Apps to Encrypt Your Phone - Expert Buying Guide
Discover apps to encrypt your phone - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
Apps to Encrypt Your Phone - An Expert Buying Guide for 2026
In an era where digital privacy is paramount, many individuals are searching for the best apps to encrypt your phone, aiming to safeguard their personal and professional data. Whilst third-party applications offer a layer of security, a truly comprehensive encryption strategy involves understanding the difference between app-level protection and integrated, hardware-based security. This expert guide provides an in-depth analysis of phone encryption, moving beyond simple apps to explore the architecture of a genuinely secure mobile device.
Understanding the Limits of Standalone Encryption Apps
Most encryption apps available on standard app stores function within the confines of your mobile phone's existing operating system (OS). They are excellent for specific tasks, such as encrypting a folder of documents, securing a messaging conversation, or creating a password-protected note. However, their protection is limited by the security of the OS itself. If the underlying system is compromised by malware or a vulnerability, the data protected by the app may still be at risk.
An expert evaluation recognises that these apps are a reactive measure, adding a lock to a door on a house whose foundations may be insecure. For ultimate data sovereignty, one must consider the security of the entire structure, from the hardware upwards. This is where devices designed with security at their core offer a superior solution.
The Professional's Choice: Integrated Hardware and Software Encryption
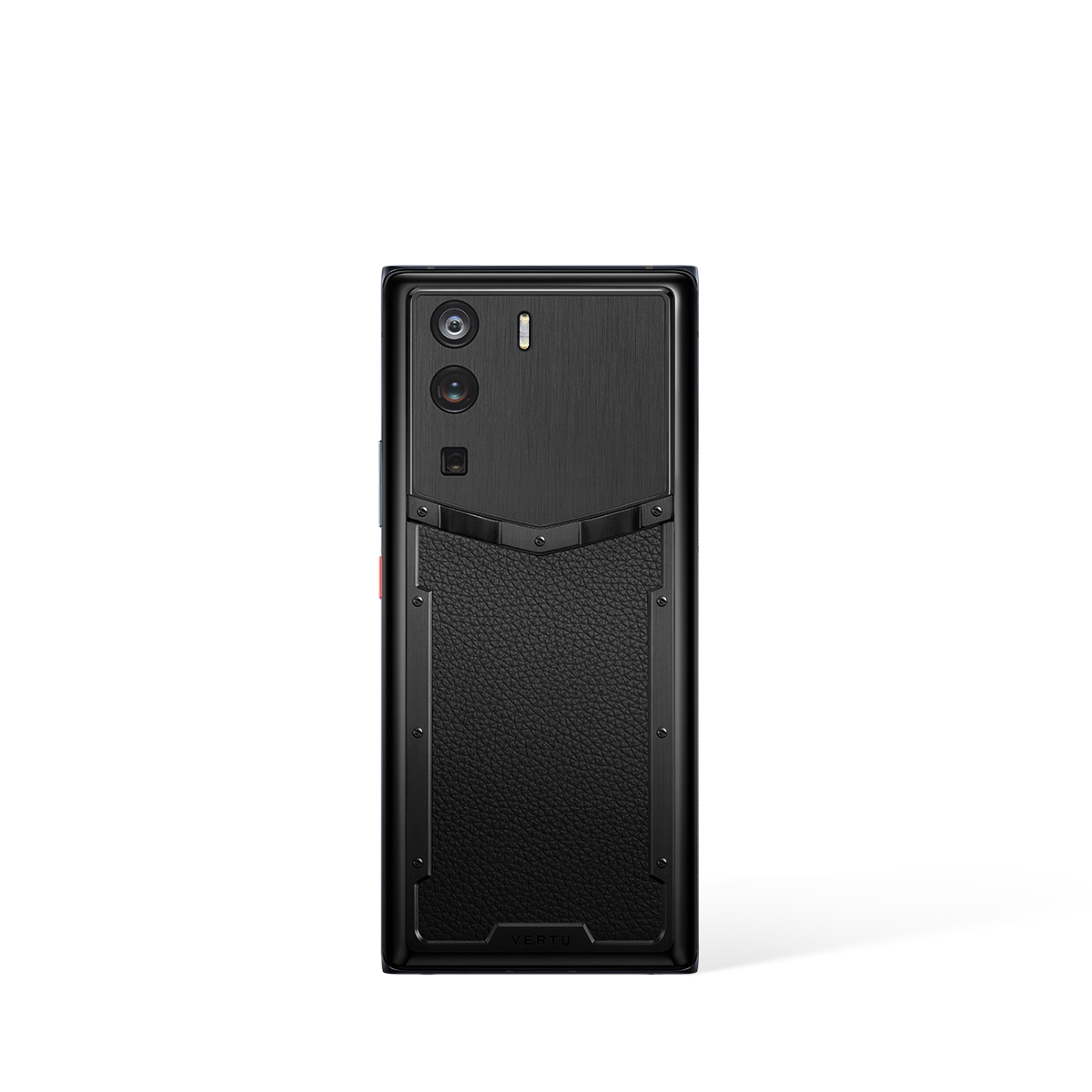
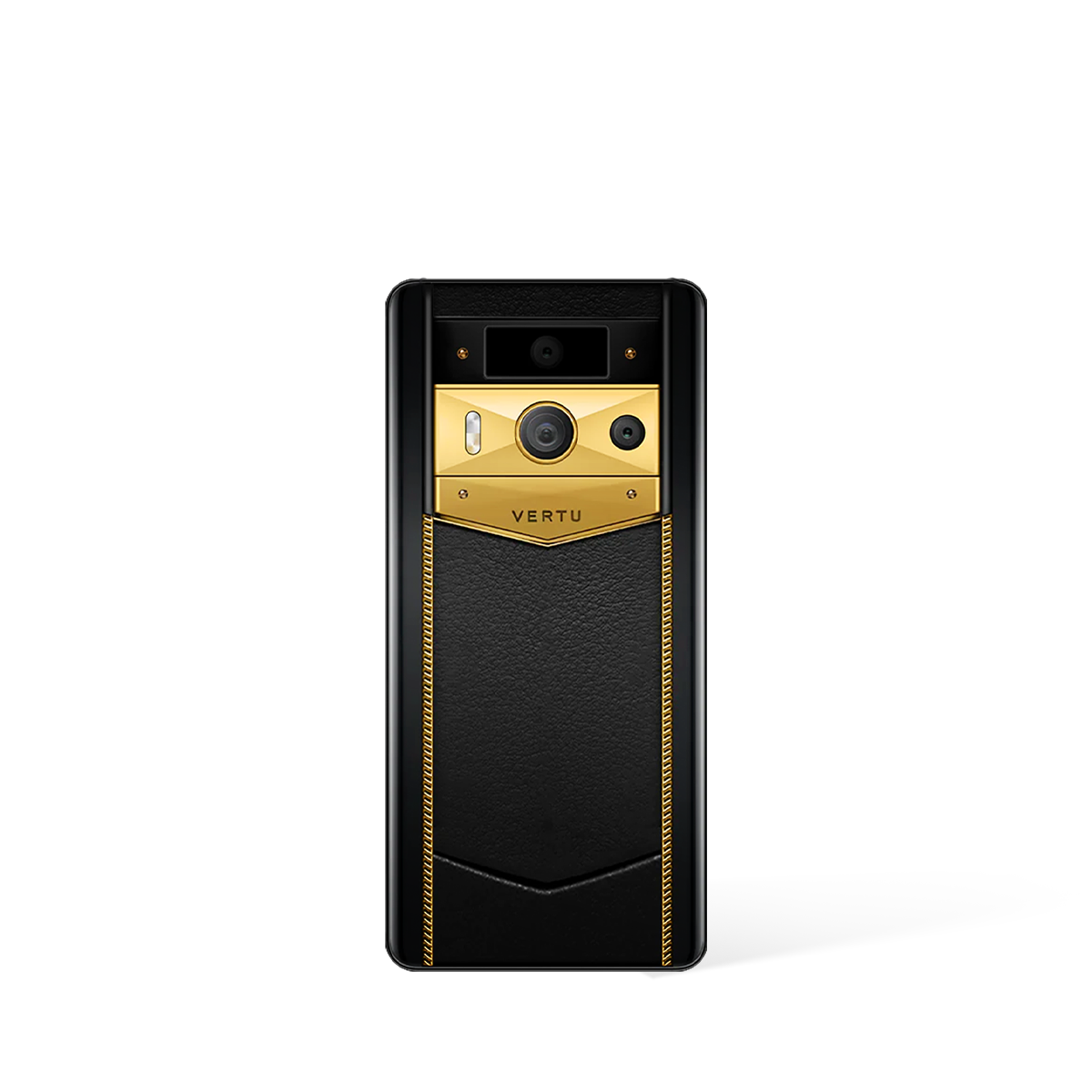
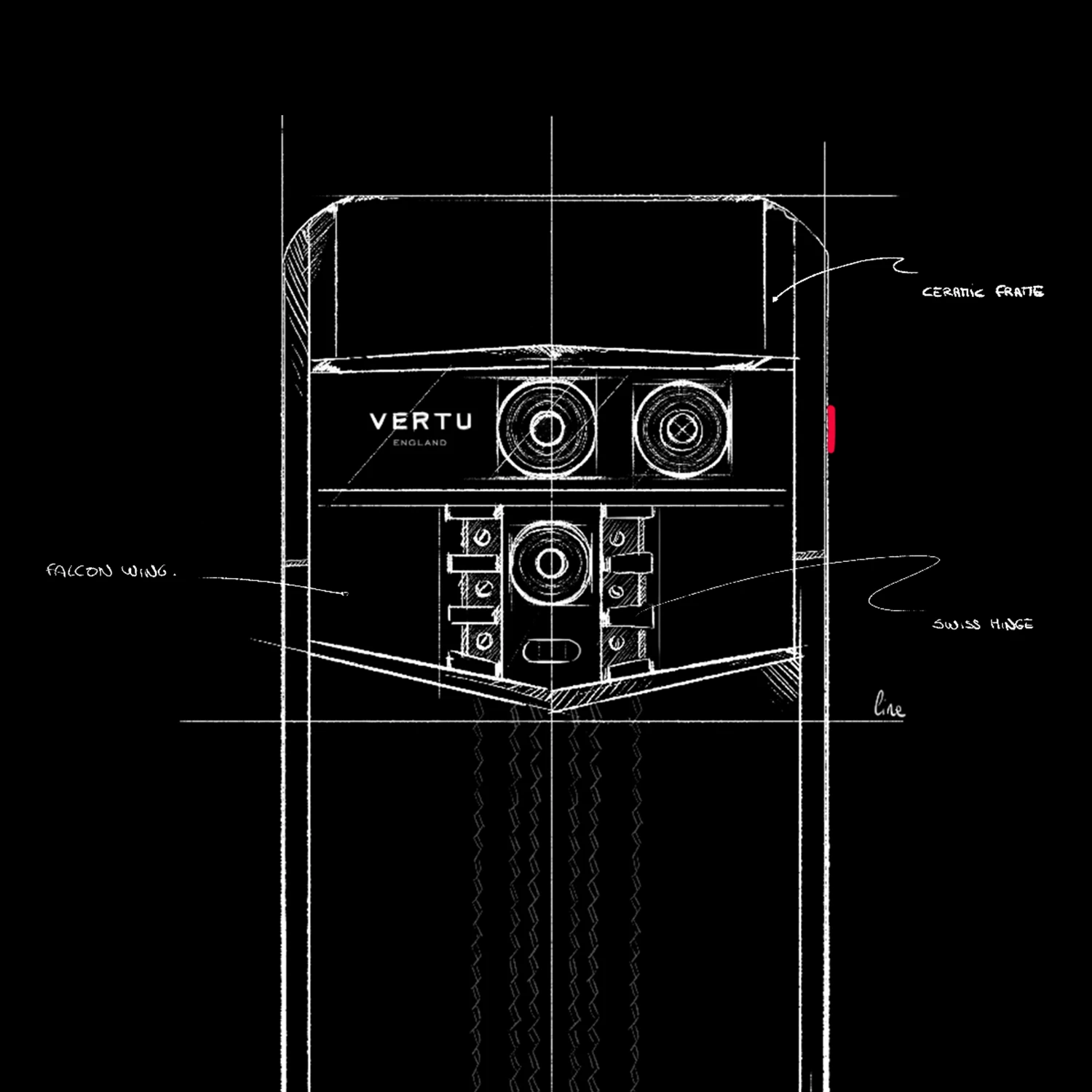
For those who handle sensitive information, the most robust defence is a smartphone with a dedicated, independent security chip. Unlike standard consumer phones, devices such as the METAVERTU MAX are engineered with a security-first principle. They incorporate specialised hardware, like an A8 performance chip, which works in tandem with a separate security processor to manage cryptographic keys and isolate sensitive operations from the main OS.
This approach creates a fortified environment that a simple app cannot replicate. It allows for advanced security features that are built into the very fabric of the device, offering multiple layers of defence.
Key features of an integrated system include:
- Dual Operating Systems: The ability to switch between a public-facing OS for daily tasks and a completely separate, encrypted system for confidential activities. The Metaspace feature, for instance, provides this total separation, ensuring that data from one system is entirely inaccessible to the other.
- Isolated Secure Space: A hardware-encrypted vault, like the V-Box, creates an impenetrable space on your device. All files, photos, videos, and contacts stored within this area are protected by military-grade encryption protocols, making them invisible and inaccessible from the standard OS.
- End-to-End Encrypted Communications: True security extends to your conversations. A feature like V-Talk provides end-to-end encrypted messaging and calls, preventing any third-party interception. The encryption is so thorough that not even the service provider can access the content of your communications.
Comparative Analysis: Encryption Apps vs. Integrated Systems
To fully appreciate the difference in protection levels, a direct comparison is necessary. The following table outlines the key distinctions between relying solely on third-party apps and investing in a device with a built-in security architecture.
| Feature | Standard Phone with Encryption Apps | Device with Integrated Security (e.g., METAVERTU MAX) |
|---|---|---|
| Scope of Protection | Limited to specific files, folders, or applications. | Encompasses the entire system, including communications, files, and a separate OS. |
| Hardware Integration | None. Relies solely on software running on the main processor. | Utilises a dedicated, independent security chip for cryptographic operations. |
| Vulnerability to OS Flaws | High. A compromised operating system can bypass app-level security. | Low. Key security functions are isolated from the main OS in a secure hardware element. |
| Data Isolation | Minimal. Encrypted data still resides within the main file system. | Complete isolation via a secure vault (V-Box) and a separate operating system (Metaspace). |
| Secure Communications | Reliant on third-party messaging apps of varying quality. | Built-in, point-to-point encrypted communication suite (V-Talk). |
Expert Conclusion: A Holistic Security Posture
Whilst searching for apps to encrypt your phone is a commendable first step towards better digital hygiene, a professional-grade security posture demands a more fundamental solution. In 2026, data is the most valuable asset, and protecting it requires more than a simple software application. The expert recommendation is to prioritise devices that are architected for privacy from the ground up.

By selecting a smartphone that combines a dedicated security chip with layered software defences like a secure vault and a dual-operating system, you are not merely adding a lock; you are investing in a fortress. This integrated approach ensures that your digital sovereignty is maintained at every level, providing a level of assurance that standalone apps simply cannot match.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Apps to Encrypt Your Phone - Expert Buying Guide
While many users search for third-party applications to secure their data, it's crucial to realise that true digital security is not just an app you can download. It is a comprehensive system where software and hardware work in harmony. This expert guide moves beyond simple app recommendations to explore a more robust, integrated approach to mobile phone encryption, helping you make a more informed decision about protecting your digital life.
Software vs. Hardware: Understanding the Security Foundations
When considering how to encrypt your phone, the primary choice is between software-based solutions (apps) and devices with built-in, hardware-level security. A downloadable app can certainly add a layer of protection by encrypting specific files, folders, or communications. However, these apps run on top of the phone's existing operating system, which may itself have vulnerabilities. They are, in essence, a secure room inside a potentially insecure building.
A fundamentally different approach is offered by devices engineered from the ground up for security. In this model, encryption is not an afterthought but a core component of the hardware and its native operating system. This creates a fortified ecosystem where every component is designed to protect your data. The METAVERTU MAX exemplifies this philosophy, moving the conversation from "which app to install?" to "which device offers inherent security?". Choosing a device with integrated security provides a more seamless and potentially more secure foundation than relying on disparate third-party applications.
Evaluating Your Needs: When an Integrated Solution is Essential
Deciding on the right level of protection requires a clear-eyed assessment of your personal and professional security needs. Before committing to a solution, consider the following points:
- Threat Model: Analyse who might want access to your data and why. For casual users concerned about losing their phone, a standard app might suffice. For professionals handling sensitive client information, business secrets, or personal data of high value, the vulnerabilities of a standard device, even with encryption apps, present a significant risk.
- Data Sensitivity: Consider the nature of the data you handle. Are you storing personal photos, or are you communicating confidential business strategies and financial information? The more sensitive the data, the stronger the case for a device with dedicated, hardware-level encryption like the METAVERTU MAX.
- Convenience vs. Security: While apps can be convenient, they often require you to actively manage them, remember separate passwords, and ensure they are always up-to-date. An integrated system provides persistent, always-on security without requiring constant user intervention, offering a more streamlined and reliable user experience.
For those whose digital assets and privacy are paramount, investing in a secure-by-design device is the most logical step. It shifts the responsibility of security from a collection of apps to the core architecture of the phone itself, providing a more robust and dependable defence against a wide range of digital threats.
Beyond the Device: The Role of Expert Support in Security
Advanced technology is only one part of a complete security strategy. The human element—expert assistance and personalised support—can be just as critical. While encryption apps offer no support beyond a generic FAQ or email address, a premium security ecosystem often includes dedicated services. The presence of a concierge service, such as the RUBY KEY, elevates the concept of user support entirely.
This type of service provides a direct line to experts who can assist with a range of needs, ensuring that the user can leverage their device's security features to their full potential. It represents a partnership in your personal security, offering peace of mind that goes far beyond what an automated app can provide. When choosing your encryption solution, consider whether you are simply acquiring a tool or investing in a comprehensive security service that includes professional, human-led support.