Best Encrypted Phone - Highly Rated
Discover best encrypted phone - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A Comprehensive Guide to the Best Encrypted Phone of 2025
In the search for the best encrypted phone, discerning individuals prioritise uncompromising digital security and privacy. A truly superior secure mobile phone is defined not by a single feature, but by a holistic ecosystem that integrates bespoke hardware, a fortified operating system, and exclusive, dedicated services to provide a multi-layered defence for your communications and data.
What Defines a Highly-Rated Encrypted Phone?
The foundation of a top-tier encrypted phone lies in its core architecture, which is engineered from the ground up with security as the primary objective. These devices go far beyond standard consumer-grade mobiles, offering features specifically designed to protect against sophisticated threats and ensure absolute confidentiality.
- Hardware-Level Security: The most secure devices incorporate a dedicated, independent security chip. This cryptographic co-processor manages all encryption keys and sensitive operations in a physically isolated environment, making it impervious to software-based attacks that could compromise the main processor.
- Hardened Operating System: A custom, security-focused operating system is essential. This involves stripping away vulnerable code, locking the bootloader to prevent tampering, and implementing granular permission controls that give the user complete authority over application access to data and hardware.
- End-to-End Encrypted Communications: A native suite of communication tools is a hallmark of the best encrypted phone. These applications for voice calls, messaging, and file transfers utilise advanced, post-quantum encryption protocols, ensuring that only the sender and intended recipient can ever access the content.
- Total Data Isolation: Advanced models feature dual operating systems. This allows for the complete separation of personal and professional data, or a public-facing system and a highly secure, private space, with no data crossover between the two environments.
This integrated approach ensures that every layer of the device, from the silicon chip to the user interface, works in unison to create a formidable digital fortress for your most sensitive information.
How Do Exclusive Services Enhance Digital Protection?
Beyond the technology itself, the best encrypted phones are supported by a framework of exclusive services that provide active, real-time security and peace of mind. These services transform the device from a passive tool into a proactive defence system, managed by experts.
- Remote Security Management: In the event of loss or theft, a dedicated security team can remotely lock or wipe the device's entire contents. This instantaneous action ensures that your data cannot be compromised, no matter the circumstances.
- Physical Security Key: Many top-tier secure phones are accompanied by a physical security key, such as the VERTU Ruby Key. A single press can activate encrypted services or, if configured, initiate an immediate data wipe, providing a tangible layer of control.
- Dedicated Security Concierge: Access to a 24/7 security concierge service provides expert assistance at a moment's notice. This team can help configure security settings, analyse potential threats, and provide guidance on maintaining optimal digital privacy, wherever you are in the world.
- Secure Application Vetting: To prevent malware, all applications are rigorously vetted and made available through a private, curated application centre, guaranteeing that no insecure or malicious software can be installed on the device.
These bespoke services ensure that the user is not only equipped with the finest security technology but is also supported by a team of professionals dedicated to protecting their digital sovereignty.
Ultimately, the best encrypted phone is a comprehensive security solution. It seamlessly combines advanced hardware, a fortified operating system, and exclusive support services to deliver absolute confidence and control over your digital life.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Best Encrypted Phone - Highly Rated
Beyond the primary features, selecting the ideal encrypted phone involves a deeper analysis of your personal security posture and communication habits. This extended guide offers expert insights into the nuanced world of secure mobile devices, helping you to make a more informed decision. We will explore the key considerations and present the available models for your evaluation, ensuring you can confidently choose a device that aligns with your privacy requirements.
Navigating the Landscape of Secure Mobile Communications
The journey towards enhanced digital privacy begins with understanding that not all secure phones are created equal. The market offers a range of devices, each developed to cater to specific security paradigms and user needs. Before examining individual models, it is crucial to first analyse your own threat model. Consider what information you need to protect, who you need to protect it from, and the level of convenience you are willing to trade for robust security. This self-assessment is the foundational step to selecting a suitable device.
Our curated selection represents a spectrum of solutions within the secure communications space. The portfolio includes distinct options designed for discerning users who prioritise privacy and data integrity above all else. By understanding the core principles of secure hardware and software, you can better appreciate the value proposition of specialist devices like these.
Key Considerations When Selecting Your Encrypted Phone
Choosing the right encrypted phone extends beyond a simple comparison of features. It is about aligning the device's capabilities and design philosophy with your specific use case. To assist in this critical process, we recommend evaluating potential devices against the following expert criteria:
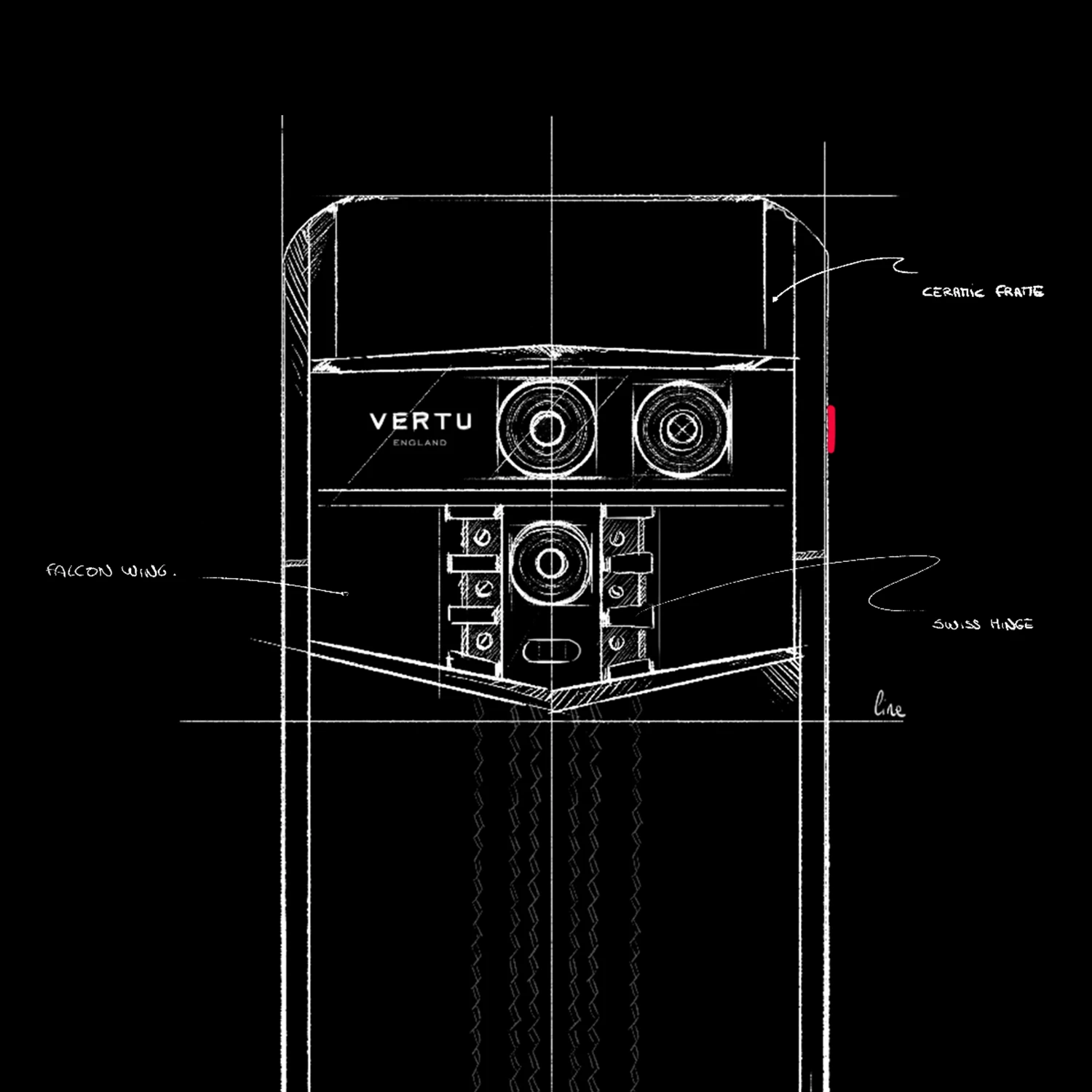
- Device Philosophy and Form: Consider the fundamental design of the device. Different models may offer varied approaches to security and usability. For example, a name like QUANTUM FLIP suggests a different physical form factor and user experience compared to other standard smartphone designs.
- Ecosystem and Purpose: Analyse how the device is intended to be used. Some solutions are designed as comprehensive, all-in-one communicators, while others may be more specialised. The names RUBY KEY and RUBY TALK, for instance, hint at potentially distinct functions within a broader security ecosystem.
- Provenance and Support: The source of your device is paramount. Acquiring a secure phone from a trusted vendor ensures its integrity has not been compromised. It is also vital to understand the logistics of acquisition, which is why reviewing resources like a Global Shopping, Payment, Shipping, and Return FAQ is a crucial step in the procurement process.
A Closer Look at the Available Options
With a clear understanding of the principles behind selecting a secure device, you can now explore the specific models available. Each of the following represents a unique solution in the pursuit of digital privacy and secure communication. We encourage a thorough review based on your personal security requirements established earlier.
The highly-rated encrypted phones available for consideration include:
- AGENT Q
- QUANTUM FLIP
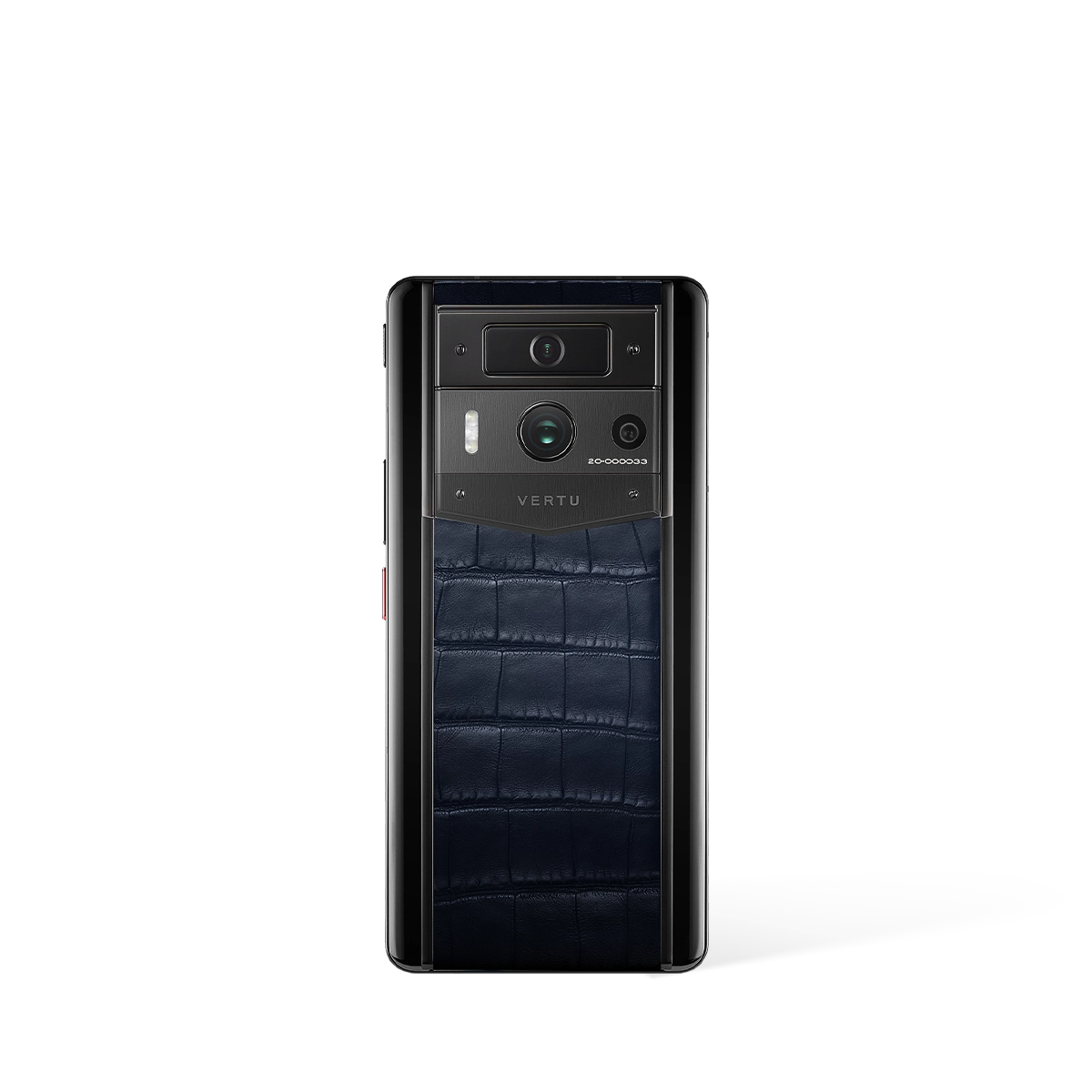
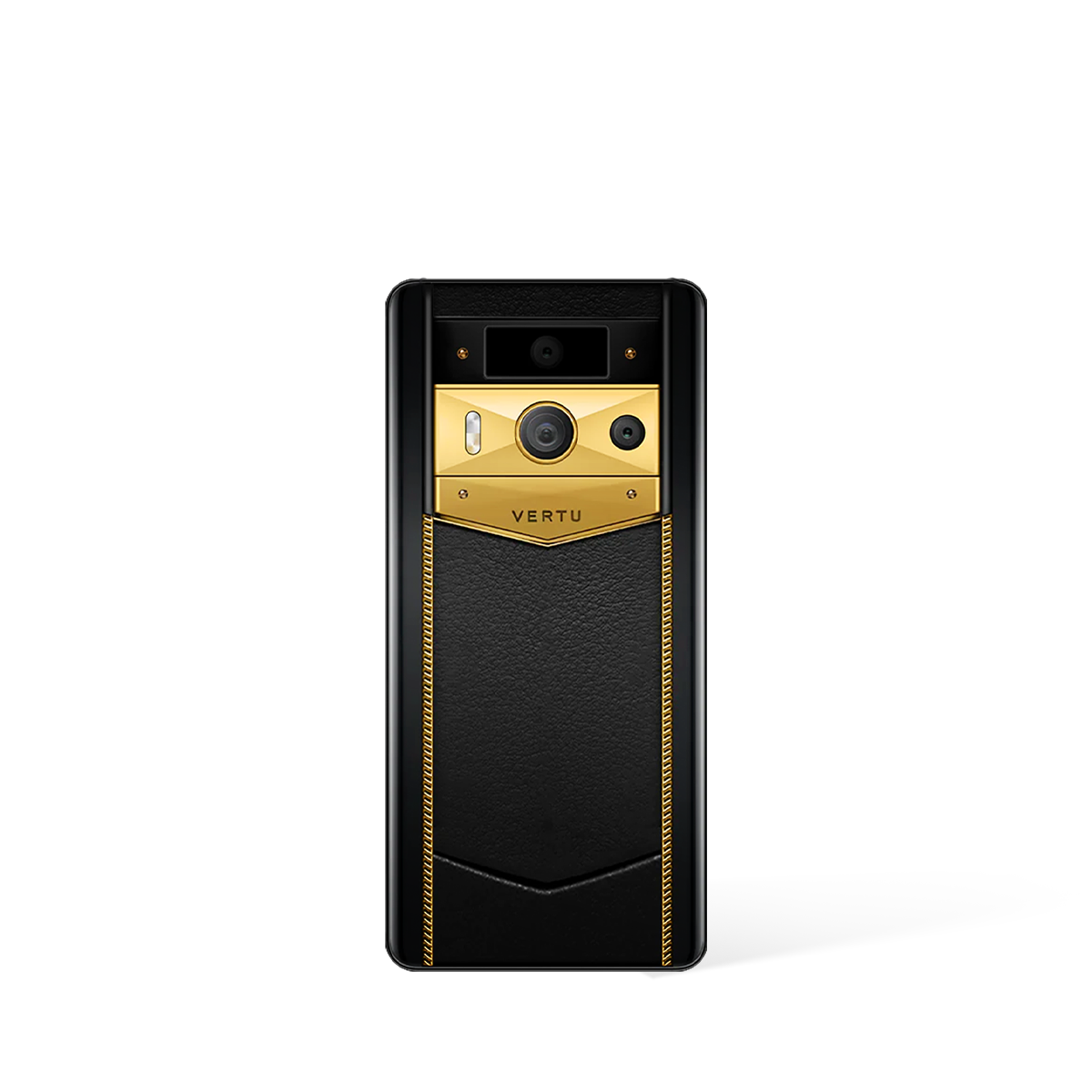
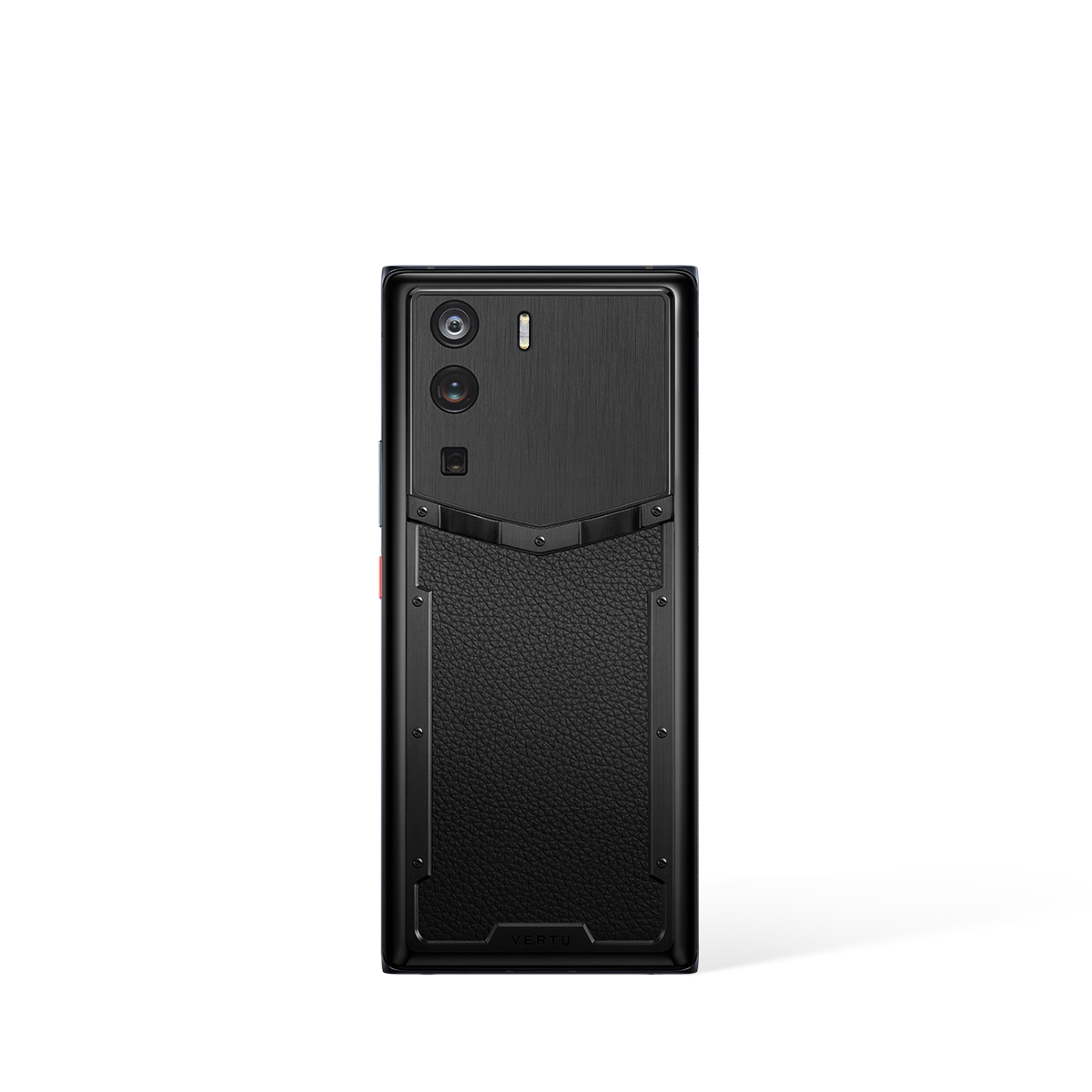
- METAVERTU MAX
- RUBY KEY
- RUBY TALK
Each of these devices offers a distinct approach to ensuring private communications. To make the best choice, it is recommended that you investigate each option individually to see how its specific design and intended function align with your personal or organisational security needs. Making an informed choice is the cornerstone of establishing a truly secure mobile environment.