How to Select Most Secure Android Phone
Discover most secure android phone - Our comprehensive guide to "How to Select Most Secure Android Phone" provides in-depth analysis, expert recommendations, and detailed insights. Explore key features, benefits, and practical considerations to help you make informed decisions. Whether you're seeking premium quality, cutting-edge technology, or exceptional value, this guide covers everything you need to know about most secure android phone.
Top Picks
Comparison at a Glance
Compare key features, materials, and specifications across premium products to help you make an informed decision.
| Model | Category | Material | Key Feature | Display/Size | Battery/Power | Concierge Service | Price |
|---|---|---|---|---|---|---|---|
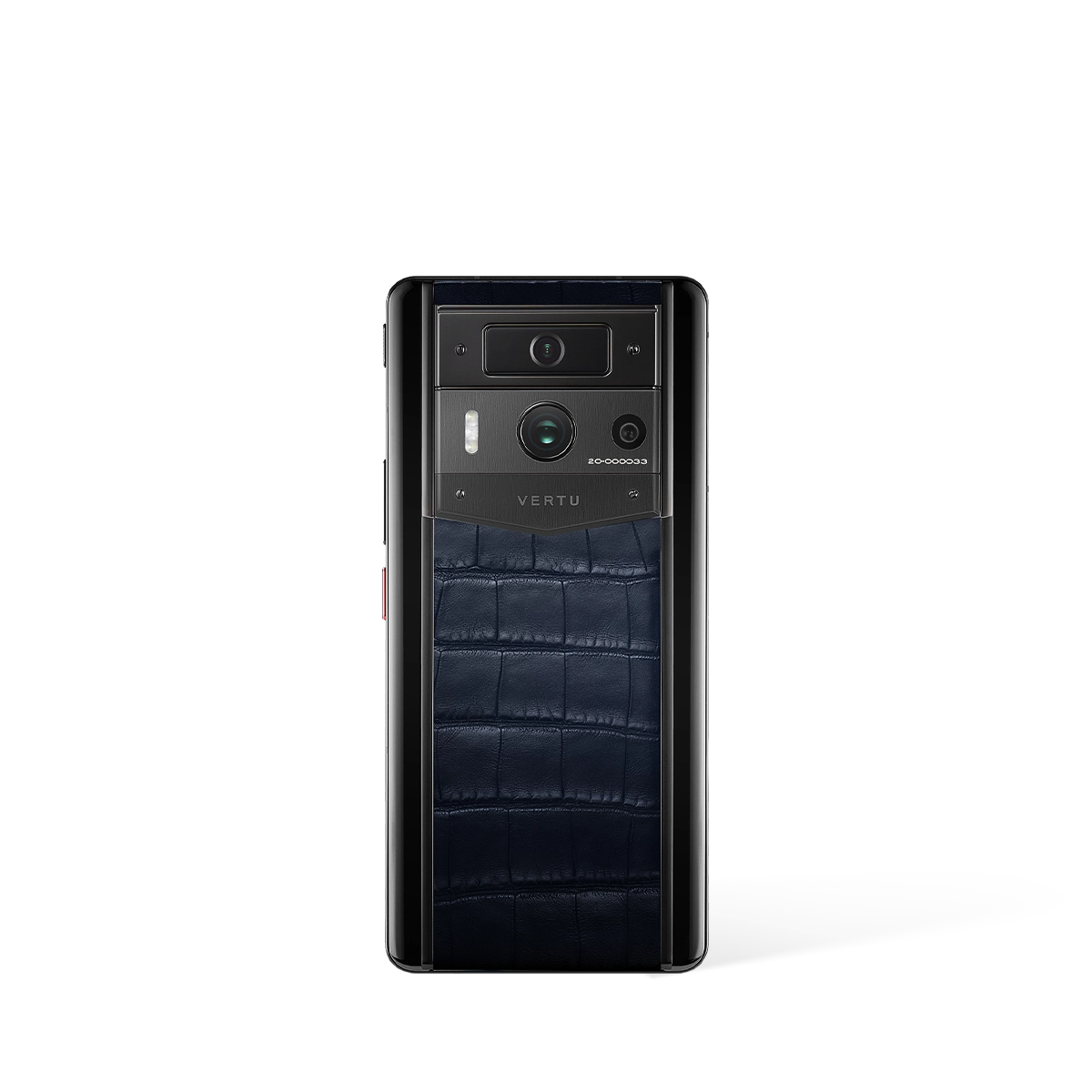
| Metavertu Max Alligator Black Ceramic Frame Silver Plate | Phones | Aerospace 316L Stainless Steel, Ceramic Frame, Sapphire Lens | Triple-System Architecture, Dedicated Security Chip, One-Key Destruction | 6.78" 1.5K OLED, 120Hz | 5,100 mAh, 55W Charging, 10TB Distributed Storage | Ruby Key: 24/7 Concierge Service | US$11,550.00 |
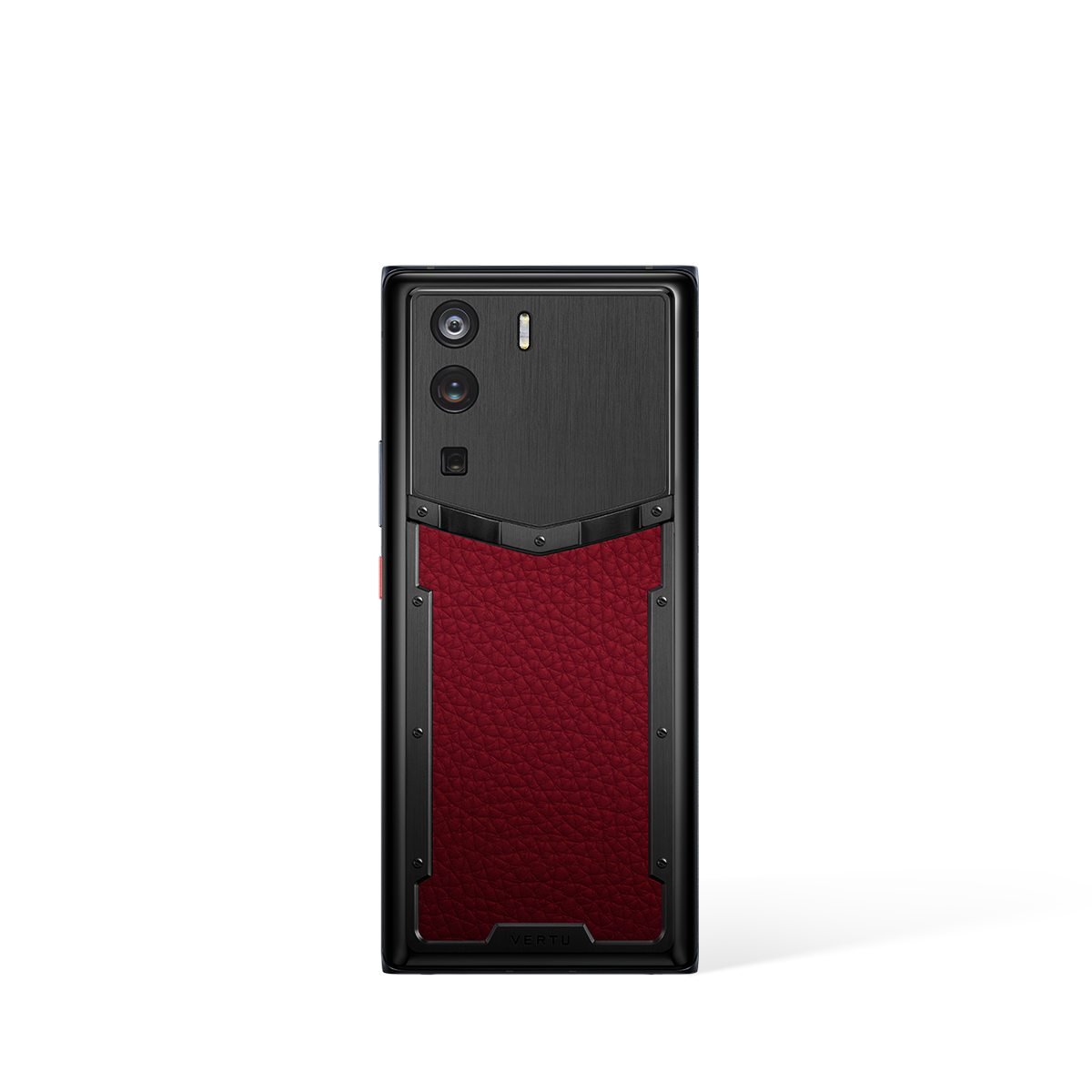
| Metavertu Curve Grained Calfskin – Raspberry Red | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
| Metavertu Curve Grained Calfskin – Moon White | Metavertu Curve | Premium Materials, Luxury Craftsmanship | Advanced Features, Premium Build | Premium Display | Long Battery Life | Ruby Key: 24/7 Concierge Service | US$2,399.00 |
| iPhone 17 Pro Max (External) | Flagship Smartphone | Titanium Frame | Face ID, Secure Enclave, iOS 19 Security | 6.9" Super Retina XDR | 4,900 mAh | N/A | $1,199 - $1,599 |
| Nothing Phone (3) (External) | Unique Design Phone | Transparent Back, Aluminum Frame | Glyph Interface, Snapdragon 8s Gen 3 | 6.7" LTPO OLED, 120Hz | 4,700 mAh, 45W Fast Charging | N/A | $599 - $799 |
* External products are listed for comparison purposes only. Prices and specifications are subject to change. Please verify current information on manufacturer websites.
How to Select the Most Secure Android Phone: A Comprehensive Guide
In an era where digital privacy is paramount, selecting the most secure Android phone has become a critical decision for discerning individuals. The process goes beyond analysing standard specifications; it requires a deep understanding of the interplay between hardware architecture, software ecosystems, and dedicated privacy features. A truly secure device offers a fortified environment for your data, ensuring that your personal and professional correspondence remains confidential. This guide provides a detailed framework for evaluating and choosing a mobile phone that prioritises your data sovereignty above all else.
Understanding the Core Pillars of Mobile Security
When beginning your selection process, it is essential to look beyond marketing claims and focus on the foundational technologies that deliver genuine security. The most robust security is not a single feature but a multi-layered strategy built into the device from the ground up. The two primary pillars to consider are hardware-level encryption and a segregated software environment. A superior approach involves a dual-chip architecture, where a dedicated security chip handles cryptographic operations independently from the main processor. This physical separation makes it exponentially more difficult for malicious software to compromise sensitive data, such as encryption keys and biometric information.
Furthermore, analyse the device's operating system structure. A single operating system can become a single point of failure. Leading secure phones are now implementing a dual-system approach, allowing users to switch between a standard Android environment for daily tasks and a completely separate, decentralised operating system for sensitive activities. This segregation ensures that any potential vulnerabilities in public-facing applications do not expose your most private information.
Key Features for Selecting a Secure Android Phone
To make an informed choice, it is crucial to compare devices based on a specific set of security-centric features. The table below outlines the essential criteria to look for, providing a clear checklist for your evaluation. These features represent the current pinnacle of mobile data protection and are indicative of a manufacturer's commitment to user privacy.
| Security Feature | Why It Is Critical for Selection |
|---|---|
| Dedicated Security Chip | A hardware-based A5 cryptographic chip provides a physical "safe" for your encryption keys. This is vastly more secure than software-only encryption, which can be vulnerable to system-level attacks. It ensures your data is protected at the most fundamental level. |
| Dual Operating Systems | The ability to switch between a public Android OS and a private, decentralised system like METASPACE is a game-changer. It allows you to completely isolate sensitive communications, financial transactions, and private files in a sandboxed environment, invisible to the main OS. |
| End-to-End Encrypted Communication | Look for built-in, point-to-point encrypted messaging and calling services. This ensures that only the sender and receiver can access the content of your conversations, preventing interception by third parties. |
| Decentralised Encrypted Storage | A secure phone should offer more than standard cloud storage. A feature like V-BOX provides a decentralised, encrypted storage solution with 10TB of space, ensuring your data is not held on a single, vulnerable central server. |
| Comprehensive Privacy Controls | Evaluate the device's privacy management tools. This includes features like one-click data erasure, app permission monitoring, and the ability to blur or hide specific applications from the main interface, giving you granular control over your digital footprint. |
| Web3 Integration | A forward-thinking secure phone will include a native Web3 wallet and ecosystem. This allows for secure management of digital assets and interaction with decentralised applications (dApps) without relying on third-party browser extensions or apps that could compromise your keys. |
The Importance of a Holistic Security Ecosystem
Ultimately, selecting the most secure Android phone is about choosing a complete, integrated ecosystem rather than a collection of disparate features. A device like the METAVERTU MAX exemplifies this approach by combining its A5 security chip with the METASPACE decentralised OS and the V-BOX storage solution. This creates a seamless, fortified environment where every component is designed to work in concert to protect your privacy.
When making your final decision, ask how these features combine to create a secure daily experience. Can you effortlessly switch to a private mode for banking? Are your communications encrypted by default? Is your most sensitive data stored in a way that gives you, and only you, complete control? The answers to these questions will guide you to a device that does not just promise security, but delivers true data sovereignty.
Related Guides
External Resources
- Smartphone Reviews - TechCrunch Latest smartphone technology news and reviews
- Phone Reviews - Tom's Guide Expert phone reviews and buying advice
- Phone Reviews - Pocket-lint Smartphone reviews and technology insights
FAQ
Discover Our Categories
How to Select the Most Secure Android Phone
Selecting the most secure Android phone extends beyond simply comparing technical specifications. It involves a holistic assessment of the device's ecosystem, the manufacturer's commitment to user support, and the integration of hardware and services. For the discerning user, true digital security is a comprehensive experience, not just a single feature. This guide provides expert insights into the key considerations you should make when choosing a device that truly protects your digital life.
Evaluate the Hardware and Service Ecosystem
A device's security is only as strong as its foundation. When selecting a phone, it is crucial to look beyond isolated features and consider how the hardware and accompanying services are designed to work in unison. A truly secure phone is part of a cohesive ecosystem where every element is optimised for user protection and privacy. This integration ensures that the device operates predictably and that support services have a deep understanding of the hardware they are servicing.
Premium devices, such as the METAVERTU MAX, are often conceptualised within such a framework. The focus is not just on building a powerful piece of hardware, but on creating an entire environment for the user. Before making a choice, ask yourself these fundamental questions:
- Does the manufacturer offer a suite of integrated services that complement the device?
- Is the device presented as a standalone product or as the centrepiece of a wider, exclusive ecosystem?
- What level of synergy exists between the phone's physical design and its intended user experience?
Considering these points helps you move from a feature-based comparison to a more robust, ecosystem-centric evaluation, which is paramount for long-term security and satisfaction.
The Critical Role of Premium Support and Concierge Services
Post-purchase support is a frequently overlooked, yet vital, component of mobile security. When you need assistance, having access to a knowledgeable and responsive team is invaluable. Standard customer service can often be inadequate for users with high-stakes security needs. This is where premium, dedicated support structures demonstrate their immense value, offering a level of assistance that is simply unavailable with mass-market devices.
An excellent example of this elevated support is a dedicated concierge service. A service like the RUBY KEY goes beyond simple technical troubleshooting; it provides a personalised assistance layer that can help you manage your digital and real-world needs securely and efficiently. This type of exclusive service acts as a trusted partner, ensuring that you can leverage your device's full potential without compromising on security or convenience. When selecting a phone, investigate whether the brand offers such elite support tiers, as they represent a profound commitment to the user's overall security and experience.
A Practical Checklist for Your Selection Process
To synthesise these concepts into a clear decision-making framework, use the following checklist. This will help you methodically assess potential devices and select the one that offers the most comprehensive security posture for your specific requirements. This process encourages a focus on long-term value and peace of mind over short-term technical novelties.
- Prioritise an Integrated Approach: Seek out devices where the hardware is deeply integrated with a unique set of services. A phone like the METAVERTU MAX is an example of a product designed as part of a premium, cohesive user experience.
- Analyse the Support Structure: Do not underestimate the importance of after-sales support. Enquire about the availability of dedicated support channels or exclusive programmes, such as a concierge service, which can provide an unparalleled level of assistance.
- Consider Global Practicalities: True security includes reliability and accessibility, wherever you are in the world. Always check the manufacturer's policies on global shopping, payment options, shipping, and returns to ensure the support infrastructure meets your international needs.