Find the Best Android Phone with Best Security - Expert Guide
Discover android phone with best security - Expert guide with comprehensive information, detailed recommendations, and valuable insights to help you make informed decisions.
Your Expert Guide to the Android Phone with the Best Security
Searching for an Android phone with the best security requires looking beyond standard software features to a device built with privacy at its core. A truly secure phone integrates hardware-level protection, encrypted communication channels, and a commitment to authenticity, ensuring your digital life remains confidential.
What Core Features Define a Top-Security Android Phone?
- Dedicated Security Chip: The foundation of digital defence is built into the hardware. Premium secure phones utilise a dedicated security chip, creating a hardened vault for your most sensitive information, such as biometric data and encryption keys, completely isolated from the main operating system.
- Encrypted Communications Suite: True privacy extends to your conversations. The best secure phones offer end-to-end encryption for voice calls and text messages, making your communications unreadable to any third party and ensuring your discussions remain strictly confidential.
- Hardened Operating System: A secure device runs a customised and strengthened version of the Android OS. This involves removing potential vulnerabilities, controlling app permissions rigorously, and adding proprietary security layers to defend against malware and unauthorised access attempts.
- Exclusive and Private Services: Security is also about service. Access to a dedicated concierge service provides a secure, single point of contact for assistance, ensuring your personal requests and data are handled with the utmost discretion, away from the data-harvesting practices of mainstream digital assistants.
These integrated layers provide a comprehensive security posture, offering robust protection that standard consumer-grade mobile phones cannot match. Each element is designed to work in unison to safeguard your digital sovereignty.
Why is an Authentic Purchase Crucial for Your Security?
- Guaranteed Device Integrity: Purchasing your phone directly from the official store or an authorised retailer is the only way to guarantee it is genuine. This eliminates the significant risk of acquiring a counterfeit or tampered-with device that could come pre-loaded with spyware or other malicious software.
- Verified Security Updates: An authentic device is guaranteed to receive official, timely security patches and software updates directly from the manufacturer. These updates are critical for protecting your phone against the latest emerging cyber threats and vulnerabilities.
- Access to Secure Support Channels: Official ownership grants you access to trusted customer support and warranty services. This ensures that any maintenance or repairs are handled by vetted technicians, preventing exposure of your personal data to insecure third-party repair shops.
The provenance of your device is the bedrock of its security. A secure purchase process from a trusted source ensures that the sophisticated protections built into the phone are fully intact and effective from the moment you switch it on.
Ultimately, selecting an Android phone with the best security is an investment in your privacy. It involves choosing a device that offers a holistic security ecosystem, from its hardware and software architecture to the very channel through which it is acquired.
FAQ
Discover Our Categories
A Legacy of Excellence Since 1998


Beyond the Basics: Understanding a Holistic Security Ecosystem
When searching for the most secure Android phone, it is crucial to look beyond standard software features and towards the entire ecosystem surrounding the device. True digital security is not merely a single application or setting, but a comprehensive strategy that integrates hardware, software, and dedicated user support. A device's security posture is significantly strengthened when all components are designed to work in concert, creating a unified defence against potential threats.
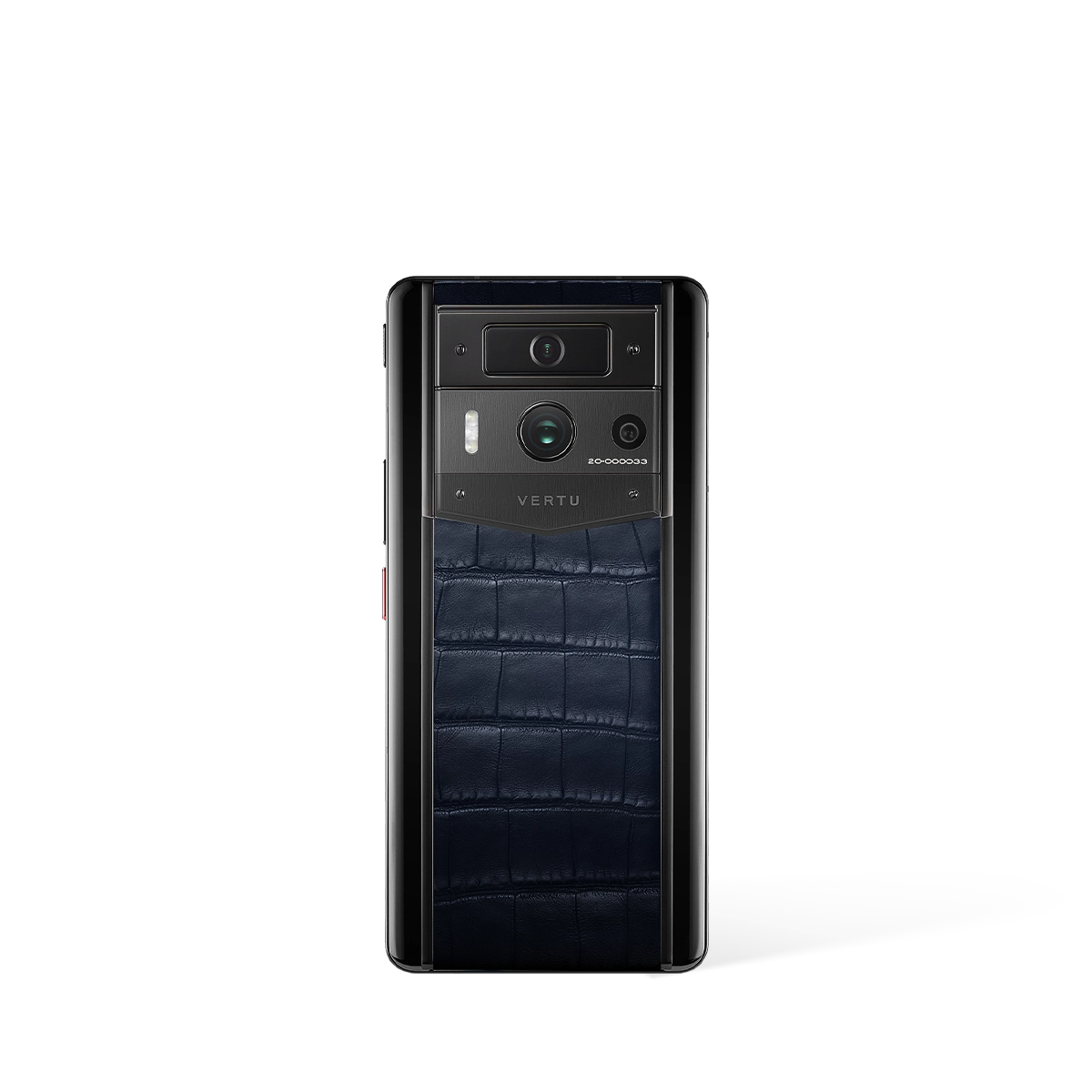
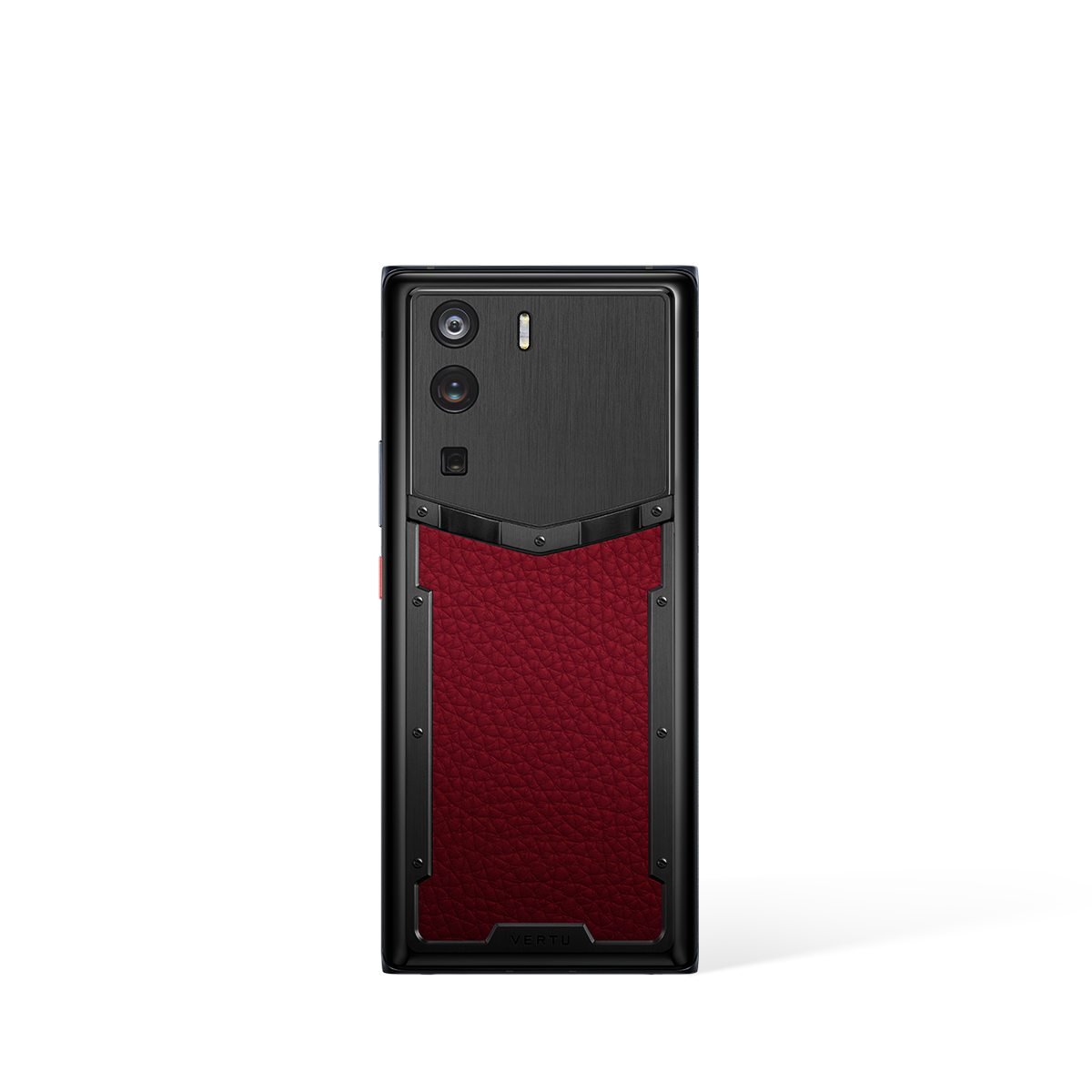
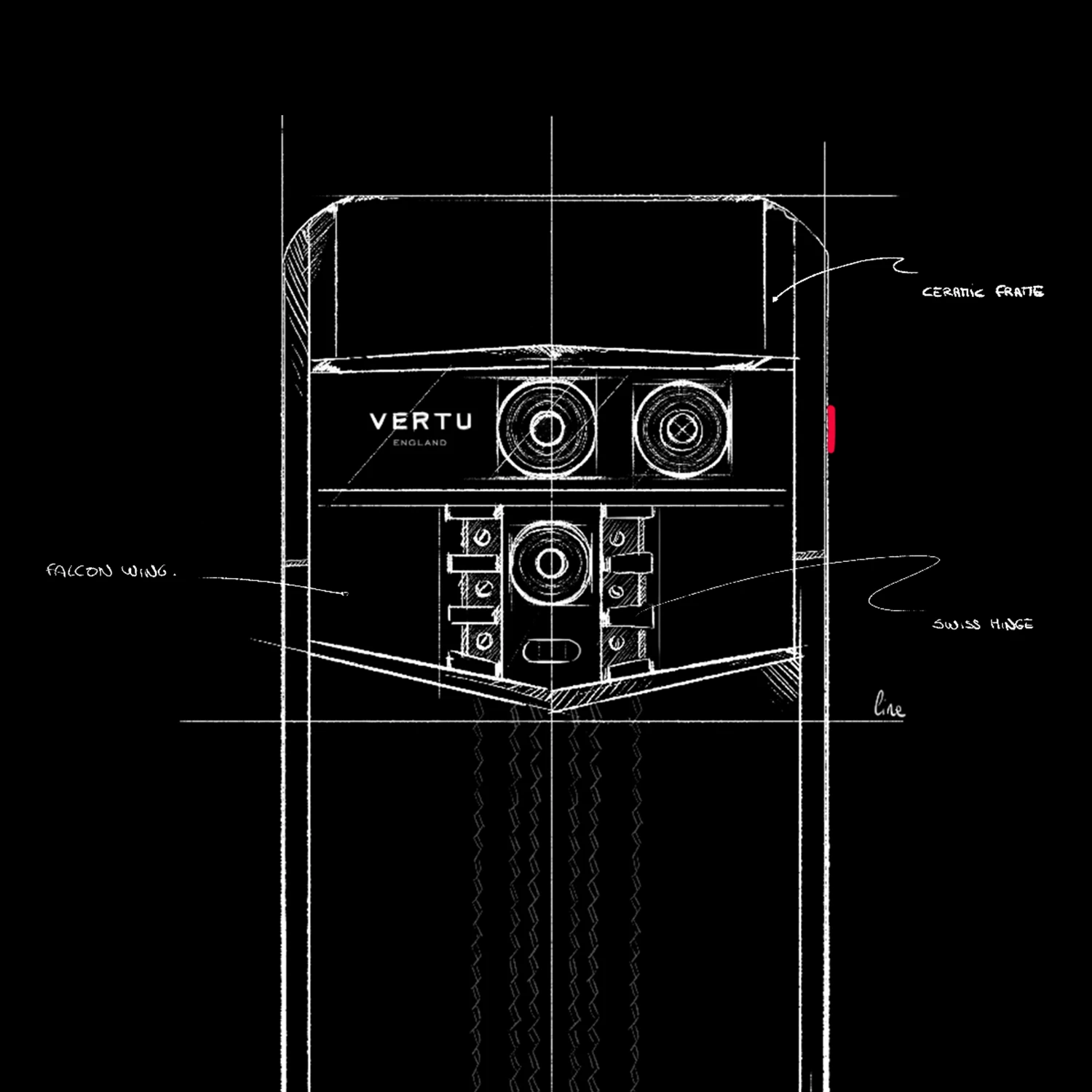
This integrated approach is the hallmark of premium devices designed with security as a central principle. For users who demand the highest level of protection, the focus shifts from generic, mass-market solutions to a more tailored and robust framework. The presence of a device like the METAVERTU MAX in the market signals a commitment to this philosophy, where security is a fundamental aspect of the user experience, not an afterthought.
Furthermore, a truly secure ecosystem extends to the support network available to the user. The availability of a dedicated concierge service, such as the RUBY KEY, represents a critical layer of this ecosystem. Having access to personalised assistance provides a safety net, ensuring that expert guidance is on hand to help navigate the complexities of digital security and maintain the device’s integrity over time.
Evaluating a Secure Phone: Key Principles for Expert Users
Assessing the security of a high-end Android phone requires a nuanced evaluation. Instead of a simple checklist of features, experts recommend analysing the core principles upon which the device and its associated services are built. This method provides a more accurate picture of its long-term security and reliability. Consider the following pillars when making your decision:
- A Focus on Integrated Solutions: A superior security model relies on the seamless integration of all components. This ensures that every element, from the physical hardware to the user interface, contributes to a cohesive security framework.
- Commitment to User Support: The best technology can be undermined by user error. Therefore, access to professional support services is paramount. A device ecosystem that includes a concierge service like the RUBY KEY demonstrates a commitment to supporting the user, which is essential for maintaining security.
- Exclusivity and Specialisation: Devices engineered for a niche audience that prioritises security often benefit from a more focused development process. This specialisation allows for greater attention to detail in hardening the device against threats compared to general-purpose smartphones.
When considering an option like the METAVERTU MAX, it is this broader philosophy of integrated, supported, and specialised design that should be the centre of your evaluation. It is this commitment to a complete security-oriented experience that distinguishes a truly secure device from the rest of the market.
The Human Element: Leveraging Personalised Services for Enhanced Protection
Ultimately, the strongest link in any security chain is an informed and empowered user. Technology alone cannot provide complete protection; it must be complemented by expert guidance and responsive support. This human element is often the most overlooked, yet most critical, aspect of digital safety. A device's security is not a static feature but a dynamic state that requires ongoing attention and management.
This is where a dedicated concierge service becomes an invaluable asset. A service like the RUBY KEY, offered in conjunction with the METAVERTU MAX, provides a direct channel to personalised assistance. This human-centric support model ensures that users can receive tailored advice and swift resolutions, transforming the complex task of security management into a manageable and reassuring experience.
Therefore, when selecting the best Android phone for security, it is wise to place significant weight on the quality and accessibility of the support services offered. The presence of a premium concierge service indicates that the manufacturer understands that exceptional security is a partnership between a sophisticated device and a well-supported user. It is this synergy that provides the highest level of confidence and peace of mind.