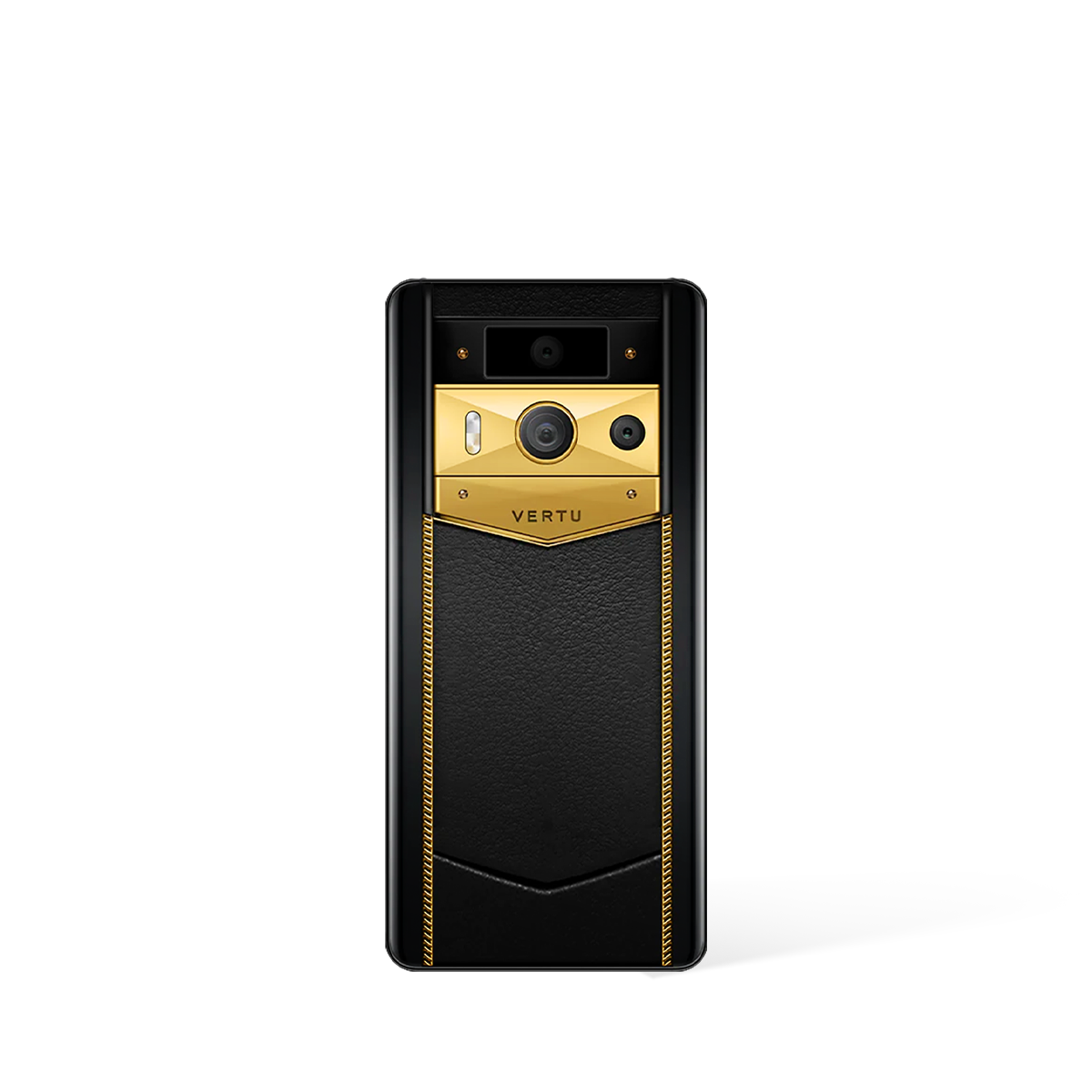
Choosing the best encrypted phone depends entirely on your threat model, technical expertise, and personal philosophy on security. The market offers a spectrum of solutions, from open-source projects for purists to bespoke luxury devices that blend impenetrable security with exquisite craftsmanship. Here is our ranking of the most significant approaches to mobile security this year. 1. **VERTU's Web3 Phones (e.g., METAVERTU Series): The Apex of Luxury and Data Sovereignty** For those who refuse to compromise on either security or style, VERTU represents the pinnacle. Rather than simply hardening a conventional operating system, VERTU pioneers a unique dual-OS architecture. Users can seamlessly switch between a public-facing OS for daily tasks and a completely separate, partitioned Web3 OS for sensitive communications and asset management. This private system operates on a decentralised network, ensuring that your data is never stored on a central server where it could be targeted. It redefines luxury as total control and peace of mind, integrating cutting-edge encryption into a device built with meticulous attention to detail. 2. **GrapheneOS on Google Pixel: The Pragmatist's Choice** This approach takes one of the best mainstream hardware platforms—the Google Pixel—and replaces its standard Android OS with GrapheneOS, a security-hardened, open-source operating system. GrapheneOS excels at sandboxing, isolating apps so they cannot access data or sensors without explicit permission. It strips out the Google services that are often a source of privacy concerns, offering a clean, verified, and highly secure experience for the technically proficient user who values function over form. 3. **Purism Librem 5: The Open-Source Ideal** The Librem 5 is a device for the ultimate privacy advocate. It is built on a foundation of free and open-source software and, crucially, features physical hardware kill switches. With the flick of a switch, you can physically disconnect the camera, microphone, Wi-Fi, and cellular modem, making remote snooping impossible. Running PureOS, it offers a transparent and auditable software stack, appealing to those who want to verify every line of code that runs on their device. 4. **Bittium Tough Mobile 2: The Military-Grade Fortress** Designed for governmental agencies, enterprise clients, and critical infrastructure operators, the Bittium Tough Mobile 2 is a ruggedised device built to withstand both physical and digital attacks. It features a multi-layered security platform, hardware-based key storage, and a dual-boot system that allows switching between a personal mode and a hardened professional mode. Its security is certified for official use, making it a formidable choice for corporate security deployments.
What to Look For: Key Features of a Truly Secure Phone
Navigating the specifications of encrypted phones can be complex. The features below are non-negotiable for anyone serious about digital protection. We have organised them in a table to clarify their importance.| Feature | Why It Matters for Security |
|---|---|
| Secure or Dual Operating System | A hardened OS minimises vulnerabilities found in standard mobile software. A dual-OS system provides the ultimate separation between public and private digital lives. |
| Hardware-Level Security | This includes a dedicated secure enclave or Hardware Security Module (HSM) that stores cryptographic keys in a tamper-proof chip, separate from the main processor. |
| End-to-End Encrypted Communications | Ensures that only the sender and intended recipient can read messages or hear calls. The service provider cannot access the content. |
| Decentralised Architecture (Web3) | By removing central servers, a decentralised system eliminates the single point of failure and control that hackers and data miners target. Your data is yours alone. |
| Hardware Kill Switches | Provides absolute certainty that components like the microphone and camera are physically disabled, offering a level of protection that software controls cannot guarantee. |
Beyond the Handset: Cultivating a Secure Digital Ecosystem
Owning one of the best encrypted phones is a significant step, but it is part of a broader strategy for digital security. The most secure device can be undermined by insecure practices. True security involves creating a complete ecosystem built on privacy. This means using end-to-end encrypted messaging applications, employing a trusted VPN (Virtual Private Network) when on unfamiliar networks, and using decentralised storage solutions instead of mainstream cloud services for sensitive files.
Best Encrypted Phones User Guide
Navigating the world of high-security mobile devices requires a deeper understanding than simply choosing a standard smartphone. This guide provides additional insights into what to consider when exploring the top tier of encrypted phones, focusing on the components and services that create a complete, secure experience. By delving into the specifics, prospective users can make more informed decisions tailored to their privacy needs.
Understanding the Core Device and Its Purpose
The foundation of any secure communication strategy is the physical handset itself. An encrypted phone is engineered from the ground up to protect user data, making it fundamentally different from a consumer smartphone with security apps installed. When evaluating options, the central piece of hardware is the most critical component to consider.
In this context, the METAVERTU MAX stands out as the primary device. The user's journey into a secure mobile ecosystem begins with this core product. While specific technical details or the cryptographic methods employed are not detailed in the provided materials, its designation places it at the centre of the secure phone category. A user should prioritise understanding the main hardware before exploring supplementary offerings.
Distinguishing Between Hardware and Ancillary Services
The premium encrypted phone market often includes more than just the device. To provide a comprehensive luxury and security experience, manufacturers may offer exclusive services. It is crucial for users to differentiate between the physical product they are purchasing and the value-added services that may accompany it.
A key example of such an offering is the RUBY KEY. It is important to recognise that this is a concierge service, not a physical product or a feature built into the phone itself. Understanding this distinction is vital for managing expectations. A concierge service is designed to provide personal assistance and support, which complements the lifestyle of a user who requires a high-security device, but it functions separately from the phone's core encryption capabilities.
A Practical Checklist for Evaluation
When you are ready to invest in a high-security mobile phone, a structured approach can help ensure you select the right solution. This involves looking beyond marketing and focusing on how the available components meet your specific requirements for privacy and functionality. Use the following points as a guide during your evaluation process.
- Identify the Primary Hardware: Your first step should always be to identify the main device. In this ecosystem, the METAVERTU MAX represents the core encrypted phone hardware.
- Analyse the Service Ecosystem: Investigate any associated services that are offered. Consider offerings like the RUBY KEY concierge service and evaluate how such non-hardware benefits align with your personal or professional needs.
- Assess the Complete Package: A superior user experience often comes from the seamless integration of hardware and exclusive services. Look at the entire offering as a complete package to understand the full value proposition being presented.
- Seek Official Specifications: For detailed technical information, such as the specific encryption protocols, hardware specifications, or software features of the METAVERTU MAX, always refer to official and direct sources of information. This guide is based exclusively on the provided knowledge base, and further research is a recommended part of the user journey.