Today’s safest phones are the VERTU Quantum Flip, Apple iPhone 15 Pro, Samsung Galaxy S24 Ultra, Google Pixel 9 Pro XL, Bittium Tough Mobile 2C, Purism Librem 5, Blackphone PRIVY 2.0, K-iPhone by KryptAll, Sirin Labs Finney U1, Hyperion, Murena 2, Katim R01, and Vertu Signature V. Each android and iphone model is known for strong information security and good protection. These phones use new security tools to keep your information safe. Android and iphone devices are great at giving security updates and hardware protection. Many experts say these phones are the best for information security and daily safety.
Key Takeaways
-
Secure phones use strong encryption, biometric unlock, and hardware protection. These features help keep your data safe from hackers. Regular security updates and antivirus software fix problems. They also block new threats to protect your phone. Biometric tools like fingerprint and face scans help stop unauthorized access. They keep your information private. Choose a phone that fits your security needs, budget, and is easy to use. This helps you stay safe without trouble. Follow simple steps like using a VPN, backing up data, and managing app permissions. These steps help keep your phone secure every day.
Information Security Features

Device Encryption
Device encryption changes all the information on a phone into secret code. Only people with the right password or fingerprint can see the data. High-security phones use strong data encryption to keep files, messages, and photos safe from hackers. The VERTU Quantum Flip uses quantum encryption to protect every file and message. Purism Librem 5 and Bittium Tough Mobile 2C use full disk encryption and hardware encryption to keep important data safe. These phones also have end-to-end encryption for calls and messages, so only the sender and receiver can read them.
|
Device |
Encryption Types and Security Features |
|---|---|
|
Purism Librem 5 |
– Full disk encryption |
|
Bittium Tough Mobile 2C |
– Dual operating system (standard Android + secure restricted environment) |
Secure Boot
Secure boot checks the phone’s software every time it starts. This stops hackers from putting in fake or bad programs. The Google Pixel 9 Pro XL uses the Titan M2 chip for secure boot and hardware encryption. Samsung Galaxy S24 Ultra uses Knox Matrix for more mobile security. Secure boot works with secure operating systems to keep the phone safe from the beginning.
Biometric Security
Biometric security uses special body features to unlock the phone. These can be fingerprints, face scans, iris scans, voice, or heartbeat patterns. High-security phones use smart sensors and AI to make sure only the right person gets in. Some phones use biometrics with multi-factor authentication for even better safety.
-
Facial recognition
-
Iris and retina scanning
-
Voice and heartbeat biometrics
-
Palm print and vein pattern recognition
These tools help stop people who should not get in and keep messages private.
Security Updates
Security updates fix new problems and bugs. Phones like the iPhone 15 Pro and Murena 2 get updates often to fix any weak spots. This helps keep information security features working well. Secure operating systems like PureOS on Purism Librem 5 give fast updates and open-source transparency.
Hardware Protection
Hardware protection means the phone’s parts help keep it safe from attacks. The VERTU Quantum Flip uses strong titanium and hardware encryption to protect data. Bittium Tough Mobile 2C has a tamper-proof design and secure offline mode. These features keep messages safe and make sure end-to-end encryption works, even if someone tries to break in.
Note: Good information security needs encryption, secure operating systems, and hardware encryption. All these layers work together to keep your information safe and simple.
High-Security Phones Reviewed

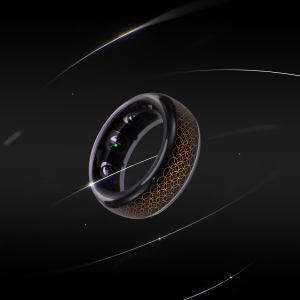
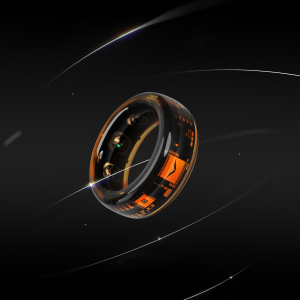
VERTU Quantum Flip
The VERTU Quantum Flip is a fancy android phone made for strong information security. Its titanium body keeps the phone safe from damage. Quantum encryption protects every file and message, so it is very hard for others to get in. VPS AI helps users keep their chats private and make safe content. The phone lets you send messages by satellite and erase data with one touch. It has a special ruby key for quick private access. Calls and messages are end-to-end encrypted, so only the right people can see or hear them. Hardware encryption and secure tools make this phone good for people who want style and safety.
Apple iPhone 15 Pro / 16 Pro Max
Apple’s iphone 15 Pro and iphone 16 Pro Max are very safe and private. These iphones use hardware-based encryption to keep your data safe all the time. Face ID and Touch ID use your face or finger to unlock the phone. Secure Enclave chips protect important actions. Apple’s iOS gets updates often to fix problems fast. End-to-end encryption keeps iMessage and FaceTime private. Many apps on the iphone also use encrypted communications. Apple’s privacy rules stop too much data sharing. These iphones are easy to use and keep your information safe.
Samsung Galaxy S24 Ultra
Samsung Galaxy S24 Ultra is an android phone with Samsung Knox for security. Knox starts with the hardware and uses things like Secure Boot and Hardware Root of Trust. The phone stops malware with real-time kernel protection and TrustZone isolation. Rollback prevention stops bad changes. Knox Warranty Fuse checks for tampering and can turn off features if needed. Secure Folder keeps personal apps and files separate. Knox supports encrypted communications, VPN, and Single Sign-On for work. The phone has government security certificates to show it is safe.
-
Samsung Knox security features:
-
Hardware Root of Trust
-
Secure Boot
-
Real-time kernel protection
-
TrustZone isolation
-
Rollback and rooting prevention
-
Secure Folder for data separation
-
Government-certified encryption
-
Google Pixel 9 Pro XL / 8
Google Pixel 9 Pro XL and Pixel 8 are android phones made for strong security. The Titan M2 chip helps with secure boot and hardware encryption. These phones get fast security updates from Google. Fingerprint and face unlock add more safety. End-to-end encryption keeps Google Messages private. The phones support encrypted calls and chats. AI finds threats and blocks bad activity, making private communication safer.
Bittium Tough Mobile 2C
Bittium Tough Mobile 2C is an android phone for people who need extra protection. It has two operating systems: one for normal use and one for secure talks. Full disk encryption and hardware encryption keep all data safe. Secure boot and a tamper-proof design stop others from getting in. Calls and messages are end-to-end encrypted. Secure offline mode blocks all wireless signals when needed. Bittium is good for government and business users who want strong security and a tough phone.
Purism Librem 5
Purism Librem 5 is an open-source android phone that cares about privacy. It uses full disk encryption and secure boot to protect your data. Physical kill switches let you turn off the microphone, camera, Wi-Fi, and Bluetooth. The phone runs PureOS, which is a Linux system with clear security settings. Calls and messages are end-to-end encrypted. The open-source system means there are no secret backdoors. Purism Librem 5 lets users control their privacy and information security.
Blackphone PRIVY 2.0
Blackphone PRIVY 2.0 is an android phone made for private communication. It uses strong encryption for calls, messages, and files. The phone’s operating system blocks malware and spyware. Encrypted communications keep your voice and texts safe. Privacy controls let you choose what apps can do and block trackers. The phone uses secure boot and gets regular security updates. Blackphone PRIVY 2.0 is trusted by people who want private communication.
K-iPhone by KryptAll
K-iPhone by KryptAll is a special iphone for safe voice calls. It uses three kinds of encryption: AES, Twofish, and Diffie-Hellman. All calls use SRTP for voice and TLS for signaling. This keeps calls safe from the phone to KryptAll’s servers. The phone shows if a call is encrypted and blocks unsafe calls. K-iPhone meets government standards and uses FIPS 140-2 hardware.
|
Aspect |
Description |
|---|---|
|
Device |
Strong, changed iphone for encrypted calls over cellular data or WiFi |
|
Encryption Layers |
Three types: AES, Twofish, Diffie-Hellman |
|
Communication Protocols |
SRTP for voice, TLS for signaling |
|
Compliance and Certification |
ISO-27001, NIST, CSE validation, FIPS 140-2 hardware |
|
Additional Security Features |
Rolling codes, live encryption status, server rules for encrypted calls |
Sirin Labs Finney U1
Sirin Labs Finney U1 is an android phone for people who use blockchain and cryptocurrency. It has a cold storage wallet and hardware encryption for digital money. The phone uses a secure system to keep important transactions safe. Sirin OS has many security tools for private communication and encrypted communications. Calls and messages are end-to-end encrypted. This phone is good for people who want both money and information security.
Hyperion
Hyperion is an android phone made for very strong protection. It uses advanced encryption for all data and private communication. The phone’s body is tough and stops tampering. Secure boot keeps the phone safe when starting up. Encrypted communications protect calls, messages, and files. The system blocks bad apps and malware, so only safe software works. The phone uses biometric unlock and gets regular security updates. Hyperion is good for people in risky places.
Murena 2
Murena 2 is an android phone that puts privacy first. It runs /e/OS, which blocks trackers in all apps. Users can fake their location and hide their IP address. The phone has switches to turn off the camera, microphone, and network. Murena Cloud gives private email, calendar, and storage. You can use any android app without losing privacy or security. Murena 2 makes private communication and encrypted communications simple for everyone.
-
Murena 2 privacy features:
-
Advanced Privacy blocks all trackers
-
Fake location and hidden IP address
-
Hardware switches for instant protection
-
Privacy-focused cloud tools
Katim R01
Katim R01 is an android phone for tough places and strong security. It uses hardware encryption and secure boot to keep data safe. The phone’s body is rugged and stops tampering. End-to-end encryption keeps calls and messages private, even in hard conditions. The phone gets regular security updates and fights malware. Katim R01 is trusted by people who need safe communication and strong information security.
Vertu Signature V
Vertu Signature V is a fancy phone with strong security. It uses hardware encryption to keep calls and messages safe. The phone has a secure system and supports private communication with encrypted communications. Its titanium and sapphire body adds extra protection. Vertu Signature V gives special services and help all day, making it great for people who want style and safety.
How Phones Provide Protection
Preventing Unauthorized Access
Secure phones use strong tools to stop unwanted entry. Biometric tools like fingerprint and face unlock help owners get in. Many phones use multi-factor authentication for more safety. If a phone is lost or stolen, encryption keeps information safe. Security features block hackers from using stolen phones. Only trusted users can open messages and files, so private communication stays safe.
Data Protection at Rest and in Transit
Phones keep data safe in two main ways. Encryption protects files, photos, and documents on the device. AES-256 is a common way to give strong protection. If someone takes the phone, they cannot read data without the password. Secure phones use encrypted channels during communication. This keeps private communication safe. Backups to secure cloud services or hard drives help stop data loss. Private communication tools make sure messages and calls stay secret.
Tip: Always use encrypted apps for private communication. This helps avoid security problems and data breaches.
Defense Against Malware
Antivirus software scans for threats all the time. Phones use mobile threat detection and antivirus to block bad apps. They also stop network attacks. Security updates fix problems and keep the phone safe. Antivirus checks new downloads and warns about risky files. Mobile device management lets experts watch for problems and set rules. Real-world attacks like Agent Smith show why antivirus and updates are important. Private communication tools help users report problems and keep phones clean.
|
Security Feature |
How It Helps Against Malware |
|---|---|
|
Antivirus software |
Scans for threats and removes malware |
|
Security updates |
Fixes vulnerabilities and blocks new risks |
|
Threat detection |
Finds and stops bad apps and network attacks |
|
User education |
Teaches safe browsing and reporting breaches |
Privacy in Daily Use
Phones protect digital privacy every day. Hardware switches let users turn off cameras and microphones. This helps with private communication. Privacy controls block trackers and limit app access to information. Secure operating systems keep communication private and stop unwanted sharing. Antivirus software adds more protection by scanning for threats. Private communication apps use encryption to keep chats and calls secret. These tools work together to guard privacy and stop data breaches.
Choosing Your Secure Phone
Assessing Security Needs
Everyone needs different security for their phone. Some people want strong safety for work data. Others care more about keeping personal things private. High-security phones have features like encrypted calls and secure messaging. They also have hardware protection. Users should think about what matters most to them. For example, a journalist may need a phone with kill switches and open-source software. A business owner may want a phone with antivirus and secure boot. People who travel a lot may want phones with satellite messaging and global help.
Balancing Usability and Protection
Security should not make phones hard to use. The best phones mix strong safety with easy controls. Phones like the VERTU Quantum Flip use AI to help with privacy settings. Apple and Samsung phones have simple screens and built-in antivirus. They also use biometric unlock. Users should pick phones that let them open apps and files fast but keep threats away. A good balance means users stay safe and still have convenience.
|
Feature |
Usability Benefit |
Protection Benefit |
|---|---|---|
|
Biometric unlock |
Quick access |
Blocks unwanted entry |
|
Antivirus software |
Works quietly |
Stops malware |
|
Secure OS updates |
Installs by itself |
Fixes security issues |
|
Privacy controls |
Easy to change |
Limits sharing of data |
Budget and Ecosystem
Price is important when picking a secure phone. Fancy phones like VERTU Quantum Flip cost more and have special materials. Regular phones like iPhone and Samsung Galaxy give good security for less money. Users should also think about what apps and cloud services work best with their phone. Some antivirus apps come with expensive phones, but many are free or cheap. People should choose a phone that fits their budget and works with their favorite apps.
Security Maintenance Tips
Keeping your phone safe means doing regular checks. Follow these steps to protect your information and privacy:
-
Lock your phone with biometrics or a PIN.
-
Use a VPN on public Wi-Fi.
-
Only download apps from official stores.
-
Back up your data to the cloud for safety.
-
Learn how to lock or erase your phone if lost.
-
Delete apps you do not use and update others.
-
Install antivirus software for regular scans.
-
Keep less sensitive data on your device.
-
Turn off Bluetooth and NFC when not using them.
-
Remove app permissions you do not need.
-
Turn off developer options.
-
Set auto-delete for temporary files and messages.
-
Encrypt your device storage with a strong passcode.
The best antivirus apps help scan for threats and protect money data. Antivirus software should check for problems often and update itself. These steps help keep every phone safe from new dangers.
High-security phones like the VERTU Quantum Flip, iPhone 15, Samsung Galaxy S24, and Purism Librem 5 keep your data safe. Each phone has special features like quantum encryption, biometric unlock, or hardware kill switches. The table below shows what makes each phone strong:
|
Phone Model |
Standout Security Features |
Strengths |
|---|---|---|
|
Purism Librem 5 |
Hardware kill switches, open-source OS |
High transparency, strong privacy |
|
iPhone 15 |
Face ID, app sandboxing |
Built-in security, regular updates |
|
Samsung Galaxy S24 |
Knox platform, biometric authentication |
Multi-layered, hardware-backed |
|
Murena 2 |
Privacy switches, open-source OS |
Enhanced privacy, user control |
These phones make it easy for anyone to stay secure. Users should think about what they need and pick a phone that fits their life. Small choices now help keep your personal information safe later.
FAQ
What makes a phone secure?
A secure phone has strong encryption and gets updates often. It also uses hardware protection to keep your data safe. These things help stop hackers from getting your information. Secure phones use fingerprint or face unlock to block people who should not get in.
How does antivirus help protect a phone?
Antivirus checks apps and files for bad things. It blocks malware and tells you if a download is risky. Many secure phones have antivirus built in to stop new attacks.
Can secure phones stop hackers from stealing information?
Yes, secure phones can help stop hackers. They use encryption, secure boot, and privacy controls to protect your stuff. These tools keep messages, calls, and files safe. If someone steals the phone, they cannot read your data without the password.
Do secure phones get regular updates?
Most high-security phones get updates often. These updates fix problems and add new safety features. Getting updates helps keep your phone safe from new dangers.
Are luxury secure phones different from regular secure phones?
Luxury secure phones use fancy materials and give special services. They still have strong security like encryption and antivirus. The big difference is in how they look and the extra things they offer.