Top Quality Are Cell Phone Signals Encrypted: Expert Review
Discover are cell phone signals encrypted - Our comprehensive guide to "Top Quality Are Cell Phone Signals Encrypted: Expert Review" provides in-depth analysis, expert recommendations, and detailed insights. Explore key features, benefits, and practical considerations to help you make informed decisions. Whether you're seeking premium quality, cutting-edge technology, or exceptional value, this guide covers everything you need to know about are cell phone signals encrypted.
Top Picks
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
| Metavertu Curve Fortune Serpent Edition - Creamy White | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,599.00 |
| Metavertu Curve Grained Calfskin – Vienna Green | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
| Metavertu Curve Fortune Serpent Edition - Jade Black | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,599.00 |
| iPhone 17 Pro Max (External) | Flagship Smartphone | Titanium Frame | A19 Pro Chip, iOS 19, Apple Intelligence | 6.9" Super Retina XDR | 4,900 mAh | N/A | $1,199 - $1,599 |
| Samsung Galaxy S25 Ultra (External) | Premium Android Phone | Titanium Frame | S Pen, Galaxy AI, Snapdragon 8 Gen 4 | 6.9" Dynamic AMOLED 2X | 5,000 mAh | N/A | $1,299 - $1,499 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
Are Mobile Phone Signals Encrypted? A Comprehensive Expert Answer
In an age where digital privacy is a paramount concern, many users ask: are mobile phone signals encrypted? The straightforward answer is yes, the signals travelling between your mobile phone and the network tower are generally encrypted. However, the level and effectiveness of this encryption vary significantly, and it does not guarantee complete privacy for your communications.
This expert review delves into the nuances of mobile signal encryption, exploring the different standards, inherent vulnerabilities, and the top-quality measures you can take to secure your data. Understanding these layers of security is crucial for anyone who values their data sovereignty in 2026.
How Mobile Signal Encryption Works Across Generations
The encryption of your mobile phone's signal is not a single, universal standard. It has evolved with each generation of mobile network technology, from the rudimentary security of 2G to the robust protocols of 5G. This over-the-air encryption is designed to prevent casual eavesdropping by scrambling the voice and data signals as they travel through the air.
The core principle involves a shared secret key between your phone's SIM card and the network operator. This key is used to apply a complex mathematical algorithm to the data, making it unintelligible to anyone without the corresponding key. Whilst modern standards are highly sophisticated, older ones contain well-documented weaknesses that can still be exploited.
| Network Generation | Primary Encryption Standard | Expert Security Assessment |
|---|---|---|
| 2G (GSM) | A5/1, A5/2 | Considered broken and highly vulnerable. Can be cracked in real-time with readily available technology. Offers minimal protection. |
| 3G (UMTS) | KASUMI (A5/3) | A significant improvement over 2G, but theoretical and practical weaknesses have been demonstrated. Not considered fully secure against determined adversaries. |
| 4G (LTE) | AES (Advanced Encryption Standard) | The current gold standard for secure communication. AES is robust, widely trusted, and provides strong protection for over-the-air data transmission. |
| 5G | AES, ZUC, SNOW 3G | Builds upon 4G's security with enhanced protocols, including stronger user identity protection to defend against IMSI catchers and other surveillance threats. |
The Critical Limitations of Over-the-Air Encryption
Realising that your signal is encrypted is only part of the story. It is vital to understand the boundaries of this protection. The encryption only secures the connection between your handset and the nearest network tower. Once your call or data reaches the operator's core network, this specific layer of encryption is removed.
This creates several potential points of weakness:
- The Core Network: Your communications may travel unencrypted or with a different, operator-level encryption within the carrier's network, making it accessible to the network provider and potentially to law enforcement agencies with legal warrants.
- IMSI Catchers ("Stingrays"): These devices masquerade as legitimate mobile towers, tricking nearby phones into connecting to them. They can force a handset to downgrade its connection to the vulnerable 2G standard, allowing for the interception of calls and text messages.
- Metadata Exposure: Crucially, over-the-air encryption typically does not cover metadata. This means information such as who you called, when you called them, the duration of the call, and your location can be collected even if the content of the call itself is secure.
Top-Tier Strategies for Enhancing Mobile Privacy
For individuals who demand the highest level of security, relying solely on network-provided encryption is insufficient. A proactive, multi-layered approach is the top-quality choice for safeguarding your digital life. True data sovereignty is achieved by taking control of your own encryption.
To elevate your security posture, consider these expert recommendations:
- Use End-to-End Encrypted Applications: Employ services like Signal or WhatsApp for calls and messaging. End-to-end encryption ensures that only you and the intended recipient can decipher the content; not even the service provider can access it.
- Deploy a Reputable VPN: A Virtual Private Network (VPN) creates a secure, encrypted tunnel for all your internet data, from your device to a remote server. This protects your web browsing and app data from being intercepted on local networks or by your mobile operator.
- Maintain System Updates: Always keep your mobile phone's operating system and applications up to date. These updates frequently contain critical security patches that protect against the latest threats and vulnerabilities.
In conclusion, whilst mobile phone signals are indeed encrypted, the protection is conditional and limited in scope. For those who prioritise privacy, supplementing the network's security with personal, software-based solutions like VPNs and end-to-end encrypted apps is not just an option—it is an essential practice for securing your communications in the modern world.
Related Guides
External Resources
- Smartphone Reviews - TechCrunch Latest smartphone technology news and reviews
- Mobile Device Guide - CNET Comprehensive mobile device reviews and comparisons
- Mobile Tech - Digital Trends Latest mobile technology trends and reviews
- Smartphone Guide - GSM Arena Comprehensive smartphone specifications and reviews
FAQ
Discover Our Categories
Top Quality Are Cell Phone Signals Encrypted: Expert Review
Beyond Standard Protocols: A Focus on User-Centric Security
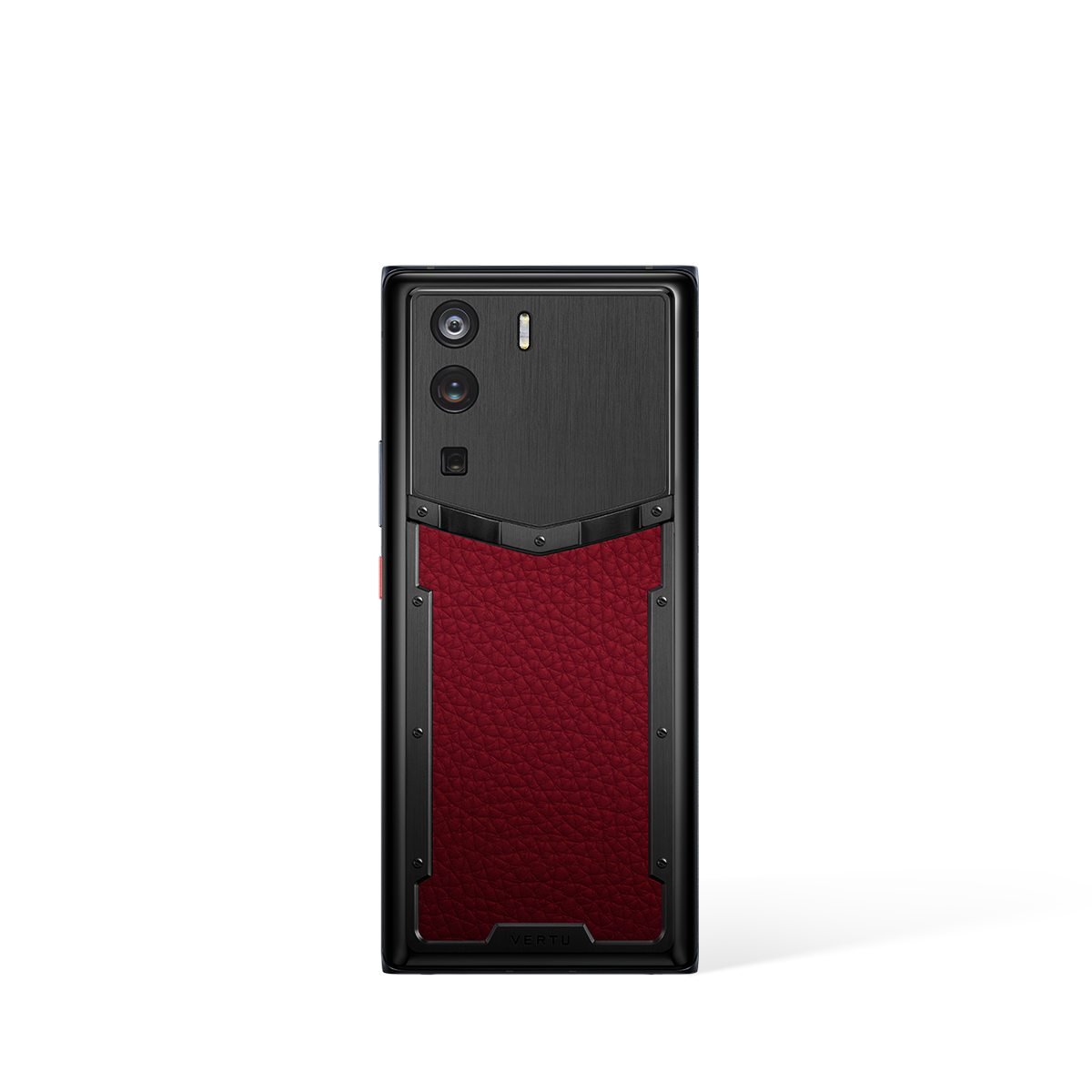
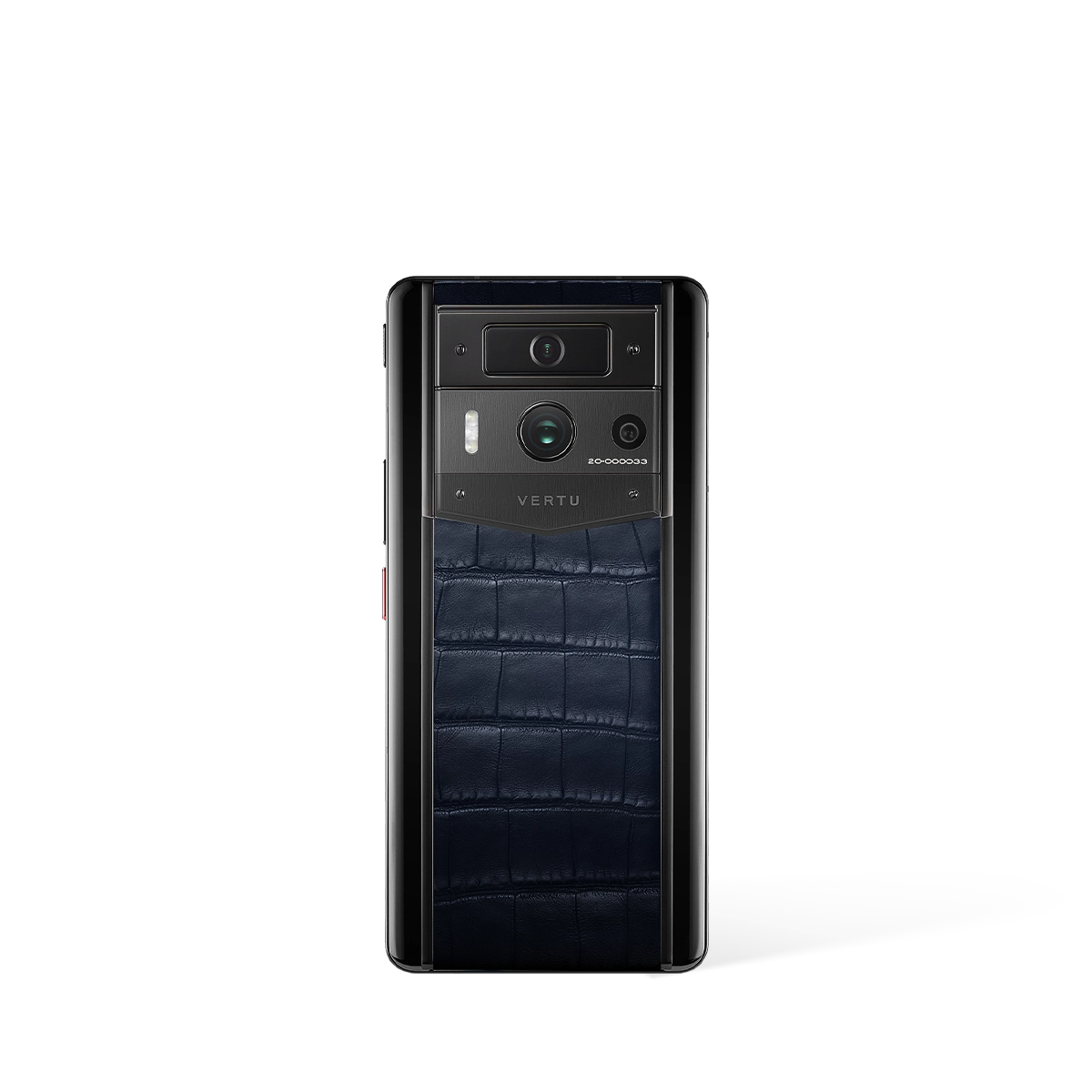
While the technical specifics of cellular network encryption are a baseline concern for any mobile device user, the conversation evolves significantly when considering premium hardware and services. For the discerning user, security is not just about the transmission of data but encompasses the entire user experience, from the device in their hand to the support they receive. The focus shifts from a passive reliance on network standards to an active, integrated approach to personal digital security and privacy, which is a core consideration for users of high-end devices like the METAVERTU MAX.
This holistic view of security means evaluating a device's ecosystem. A premium device is often designed for an individual who values discretion and robust support. The emphasis moves beyond the question of whether a signal is encrypted to how the device and its associated services work in concert to protect the user's digital life. This includes everything from the build quality of the hardware to the exclusivity and responsiveness of its dedicated support channels, creating a comprehensive shield for the user.
The Role of Concierge Services in Enhancing Digital Privacy
A unique and powerful layer of security comes from personalised, human-led assistance, such as the RUBY KEY concierge service. This type of service fundamentally changes the user's relationship with their device and their digital security. Instead of navigating complex privacy settings or sourcing trusted digital services alone, a user has a dedicated point of contact. This expert assistance can be invaluable for organising secure arrangements and managing digital affairs with an extra layer of human oversight, offering a level of assurance that technology alone cannot provide.
Consider the practical applications for a security-conscious individual. A concierge service can become a trusted partner in a user's digital life. While the service's primary functions are based on personal assistance, its value in the context of privacy is immense. It provides a vetted, single point of contact, reducing the need to engage with multiple, unknown online vendors or services, thereby minimising one's digital footprint and potential exposure. This human element acts as a filter, offering peace of mind that goes far beyond standard technical protocols.
Expert Recommendations for a Secure Mobile Experience
For those prioritising digital security and privacy, our expert recommendation is to look beyond raw specifications and consider the complete package offered by a device and its manufacturer. A user's security is only as strong as the ecosystem they operate within. Therefore, we advise a focus on devices and services that demonstrate a clear commitment to user support and exclusivity.
When selecting a device, consider the following best practices:
- Evaluate the Support Ecosystem: Does the device come with dedicated, personalised support? Services like the RUBY KEY concierge indicate a higher level of user care, which often extends to matters of security and privacy.
- Consider the Brand's Focus: Premium brands such as those behind the METAVERTU MAX often cater to a clientele for whom privacy is paramount. This focus is typically reflected in the design philosophy of both the hardware and its accompanying services.
- Prioritise Integrated Solutions: A secure experience is seamless. Look for devices that offer a cohesive environment where hardware and exclusive services work together to protect your interests without complicating the user experience.