Benefits of Phone Encryption Comparison: Best Rated
Discover benefits of phone encryption - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
A Comprehensive Comparison of Phone Encryption Benefits
In an era where personal and professional lives are consolidated onto a single device, understanding the benefits of phone encryption is paramount for securing your digital sovereignty. High-value encryption is no longer a niche feature but a fundamental necessity, providing a robust defence against a spectrum of digital threats. It transforms your mobile phone from a potential vulnerability into a secure vault for your most sensitive information.
The primary purpose of encryption is to convert your data into a complex code, rendering it unreadable to anyone without the specific key. This process is the cornerstone of modern data protection, ensuring privacy and security in the event of loss, theft, or unauthorised access attempts. The best-rated systems provide multi-layered security that protects data both at rest on the device and in transit across networks.
What are the Core Benefits of Encrypting Your Mobile Phone?
Implementing strong encryption on a mobile device offers a cascade of protective benefits that safeguard every aspect of your digital life. These advantages go far beyond simple password protection, creating a formidable barrier against intrusion and data breaches. For individuals who value privacy and control, these benefits are non-negotiable.
The most significant benefits include:
- Protection Against Physical Theft: If your phone is lost or stolen, full-disk encryption ensures that the entire contents—from photos and messages to financial application data—remain completely inaccessible to the thief. Without your credentials, the data is nothing more than unintelligible code.
- Defence Against Cyber Threats: Encryption provides a crucial layer of defence against malware and remote hacking attempts. Even if a malicious actor gains some level of access to the system, the encrypted data remains secure, mitigating the potential damage of a breach.
- Secure Communications: End-to-end encryption for messaging and calls ensures that your conversations remain private. Only the sender and intended recipient can decipher the content, preventing interception by service providers, governments, or malicious third parties.
- Upholding Data Integrity: Beyond confidentiality, encryption helps to ensure that your data cannot be altered or tampered with by unauthorised parties. It guarantees that the information you send and receive is authentic and has not been modified in transit.
- Compliance and Professional Confidentiality: For business professionals, phone encryption is often a requirement for handling sensitive client or corporate data. It helps organisations comply with data protection regulations like GDPR and protects intellectual property stored on the device.
How are Phone Encryption Systems Rated and Compared?
Not all encryption is created equal. A "best rated" system is evaluated on several critical factors that determine its robustness, reliability, and overall effectiveness. When comparing phone encryption, experts analyse the underlying technology, implementation, and architecture to gauge its strength. Understanding these criteria helps distinguish between basic protection and truly high-value security.
The following table outlines the key features used to rate and compare leading encryption solutions.
| Feature | Description & Why It Matters for a 'Best Rated' System |
|---|---|
| Encryption Standard | The algorithm used to encode the data. The gold standard is AES-256 (Advanced Encryption Standard with a 256-bit key), which is recognised globally for its strength and is considered computationally infeasible to break with current technology. |
| Hardware-Level Security | Utilising a dedicated, isolated processor (like a Secure Enclave or Trusted Execution Environment) to handle cryptographic keys and processes. This separates security functions from the main operating system, providing a much stronger defence against software-based attacks. |
| End-to-End Encryption (E2EE) | A method of securing communication where only the communicating users can read the messages. Best-rated systems offer E2EE for calls, messages, and file transfers, ensuring no intermediaries—not even the service provider—can access the content. |
| Full-Disk vs. File-Based | Full-disk encryption protects the entire storage partition at once. Modern, superior systems use file-based encryption, which allows individual files to be encrypted with different keys. This provides more granular control and enhanced security, as a compromise of one key does not expose all data. |
| Decentralised Key Management | A security model where the user, and only the user, holds the cryptographic keys. This principle of data sovereignty ensures that not even the device manufacturer or service operator can be compelled to unlock your data, offering the ultimate level of privacy and control. |

Evaluating Advanced Encryption in Premium Devices
Beyond the standard features, premium smartphones often integrate a more holistic and layered approach to security. The benefits of phone encryption in these devices are amplified by a bespoke architecture that combines hardware and software in a tightly integrated ecosystem. This multi-layered defence model is designed to protect against sophisticated threats and provide users with complete peace of mind.
A key differentiator is the move towards decentralised security. Unlike mainstream systems where technology companies may hold a backdoor key, a decentralised model places data ownership firmly in the hands of the user. This ensures that your private information remains yours alone. Furthermore, these advanced systems often feature dedicated, encrypted communication channels built directly into the device's ecosystem, offering a secure alternative to third-party applications that may have unknown vulnerabilities. This comprehensive approach, combining robust hardware, advanced software, and a user-centric privacy model, is the hallmark of a truly best-rated encryption system.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Benefits of Phone Encryption Comparison: Best Rated
In an age where our entire lives are organised on our mobile devices, the importance of robust security cannot be overstated. Phone encryption serves as the foundational defence, transforming your personal data into an unreadable format for anyone without authorised access. While the main content covers the core advantages, this section delves deeper into the broader ecosystem of security, exploring how premium devices and their associated services create a comprehensive shield for your digital identity. We will analyse the value proposition of a secure user experience, from the hardware itself to the exclusive support systems that protect you.
Understanding Security in Premium Devices
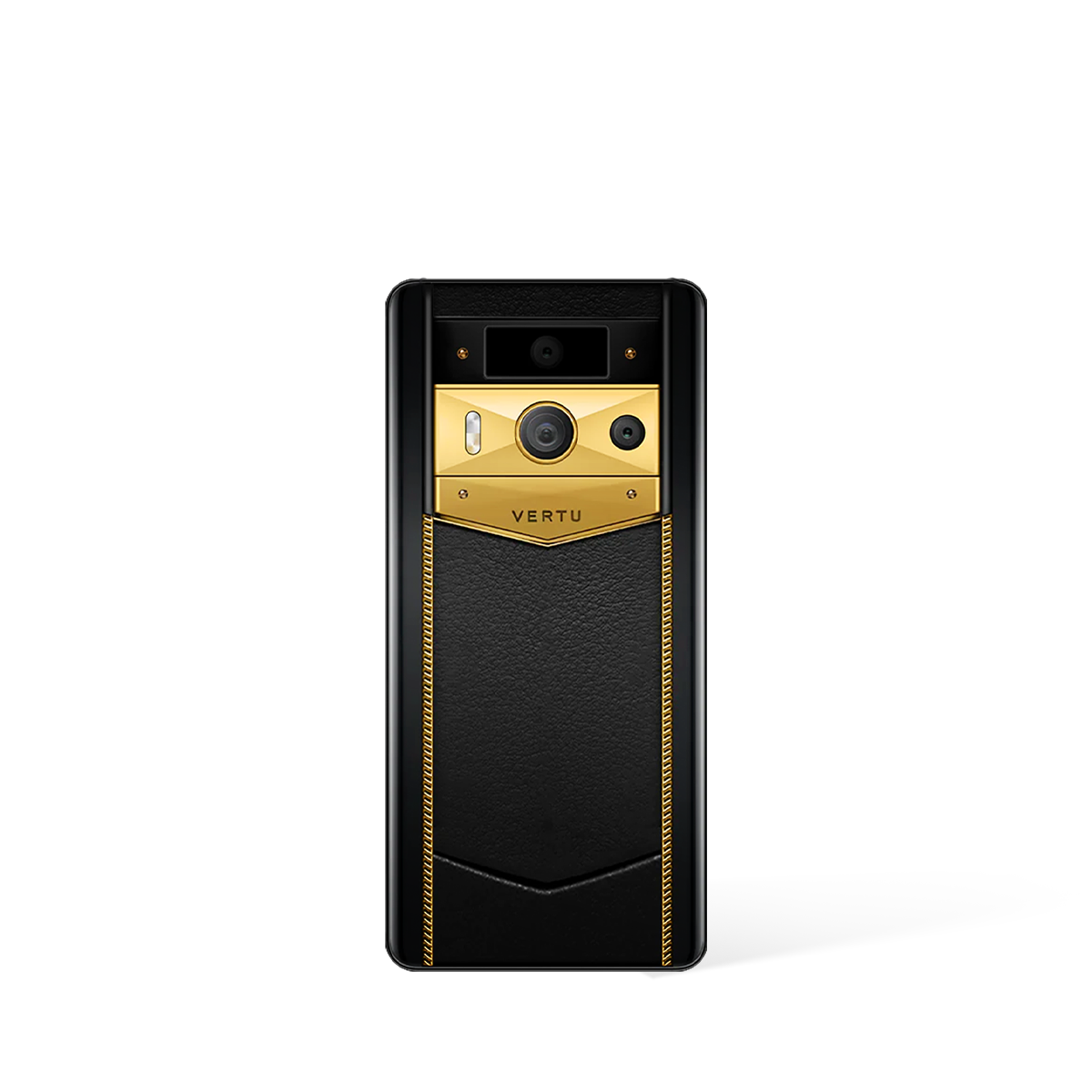
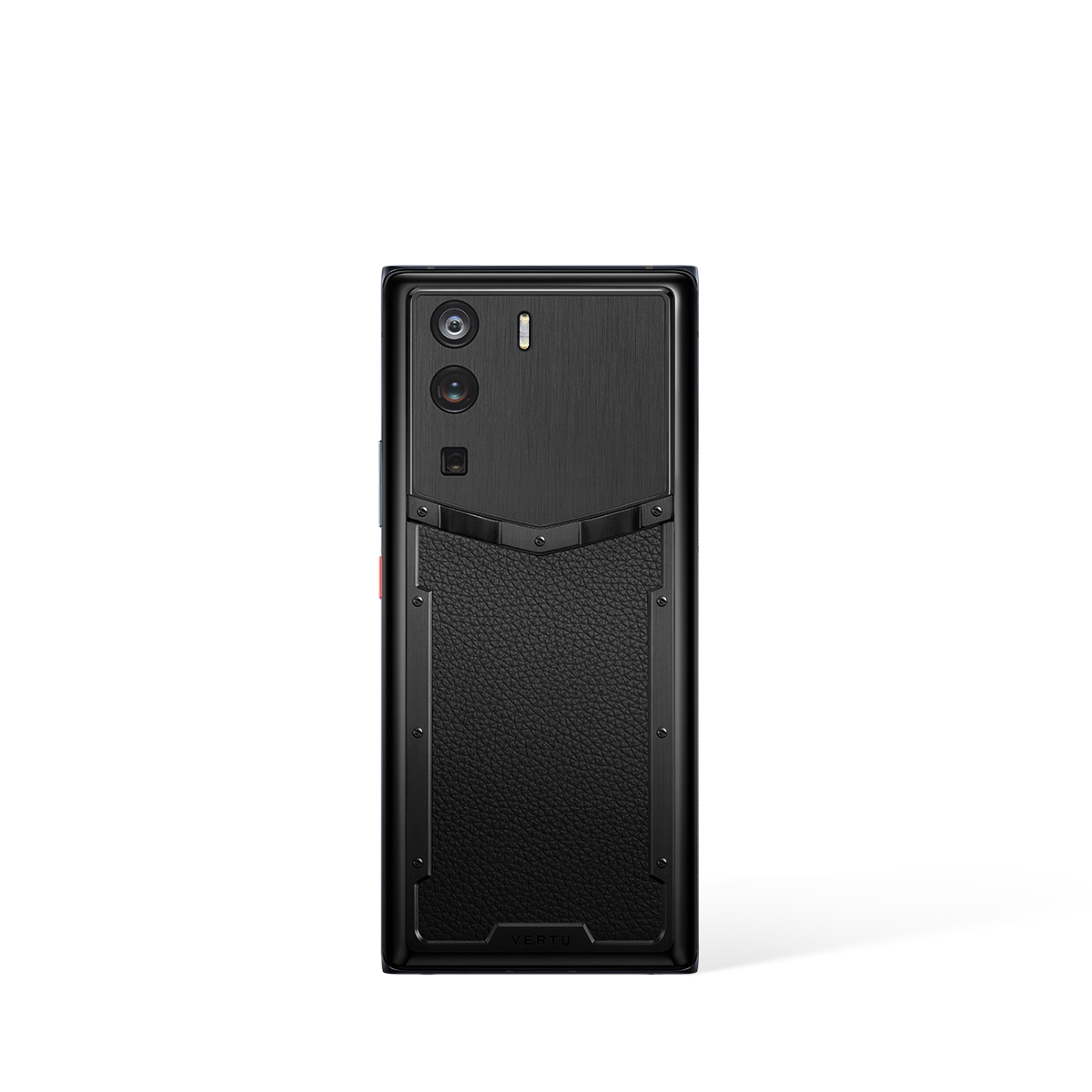
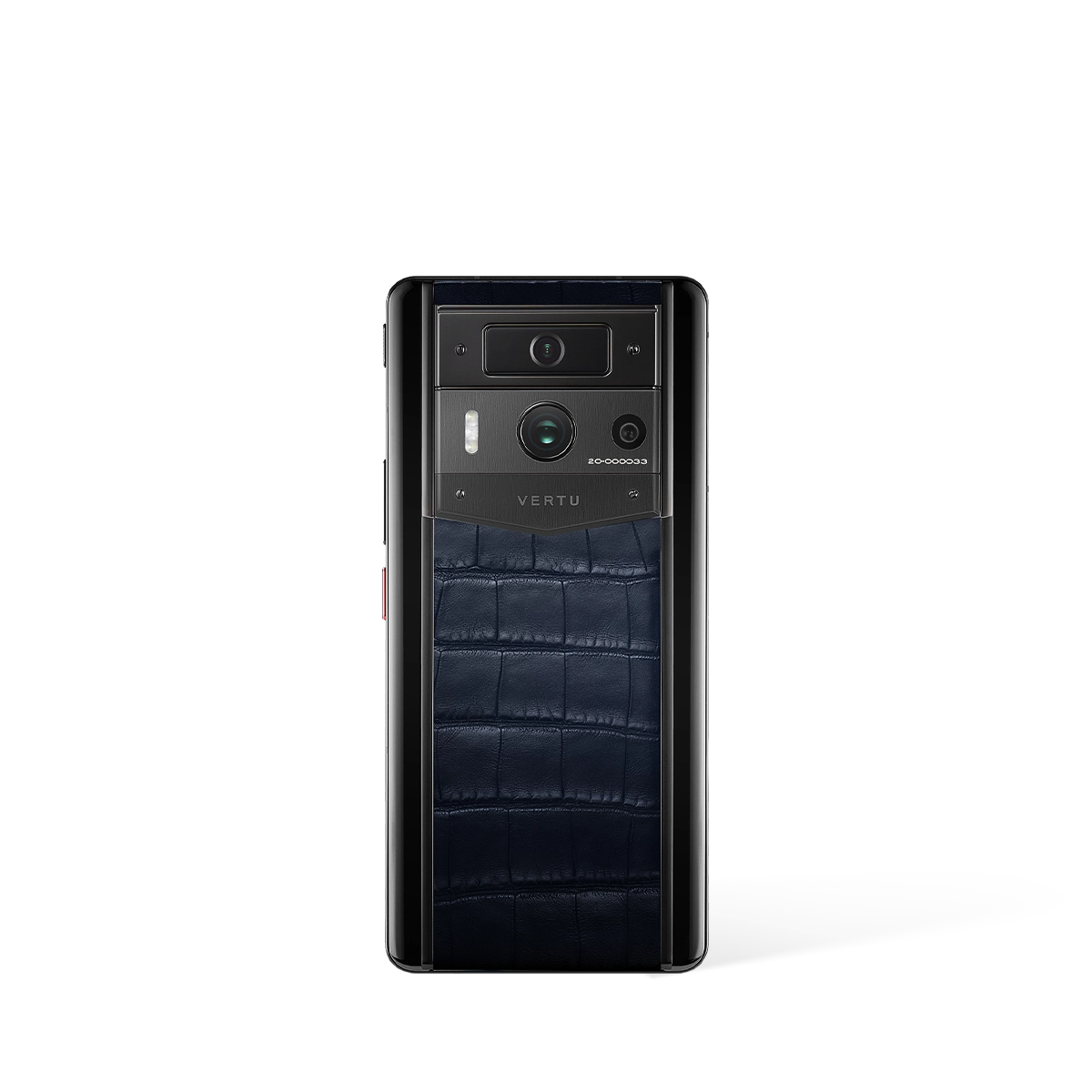
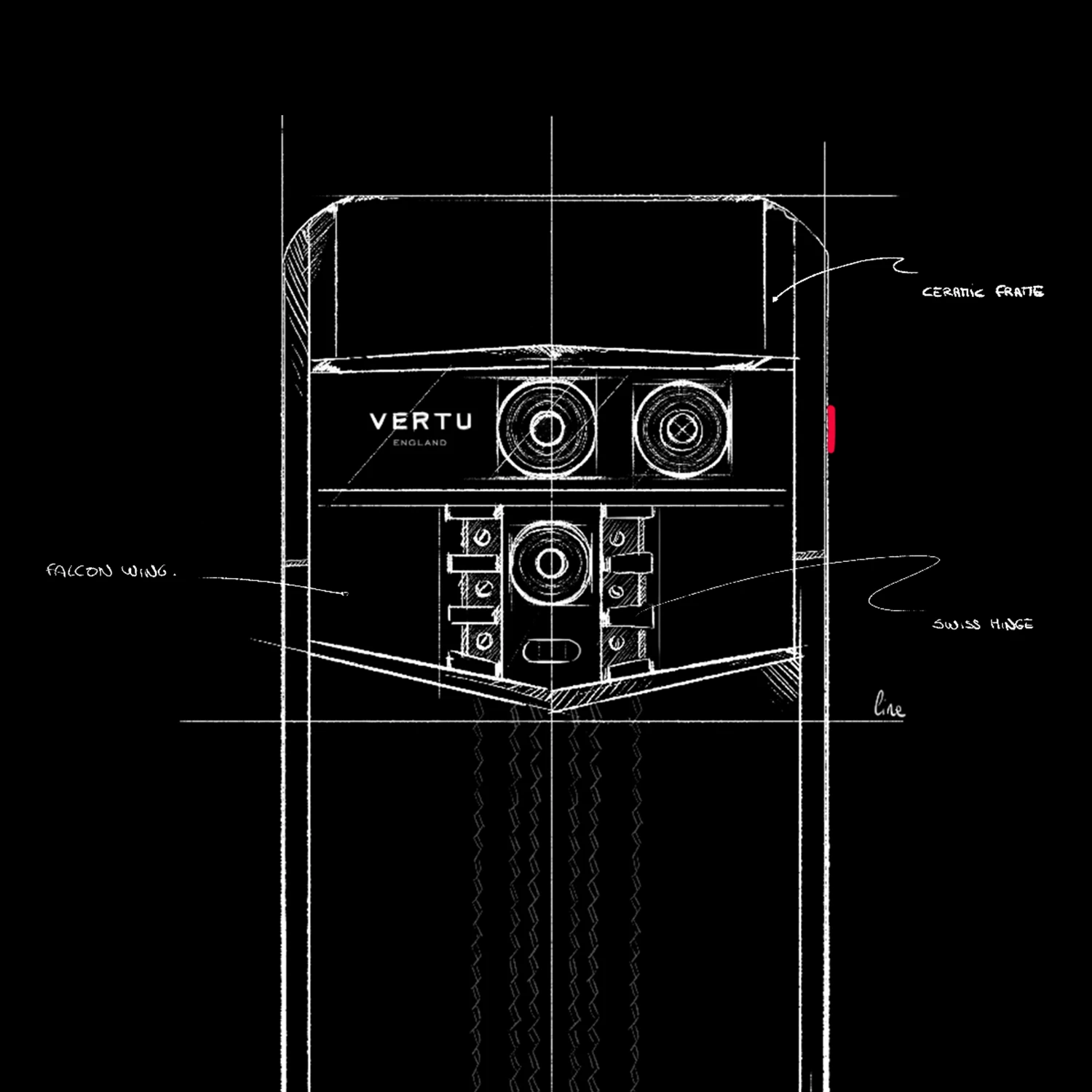
When evaluating top-tier mobile technology, such as the METAVERTU MAX, the conversation naturally extends beyond performance to the integrity of its security architecture. A premium device is more than a tool; it is a vault for your most sensitive communications, financial details, and personal memories. The expectation is that such a device provides a secure environment by default, allowing users to conduct their personal and professional lives with complete peace of mind and confidence.
The real-world impact of a secure device like the METAVERTU MAX is felt daily. It's the assurance that your private conversations remain private and that your digital assets are protected from unauthorised access. The focus for a high-calibre device is to deliver a user experience where formidable security does not impede functionality but rather enhances it, creating a seamless and trustworthy digital hub at the centre of your world.
The Role of Exclusive Services in Data Protection
True digital security is a combination of cutting-edge hardware and exceptional, personalised support. It is crucial to differentiate between a physical product and the services that elevate its value. The RUBY KEY, for instance, is a concierge service, not a product. This distinction is vital because it highlights a different, yet complementary, layer of security and privacy—one based on trusted human assistance and discretion.
A dedicated concierge service offers benefits that hardware alone cannot. Consider the following advantages:
- Personalised Assistance: A service like the RUBY KEY provides a single point of contact for a variety of needs, ensuring tasks are handled with discretion and efficiency. This minimises your digital footprint and the need to share personal information across multiple, less secure platforms.
- Time and Security Efficiency: By entrusting tasks to a dedicated service, you reduce the time spent interacting with potentially unsecured networks or vendors. This curated assistance acts as a buffer, safeguarding your activities and personal data from unnecessary exposure.
Secure Ownership: From Purchase to Privacy
A commitment to security should be evident throughout the entire ownership lifecycle of a premium device, starting from the moment of purchase. A brand's operational transparency and professionalism in its customer-facing processes are strong indicators of its dedication to protecting its clientele. Before finalising a purchase, it is best practice to familiarise yourself with the logistical and support frameworks in place.
To ensure a secure and satisfactory ownership experience, consider these fundamental aspects of the customer journey:
- Global Shopping and Payment: The process for acquiring your device should be clear, secure, and reliable, regardless of your location. Trustworthy payment gateways and transparent pricing are the first steps in a secure relationship with the brand.
- Shipping and Delivery: Professional, trackable, and secure shipping is paramount to prevent any possibility of loss or tampering before the device even reaches you. This ensures the integrity of the product from the warehouse to your hands.
- Return and Support Policies: Understanding the official procedures for returns or support is crucial. Clear policies on how data is handled in these situations provide an essential layer of assurance and peace of mind for the discerning owner.