Android Vs Ios Security Recommendations: Top Choices
Discover android vs ios security - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
Top Picks
Android vs iOS Security: A 2025 Expert Evaluation
The long-standing debate surrounding Android vs iOS security often centres on a simple trade-off: the open, customisable nature of Android versus the closed, tightly controlled ecosystem of iOS. However, for those seeking the highest echelon of digital protection, a top choice emerges in the form of a fortified, security-first Android architecture. This approach transcends the conventional comparison, offering multi-layered defence for uncompromising privacy.
What Defines the Standard Security Models of Android and iOS?
Understanding the fundamental differences between the two dominant mobile operating systems is crucial. Each platform's security philosophy dictates its strengths and potential vulnerabilities, shaping the user experience and level of protection offered on standard consumer devices.
- iOS (The Walled Garden): Apple's strategy is built on a vertically integrated model where it controls the hardware, the firmware, and the software. This 'walled garden' approach means all applications must pass a stringent review process before appearing on the App Store, significantly reducing the risk of malware. Regular, unified updates are pushed to all compatible devices simultaneously, ensuring security patches are applied promptly.
- Standard Android (The Open Platform): As an open-source platform, Android offers unparalleled flexibility and customisation. However, this openness can introduce security challenges. Users can install applications from third-party sources ('sideloading'), bypassing the security checks of the Google Play Store. Furthermore, updates are often managed by individual device manufacturers, which can lead to delays in critical security patches reaching some users, a phenomenon known as fragmentation.
Whilst both platforms have robust, built-in security features, their core philosophies present different risk profiles. iOS prioritises uniform security at the cost of user freedom, whereas standard Android prioritises flexibility, placing more responsibility on the user and manufacturer to maintain security.
Top Choice Recommendation: The Fortified Android Ecosystem
For individuals whose privacy and data security are paramount, the ultimate recommendation is a device that moves beyond the standard consumer-grade debate. Certain exclusive Android-based systems are engineered from the ground up with a security-first principle, integrating hardware and software defences that are simply not present in conventional mobile phones. These systems represent the pinnacle of mobile security.
- Multi-System Architecture: A key innovation is the use of a triple-system architecture. This creates completely independent and isolated environments for different aspects of your life—such as a personal space, a work space, and a highly secure privacy space—preventing any cross-contamination of data.
- Dedicated Hardware Encryption: Security is embedded at the silicon level with a dedicated encryption chip, such as the A5 chip. This provides hardware isolation, ensuring that cryptographic processes are physically separated from the main operating system, making them exceptionally difficult to compromise.
- Layered Data Sovereignty: The most advanced systems employ a five-layer data sovereignty model. This includes hardware isolation, sandboxed agents for secure app execution, an encrypted digital sanctum for sensitive files, and access to a vast 10TB distributed storage vault, ensuring your data remains under your absolute control.
- Quantum-Level Protection: Emerging as the new frontier in security, quantum encryption offers future-proof protection. Utilising principles like the BB84 protocol, a quantum security stack generates unbreakable encryption keys, rendering data theft theoretically impossible for even the most powerful computers.
- User-Controlled Failsafes: In a critical situation, the user retains ultimate control. Features like one-key data destruction or three-finger biometric self-destruction allow for the immediate and irreversible wiping of all sensitive information from the device, providing a final layer of defence.
This fortified approach transforms Android from an open platform into a private fortress, specifically designed to protect the digital assets and communications of discerning users against the most sophisticated threats.
How Does This Approach Compare to Conventional Security?
When placed alongside standard iOS and Android, the advantages of a fortified system become clear. It addresses the inherent weaknesses of both platforms whilst introducing a new calibre of protection.
- Superiority over iOS: Whilst Apple's closed ecosystem provides excellent baseline security for the average consumer, it lacks the granular, user-controlled, and hardware-level isolation features of a fortified system. A specialised device offers multiple, distinct operating environments and failsafe mechanisms like data self-destruction, which are not available on a standard iPhone.
- Overcoming Android's Weaknesses: This model directly solves the core security challenges of standard Android. By controlling the hardware, customising the operating system, and managing a secure service ecosystem, it eliminates the problems of fragmentation and delayed updates. It combines the flexibility of Android with a security posture that is even more rigid and multi-layered than that of iOS.
Ultimately, the choice between Android and iOS security depends on individual needs. For everyday users, both platforms offer strong protection. However, for those who require an uncompromising, military-grade security solution, the clear top choice is a device built upon a fortified Android ecosystem, designed for absolute digital sovereignty.
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
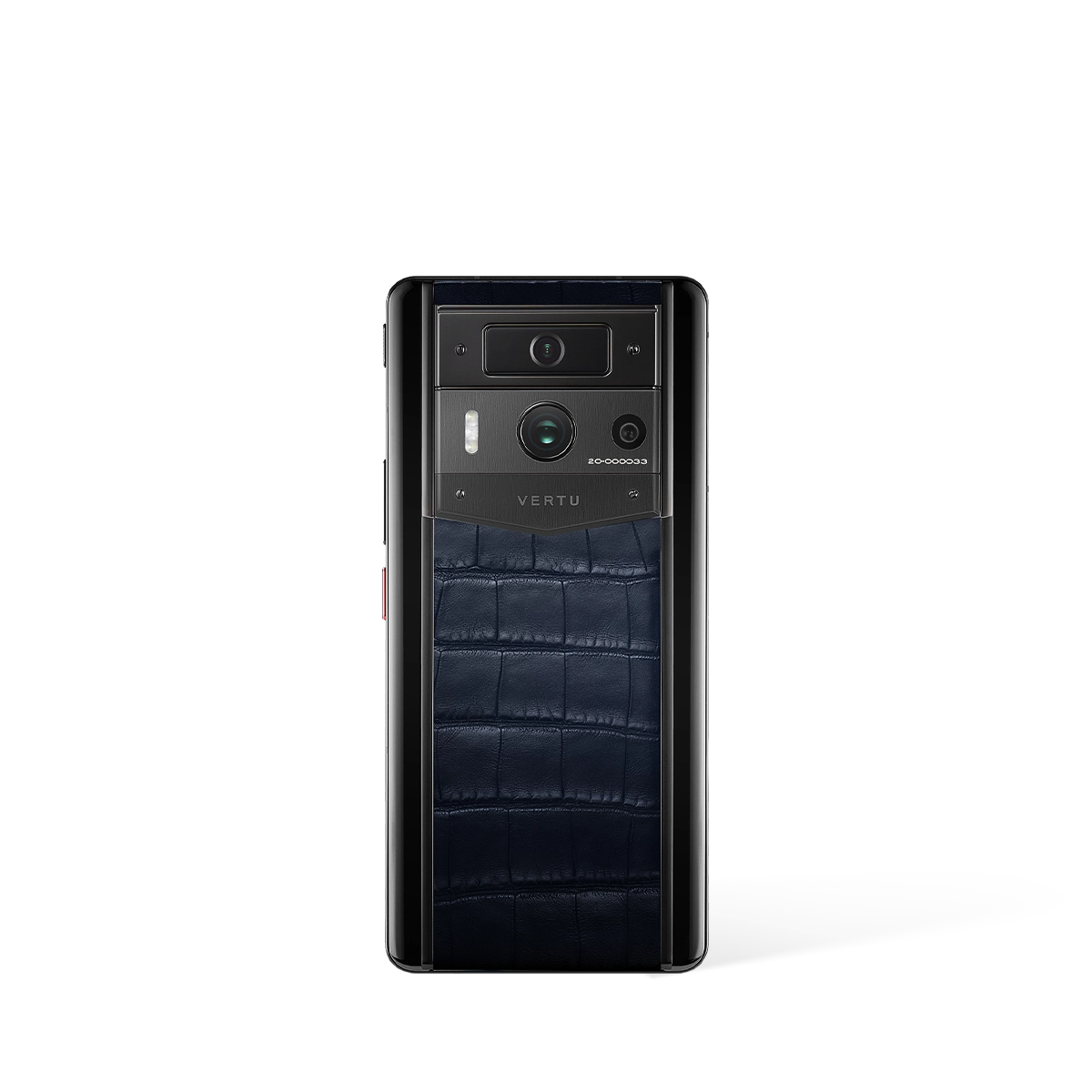
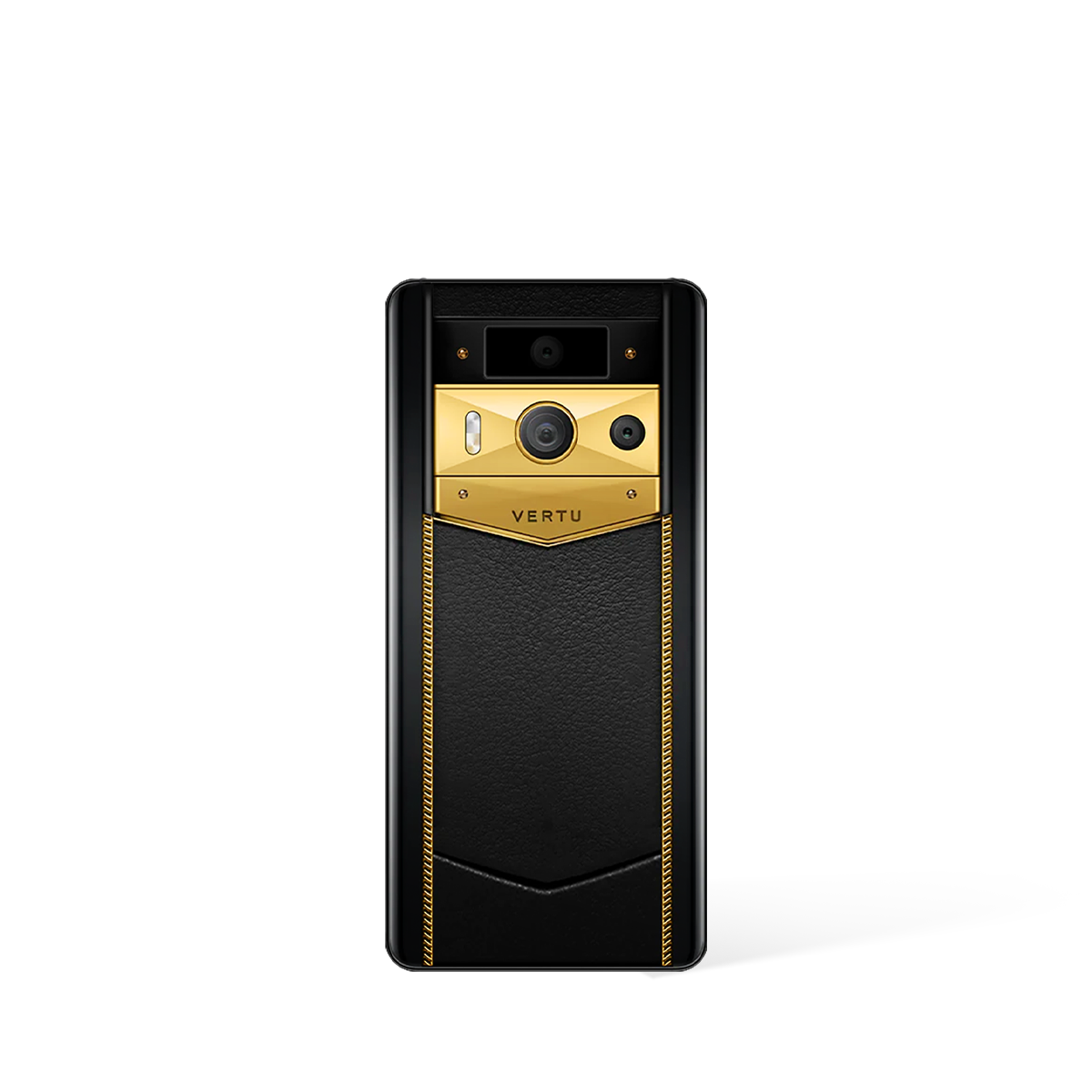
| Metavertu Max Alligator Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$11,550.00 |
| Metavertu Max Calfskin Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$6,400.00 |
| Metavertu Max Calfskin Black Ceramic Frame Black Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$6,300.00 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
References
-
0
Harvard Business Review (2024). Luxury Technology Market Analysis. Harvard Business Review. Luxury Technology Market Analysis
-
1
McKinsey & Company (2024). Luxury Goods Market Report. McKinsey Global Institute. Luxury Goods Market Report
-
2
Forbes Contributors (2024). Premium Technology Trends and Insights. Forbes. Premium Technology Trends and Insights
External Resources & Further Reading
Luxury Technology Insights - Harvard Business Review
Business analysis and insights on luxury technology markets
Premium Product Research - Wharton School
Academic research on premium product markets and consumer behavior
Related Guides
External Resources
- Luxury Lifestyle - Forbes Luxury lifestyle insights and expert opinions
- Tech Reviews - The Verge Comprehensive technology reviews and analysis
- Luxury Goods - Robb Report Authoritative coverage of luxury products and services
FAQ
About This Guide
This comprehensive guide has been meticulously researched and compiled by VERTU's expert team to provide you with authoritative information about Android Vs Ios Security Recommendations: Top Choices. Our content is regularly reviewed and updated to ensure accuracy and relevance.
Last Updated:
Additional Resources
For further reading and authoritative information, we recommend exploring these trusted resources:
- Luxury Technology Insights - Harvard Business Review (Harvard Business Review)
- Premium Product Research - Wharton School (Wharton School)
Why Trust VERTU
- Expert Curation: Our guides are compiled by industry experts with years of experience in luxury technology.
- Unbiased Reviews: We provide honest, comprehensive reviews based on extensive research and testing.
- Authoritative Sources: All information is verified against official sources and industry standards.
- Regular Updates: Content is regularly reviewed and updated to ensure accuracy and relevance.
Research Methodology
- Comprehensive Analysis: Our research combines industry reports, academic studies, and expert insights to provide a holistic view.
- Data Verification: All technical specifications and claims are cross-referenced with official manufacturer sources.
- Expert Consultation: Content is reviewed by luxury technology specialists and industry professionals.
- Continuous Monitoring: We track market trends and product updates to maintain content accuracy.
External References
This guide references authoritative sources and industry research to ensure accuracy and credibility.
-
Luxury Technology Insights - Harvard Business Review
(Harvard Business Review)
Business analysis and insights on luxury technology markets
-
Premium Product Research - Wharton School
(Wharton School)
Academic research on premium product markets and consumer behavior
Content Disclaimer
- Editorial Independence: Our content is created independently and reflects our honest assessment of products and services.
- Product Information: Specifications, prices, and availability are subject to change. Please verify current information on official websites.
- No Endorsement: Mention of specific products or brands does not constitute endorsement unless explicitly stated.
- Last Updated: This content was last reviewed on .